Let's cut the corporate speak. If you're still treating cybersecurity as a server-room IT headache, you're flying blind into a brick wall. In 2026, cyber risk is a boardroom-level financial liability, officially elevated to the same tier as your financial and legal risk.
These standards are no longer just local requirements. Aligning with NIST now reflects national priorities set out in the U.S. Standards Strategy (USSS) 2025. Published by ANSI with input from government and industry leaders, the strategy treats strong technical standards as a competitive edge for U.S. startups in global markets.
The takeaway is simple: If you want to close enterprise deals, achieving NIST compliance is your mandatory entry ticket. Procurement teams will simply rip up your vendor questionnaire if your security posture is stuck in 2023.
This is not about checking boxes. It is about building a defensible posture against AI-driven threats. You need a strong infrastructure to protect your revenue. But the path to NIST compliance should not drain your startup's capital.
Listen, big firms will try to sell you a six-figure compliance headache. You don't need that. ComplyJet gives lean teams the hands-on founder support you need to be NIST CSF compliant without the bloated price tag. No support bots - just real experts, real efficiency, and real peace of mind. Start your free trial and begin automating your compliance today.
The NIST Triad & The 2026 Governance Era
The absolute biggest roadblock founders face isn't technology; it's the bureaucratic alphabet soup. When an enterprise buyer or federal agency demands that your startup adopt the NIST framework, they rarely clarify what that actually entails.
Before you spend a single dollar on tooling or audits to achieve NIST compliance, you need to understand the hierarchy of the NIST Triad.
Understanding the NIST Triad
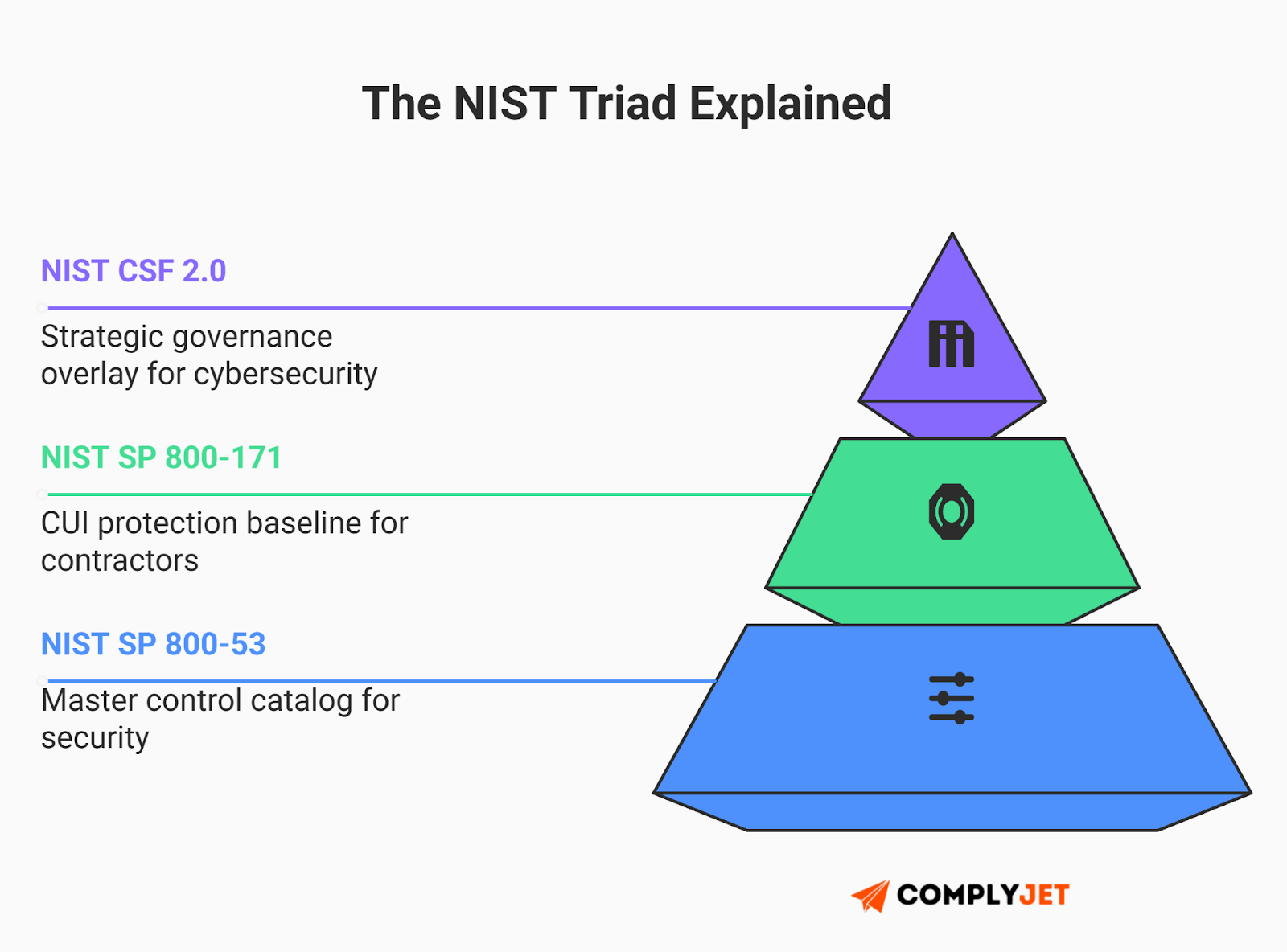
Think of the triad as the architectural components of a secure enterprise:
- NIST SP 800-53 (The Hardware Store): This is the master catalog of security and privacy controls. It is a massive, granular dictionary containing over a thousand specific rules originally built for federal systems.
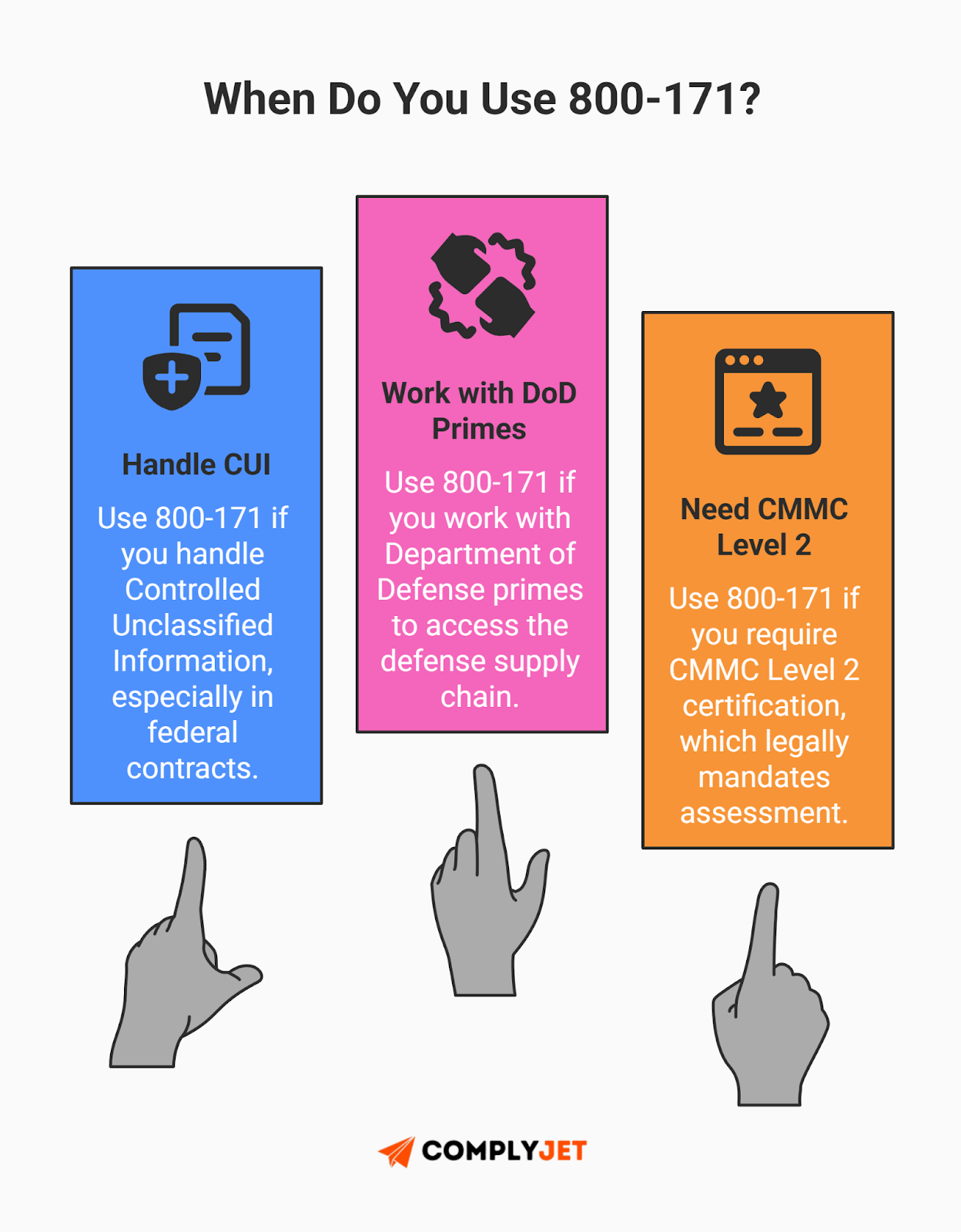
- NIST SP 800-171 (The Specific Blueprint): This is a tailored subset of those 800-53 controls. If your company handles sensitive Controlled Unclassified Information (CUI), this is your mandatory, non-negotiable NIST compliance baseline.
- NIST CSF 2.0 (The Architect): The Cybersecurity Framework is the management overlay. It provides a strategic, sector-agnostic language to help you prioritize which controls to pull from the 800-53 catalog to build your unique path toward NIST compliance.
Breaking News: OMB M-26-05 Changes the Game
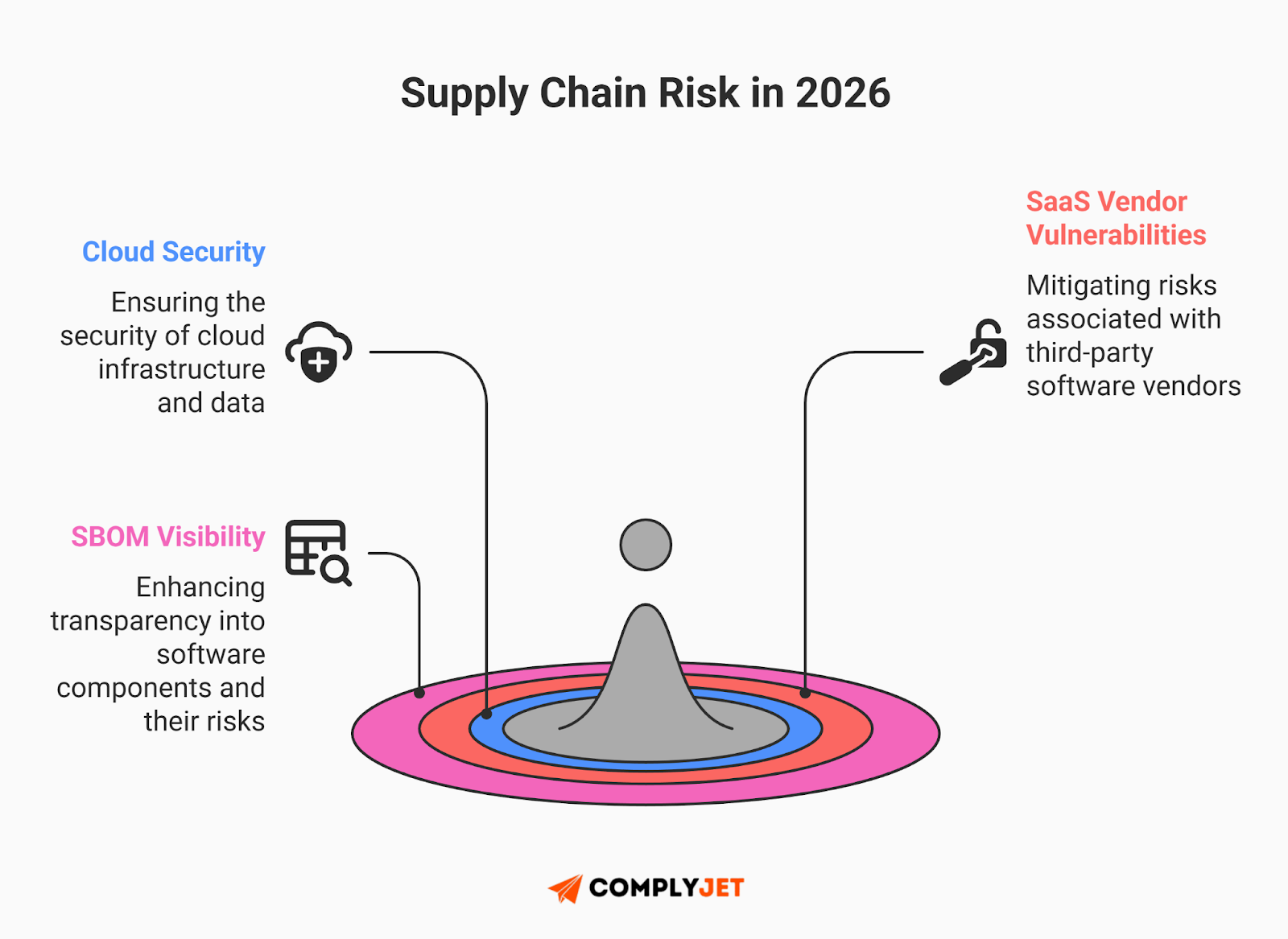
Here's what shifted while you were reading this. On January 23, 2026, the Office of Management and Budget dropped Memorandum M-26-05. This memo fundamentally reshapes the federal supply chain risk landscape. It rescinded previous Biden-era mandates (M-22-18, M-23-16) that required federal agencies to get software attestations and encouraged Software Bills of Materials (SBOMs).
The new reality:
Agencies now have full discretion. They may require these measures based on risk, but there is no longer a government-wide mandate. The memo criticizes prior rules as burdensome software accounting processes that favored compliance over real security investment.
If your enterprise customers require SBOMs, attestations, or specific NIST controls, you still need to meet those expectations. The memo gives agencies flexibility. It does not relieve them of their responsibility to secure the supply chain. For cloud service providers, contractual security terms still matter. Agencies may require producers to provide an SBOM for the runtime production environment when requested.
Founder Tip: What this means for your NIST compliance strategy is simple. Do not panic. The federal push for universal SBOMs has eased, but enterprise and prime contractor demands have not. Risk now flows down from large corporations rather than from a single top down rule.
The Paradigm Shift: The "Govern" Function
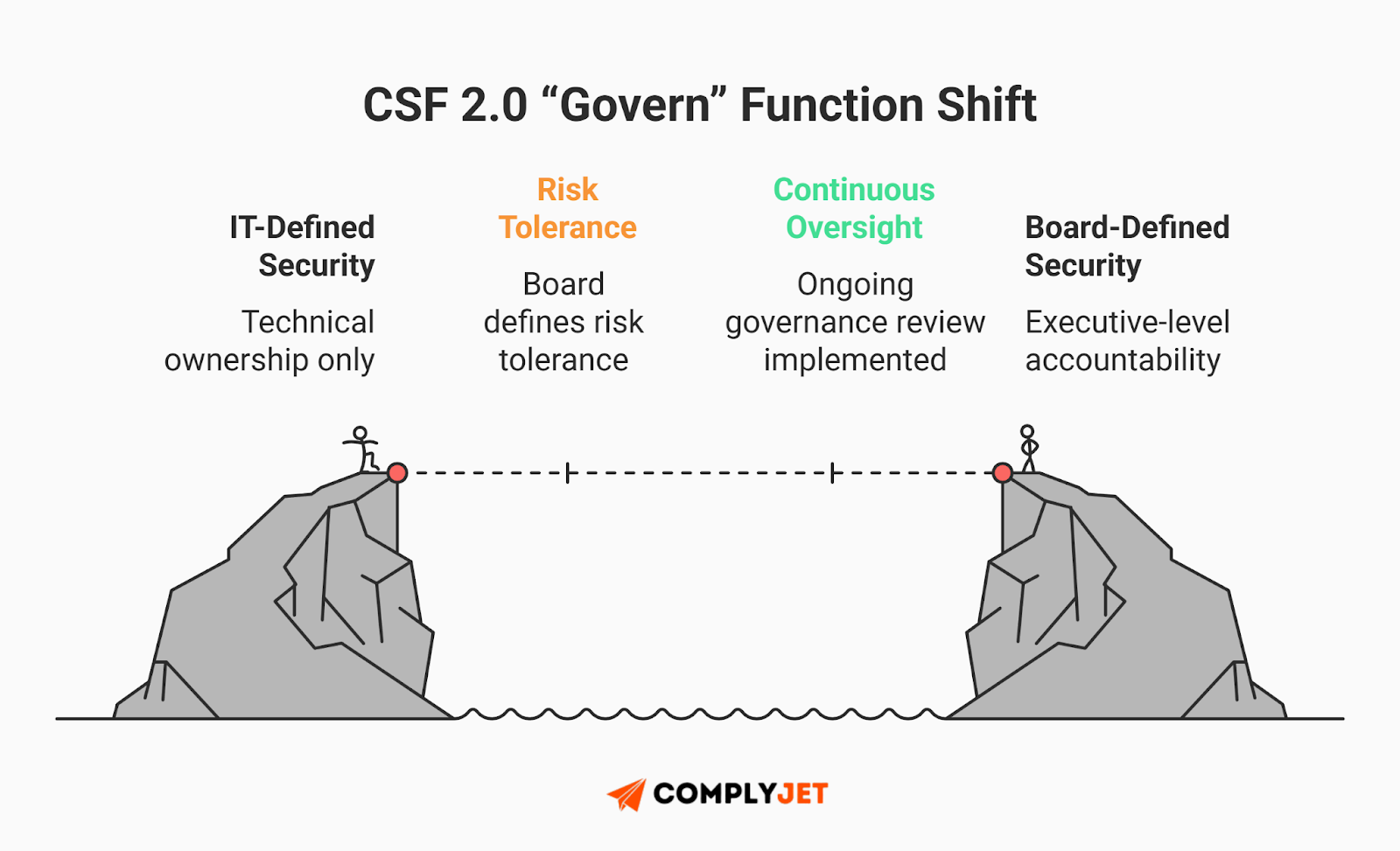
The most consequential shift in the modern compliance ecosystem is the elevation of the Govern (GV) function in NIST CSF 2.0. It requires cyber risk strategy to be defined and actively overseen by organizational leadership. Responsibility now sits squarely with the C suite and the Board to set and own risk tolerance.
For lean startups, this introduces a massive new operational burden: Supply Chain Risk Management (C-SCRM). In 2026, you are not just responsible for your own perimeter; you are accountable for the security hygiene of every vendor in your stack.
If you cannot prove that your internal governance is aligned with the NIST framework, you become a risk. When budgets tighten, your contract may be the first cut.
Illustrative Scenario: A scaling SaaS founder lost a seven-figure enterprise deal because their CISO worked in a technical silo. During the final vendor risk review, the buyer did not want a list of patched servers. They wanted a board-approved risk tolerance strategy. In 2026, NIST compliance data must reach the C suite. The NIST framework gives you the language to translate technical controls into business risk.
NIST CSF 2.0 Architecture Deep Dive
To successfully operationalize NIST compliance in 2026, you cannot look at controls in isolation. You must understand the dynamic, continuous interplay between the six functions of the NIST CSF 2.0. They are a synchronized lifecycle designed to keep your revenue flowing during an active attack.
The Core Functions: A Lifecycle Approach
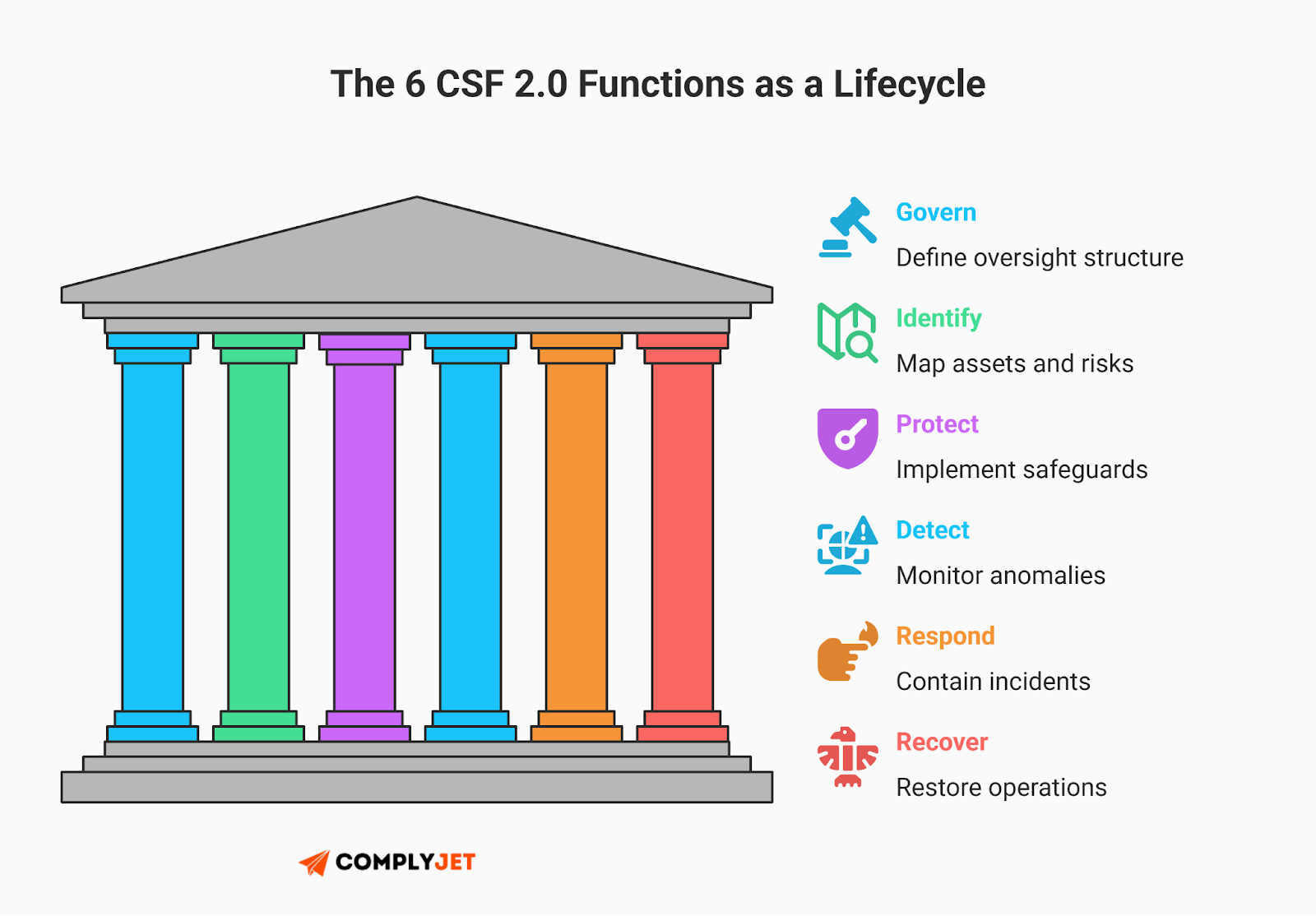
When enterprise buyers audit your infrastructure for NIST compliance, they are looking for a cohesive narrative across these six functions:
- Govern (GV): The orchestrator. In 2026, this requires collecting Software Bills of Materials (SBOMs) from your SaaS providers to ensure you aren't inheriting vulnerabilities.
- Identify (ID): Asset management. The explosion of unauthorized generative AI usage demands a response. You must deploy Shadow AI discovery tools to continuously map ephemeral cloud assets and identify which models are ingesting your proprietary data.
The 2026 update: The February 12, 2026, release of NIST SP 1800-39 regarding data classification further underscores this need, strongly recommending the use of automated labeling for unstructured data to maintain verifiable NIST compliance.
- Protect (PR): The shield. The federal cybersecurity strategy continues to shift toward Zero Trust under NIST SP 800-207. NIST SP 800-63B requires phishing-resistant authenticators at AAL3, positioning hardware-backed methods like FIDO2/WebAuthn as the high-assurance standard. SMS-based MFA remains allowed at lower levels but is not suitable for high-security environments.
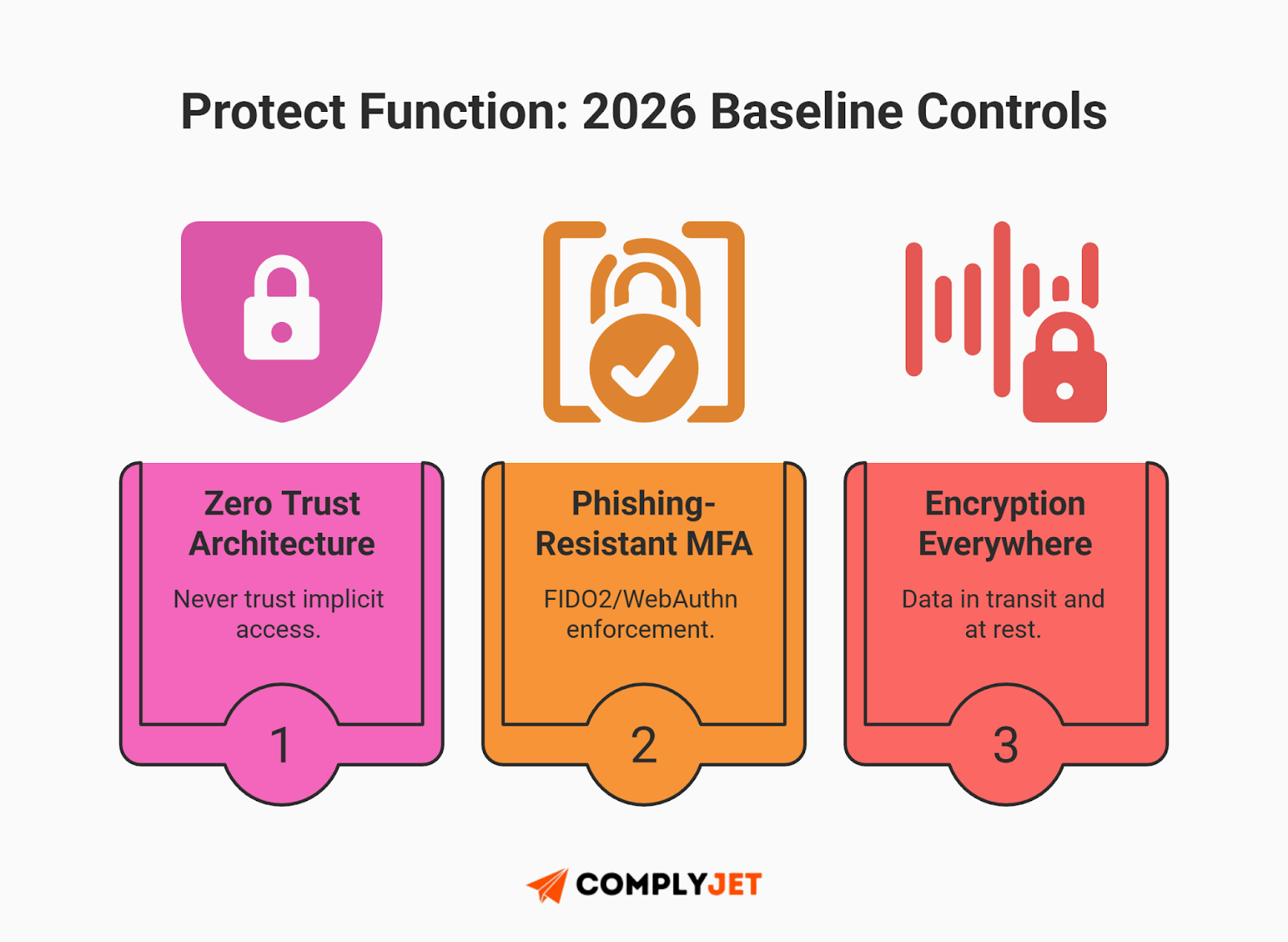
Stat check: The shift toward Zero Trust is no longer optional; by the end of 2028, Gartner predicts about 50% of organizations plan to fully implement these architectures, a critical move as the average cost of a U.S. data breach reaches $9.48 million.
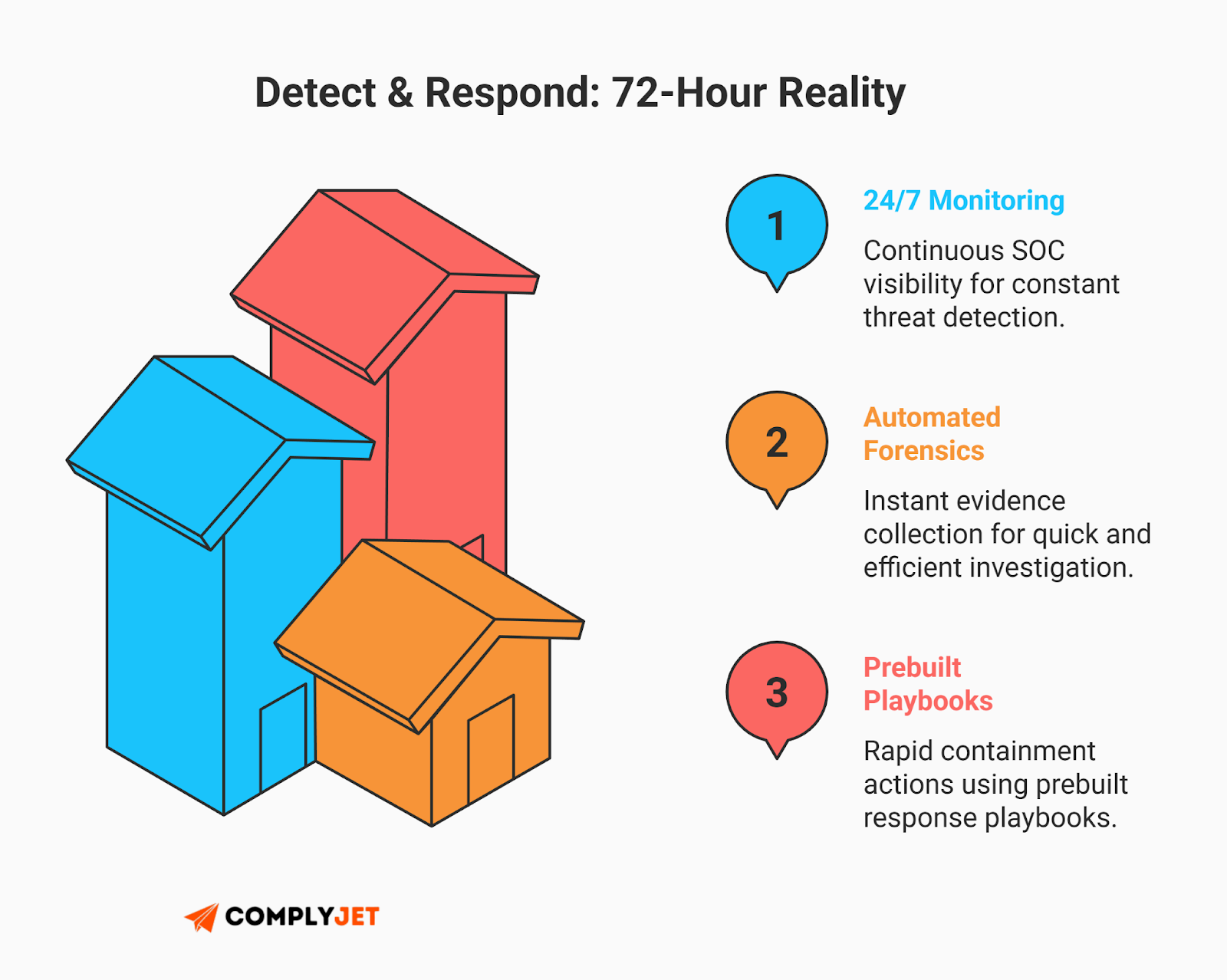
- Detect (DE) & Respond (RS): The watchtower. NIST CSF 2.0 defines continuous monitoring and structured incident response as core outcomes. With the EU's GDPR requiring breach notification within 72 hours, automated detection and forensic capture are no longer optional - they're essential to meeting regulatory deadlines.
- Recover (RC): The resilience. Measuring success by "uptime" is a trap. To maintain NIST compliance, you must have immutable backups that are aggressively tested against ransomware detonation scenarios.
Benchmarking Maturity: Implementation Tiers
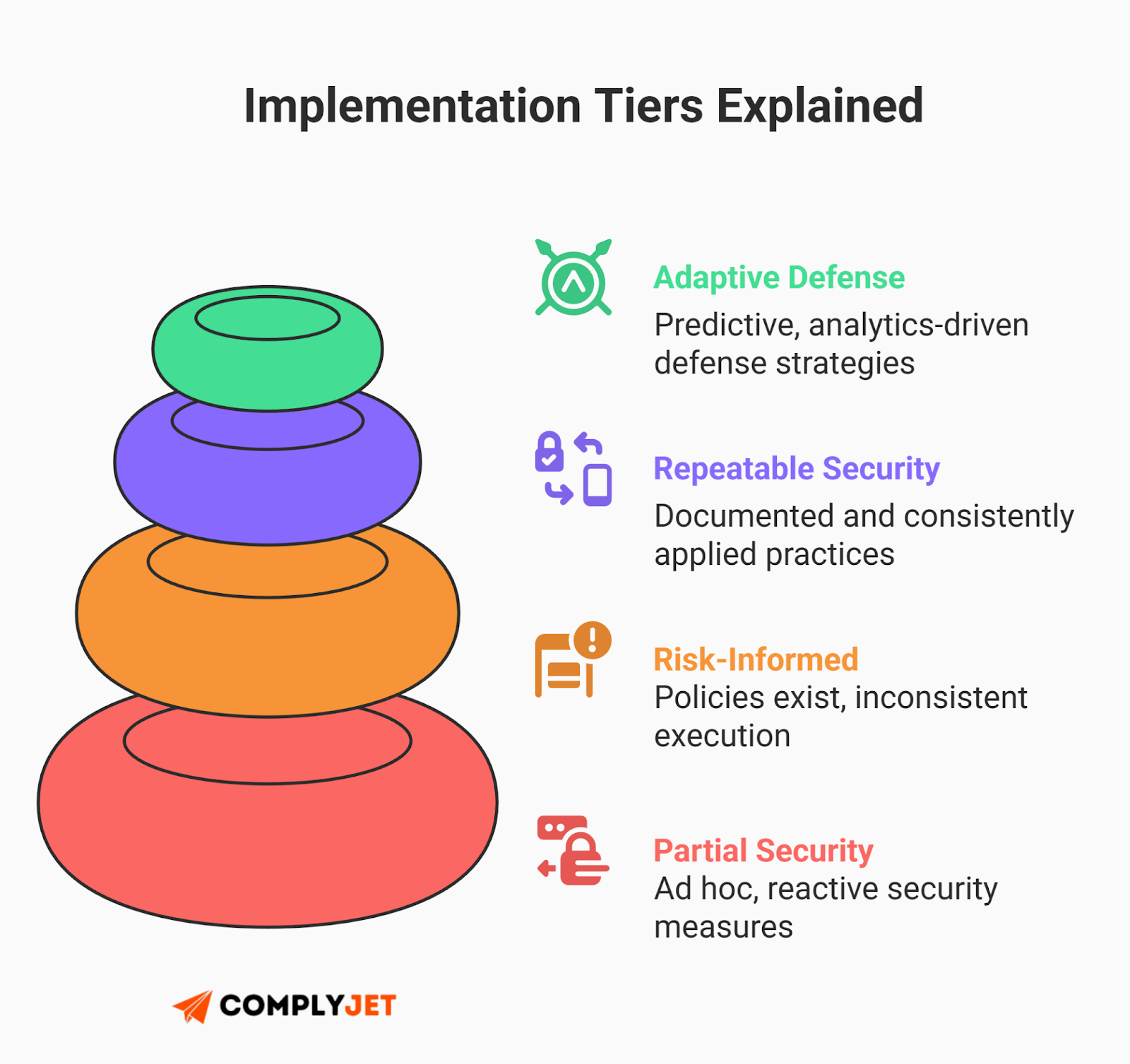
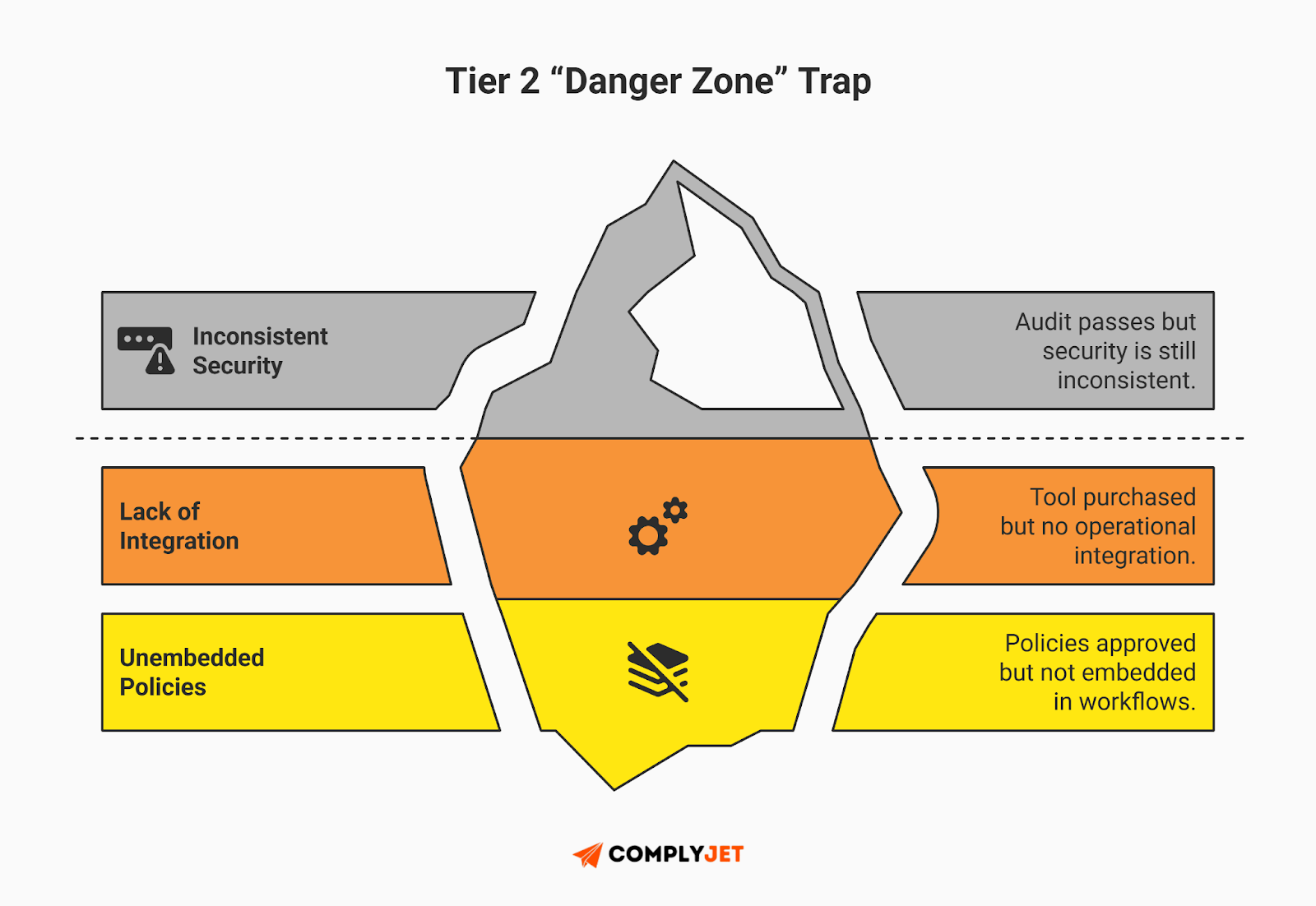
To evaluate the maturity and integration of your risk management practices, the NIST framework uses Implementation Tiers (1-4).
Your immediate operational goal for NIST compliance is to achieve Tier 3. Reaching a repeatable state proves to the market that your security is embedded into your company culture.
The Federal Mandate: CMMC 2.0 and The 800-171 Dilemma
For the Defense Industrial Base (DIB), NIST SP 800-171 compliance is now synonymous with revenue retention. The enforcer validating this security posture is CMMC 2.0, which entered its official rollout phase in late 2025. As of February 2026, the program is fully enforceable, making verified cybersecurity a non-negotiable condition for contract awards.
Stat Check: With 87% of leaders identifying AI-related vulnerabilities as the fastest-growing risk, the Department of Defense is using CMMC 2.0 as a filter for supply chain resilience. This makes NIST compliance the only way to protect your federal revenue streams from emerging threats.
CMMC 2.0 Rollout Status (2026)
The phased rollout is aggressive: Phase 1 officially launched on November 10, 2025, mandating self-assessments and SPRS scores, while Phase 2 - which introduces mandatory C3PAO third-party assessments for prioritized acquisitions - takes effect on November 10, 2026.

Additionally, contractors must now obtain and upload a CMMC Unique Identifier (UID) for each information system to the SPRS database as a prerequisite for contract award.
The Rev 2 vs. Rev 3 Trap
A critical challenge in 2026 is the misalignment between the legal requirements and the latest standards. NIST released SP 800-171 Revision 3, but the CMMC 2.0 rule is legally codified around Revision 2.
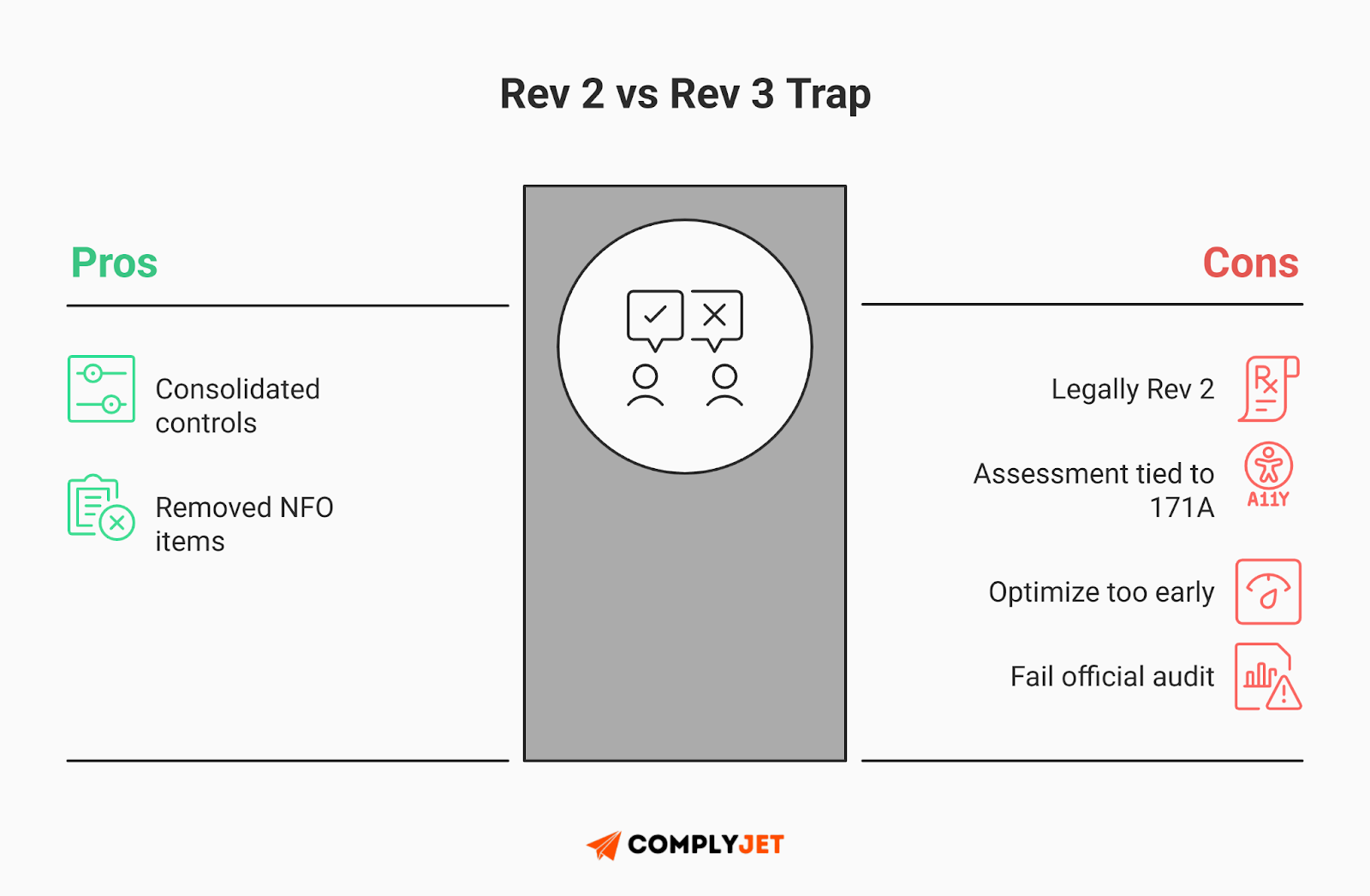
If you try to future proof your architecture by implementing Revision 3 today, you could fail your assessment. Revision 3 consolidated and removed certain NFO controls. An assessor using the Revision 2 assessment guide, SP 800 171A, may mark you deficient for a control you removed.
To maintain NIST compliance, you must preserve a strict Revision 2 baseline in all official audit artifacts, including your SSP and POA&M.
CMMC Cost Modeling for 2026
Budgeting for certification is a significant financial event. The following figures are generalized market estimates compiled from industry pricing intelligence and limited survey data. They are not official government guidance and should not be relied upon as guaranteed certification costs.
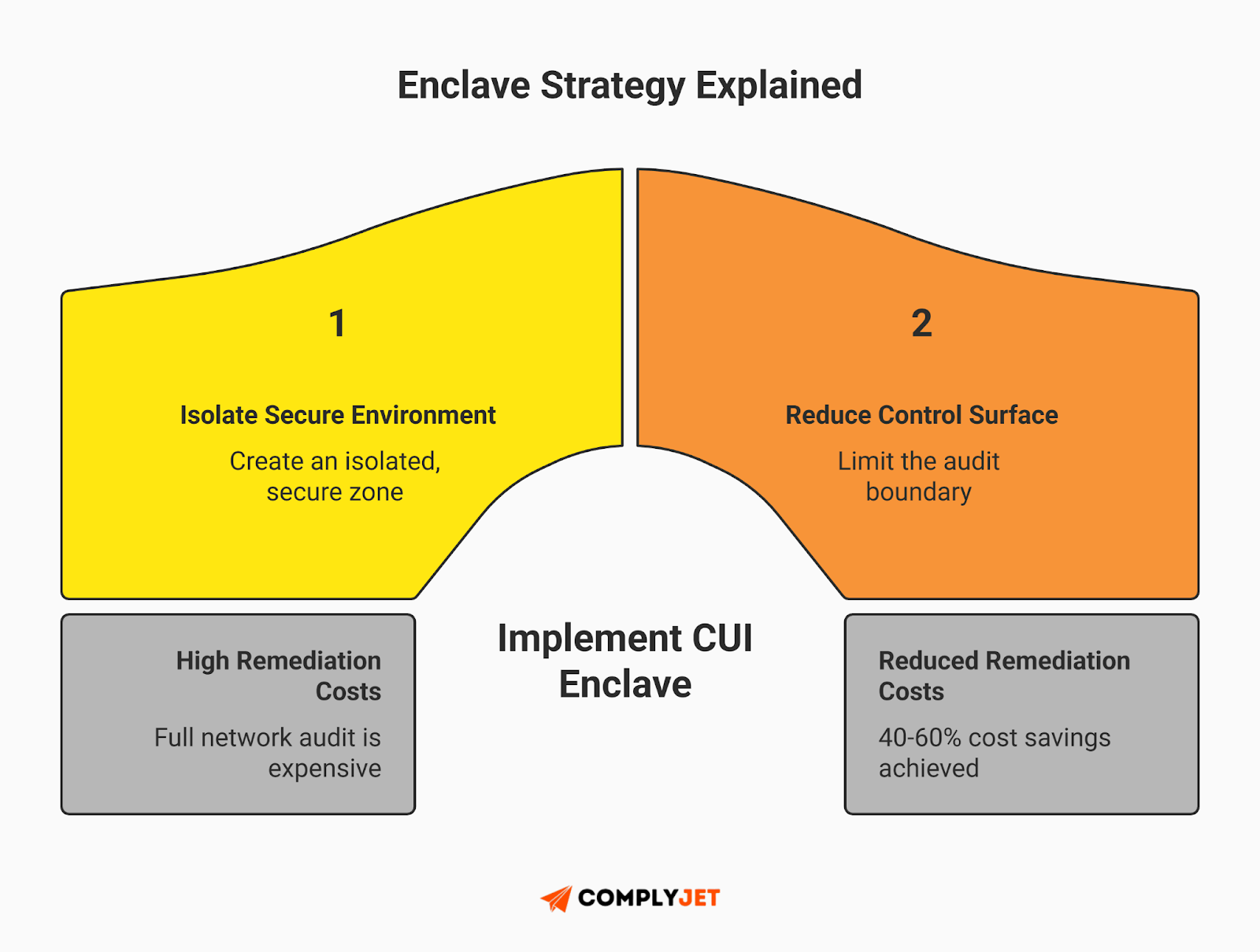
Illustrative Scenario: A 40-person SaaS firm nearly abandoned a lucrative DoD contract when quoted $250k for full-network remediation. Instead of dragging their entire startup into scope, they adopted an "Enclave Strategy". By utilizing a CUI enclave architecture, they spun up a secure environment strictly for handling sensitive data. By isolating the blast radius, they reduced their assessment scope and slashed their costs to achieve NIST compliance by ~40%.
The SaaS Bridge and NIST as the Master Key
Most lean US SaaS startups look at the requirements for NIST compliance and see nothing but heavy, bureaucratic federal red tape. They assume it is strictly for legacy defense contractors and immediately pivot all their resources into chasing a SOC 2 report just to unblock their immediate sales pipeline.
This siloed thinking is a massive drain on your engineering resources and your budget. Treating every audit for NIST compliance as a disconnected, frantic sprint is the exact opposite of scalable growth.
Why SaaS Startups Should Care About NIST
Instead of viewing it as a standalone hurdle, reframe the NIST framework as the ultimate foundation for your overarching Integrated Risk Management (IRM) strategy. When you implement the framework, you establish a unified governance baseline. You build a secure architecture once, and you map the evidence multiple times.
Doing the heavy lifting for NIST compliance upfront actively drives down your audit costs and reduces friction for every other commercial framework you actually care about.
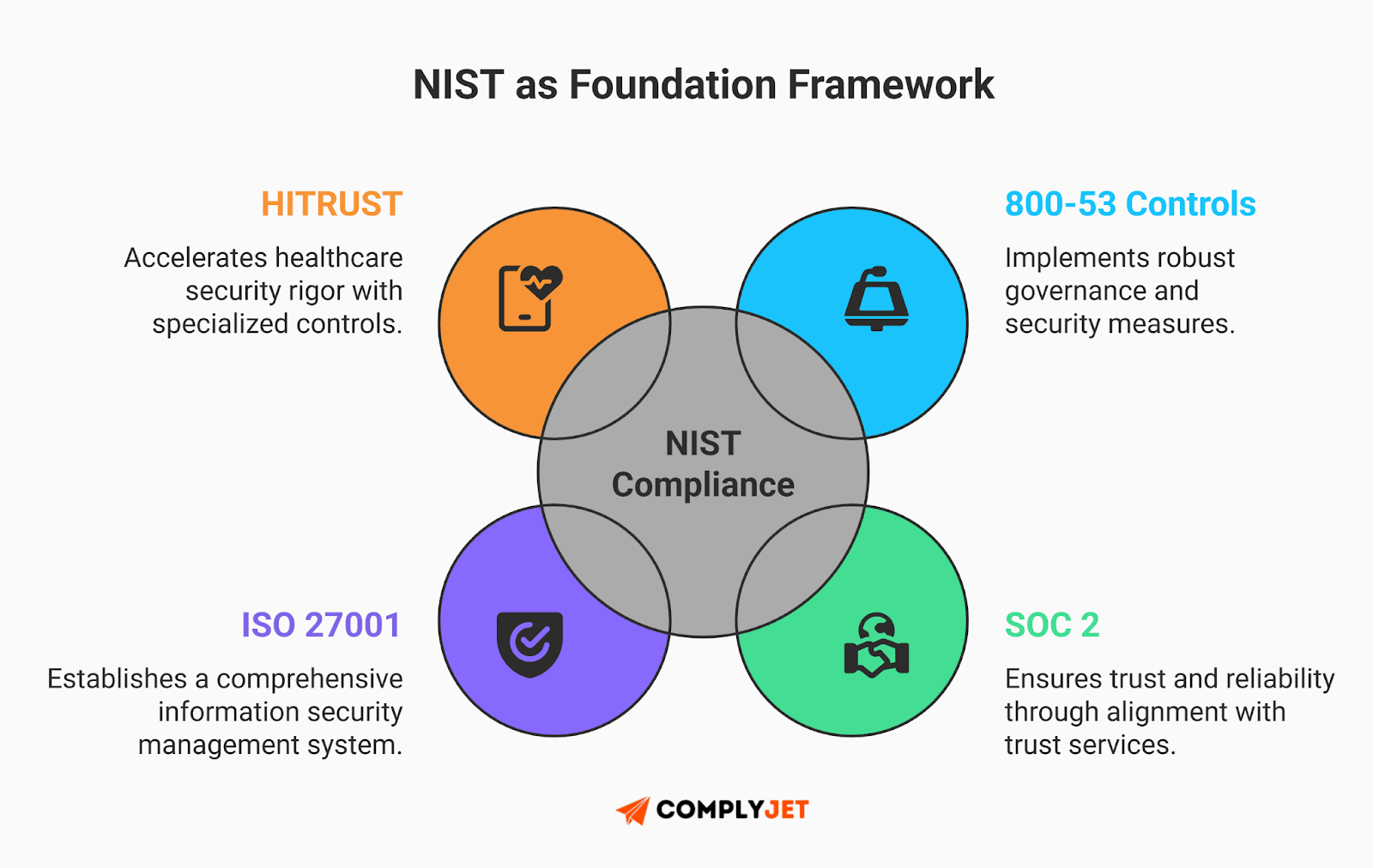
Mapping NIST to Commercial Frameworks
- SOC 2: The AICPA's SOC 2 revolves around the Trust Services Criteria - specifically Security, Availability, and Confidentiality. When you operationalize the "Protect" and "Govern" functions of the NIST framework, you are inherently fulfilling these exact criteria.
You are effectively pre-building the engine that turns a grueling SOC 2 audit into a smooth, frictionless review.
- ISO 27001: If your roadmap includes international expansion, you will eventually need ISO 27001. The core requirement of this standard is the establishment of a continuous Information Security Management System (ISMS).
NIST SP 800-53 is broad and detailed. Strong alignment with its controls puts organizations beyond most baseline ISMS requirements. However, formal certification still requires documented governance, audits, and review processes.
- HITRUST & PHI: For healthcare founders, the stakes are exponentially higher. By mapping your infrastructure to NIST compliance controls from day one, you establish most of the rigorous data flow security mandated by the healthcare sector.
This makes securing Protected Health Information (PHI) and achieving HITRUST certification significantly faster.
Emerging NIST Tech: AI Governance & PQC
If your strategy for NIST compliance looks identical to what it was in 2023, you are already obsolete. The 2026 landscape specifically targets two emerging threats: unauthorized generative AI usage and the impending cryptographic transition. Enterprise buyers are scrutinizing these areas right now.
Governing the "Shadow AI" Explosion
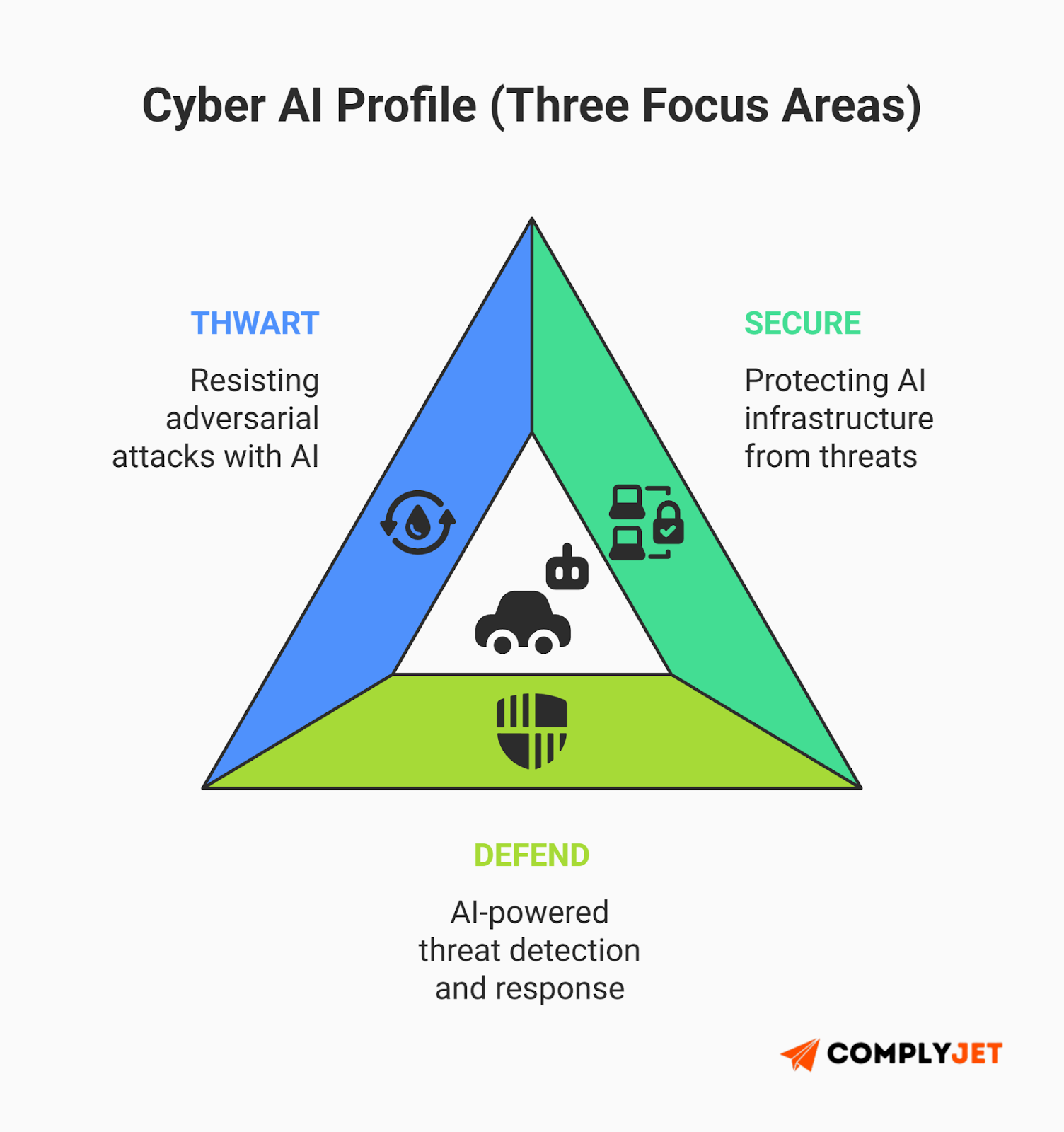
Your engineers and sales teams are already using unauthorized GenAI tools to process your sensitive corporate data. To govern this chaos, you must adopt the Cyber AI Profile (Draft IR 8596), which explicitly tailors the framework for artificial intelligence. Adopting the Cyber AI Profile breaks AI security into three focus areas:
- SECURE: Protect the AI system itself. In 2026, this includes strong machine identity management for autonomous AI agents. To meet NIST expectations, each agent should have a unique, traceable identity. This helps prevent unauthorized lateral movement across systems.
- DEFEND: Using AI to enhance cybersecurity, leveraging AI-driven anomaly detection to spot pattern deviations indicative of a breach.
- THWART: Building resilience against AI-enabled attacks, including deepfakes and adversarial model evasion.
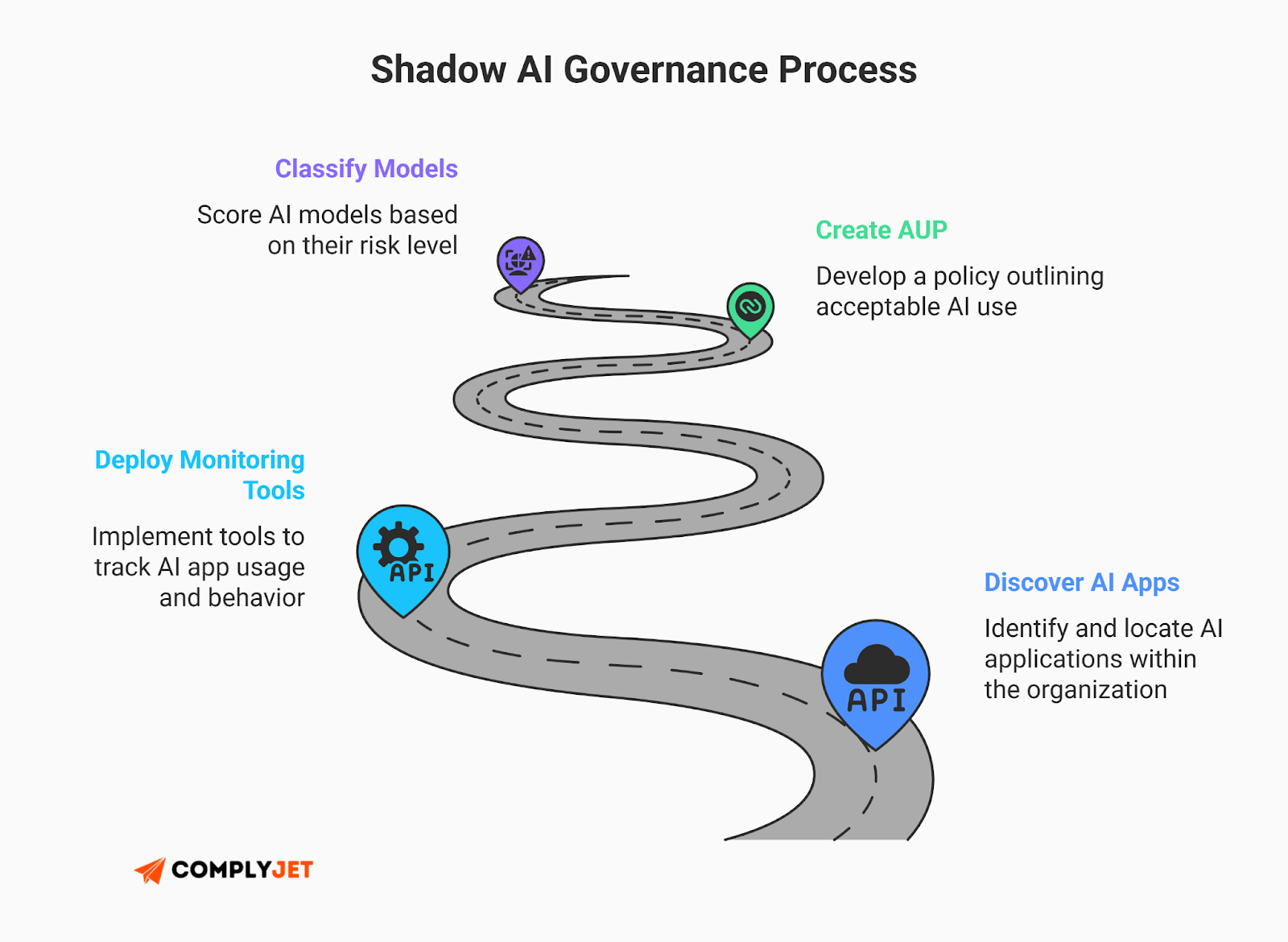
Actionable Steps: You cannot secure what you cannot see. Immediately deploy Shadow AI discovery tools, such as Microsoft Defender for Cloud Apps, to pinpoint exactly which unauthorized AI apps are active on your network. Next, establish a strict Acceptable Use Policy for NIST compliance. Finally, formally map all in-house models using the NIST AI RMF to accurately classify their risk levels from Low to High.
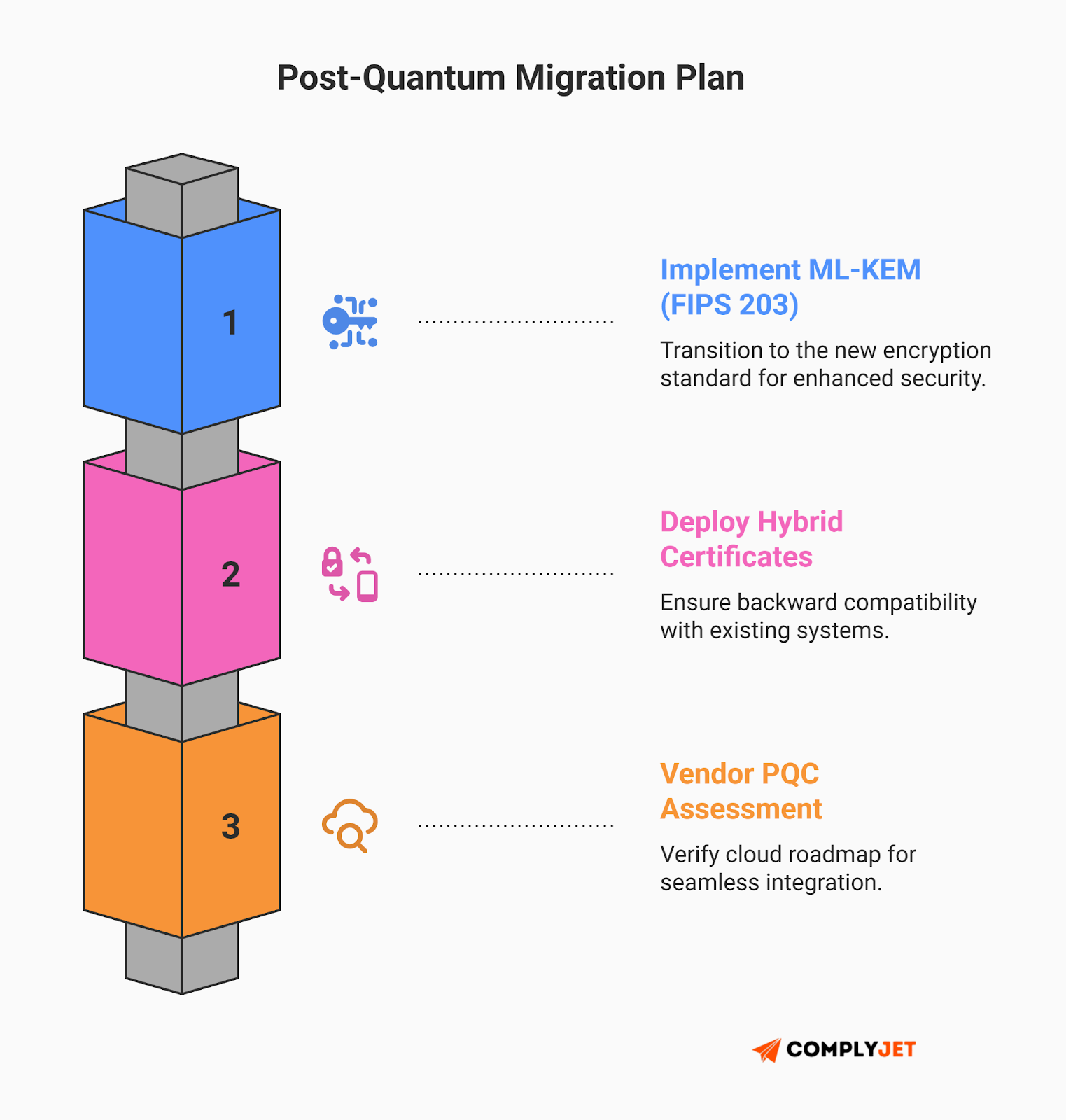
Post-Quantum Cryptography (PQC): The 2026 Migration
Quantum computing might sound like a future problem, but nation-state adversaries are executing a "Harvest Now, Decrypt Later" (HNDL) strategy today - stealing your encrypted data now to break it open once quantum tech matures. Maintaining long-term NIST compliance requires addressing this now.
The immediate mandate for founders is the FIPS 203 ML-KEM migration. Do not attempt a "rip and replace" of your cryptography. Instead, implement hybrid certificates that utilize both classical and post-quantum algorithms to ensure backward compatibility.
Concurrently, execute aggressive vendor assessments to ensure your cloud providers have a roadmap for these new standards.
Operationalizing NIST Compliance: Tools, Talent & Budgets
The complexity of continuous monitoring in 2026 absolutely necessitates a GRC automation platform. However, a major pitfall in achieving NIST compliance is confusing software with security.
The Danger of "Evidence Vacuums"
Automation handles the Automated evidence collection, but governance requires human decision-making. Late 2025 saw the update of NIST SP 800-70 Rev 5, which introduced "evidence-ready automation". This standard encourages the use of Standardized Identifiers (CCE) to allow your systems to self-report their configuration status directly to your GRC tools.
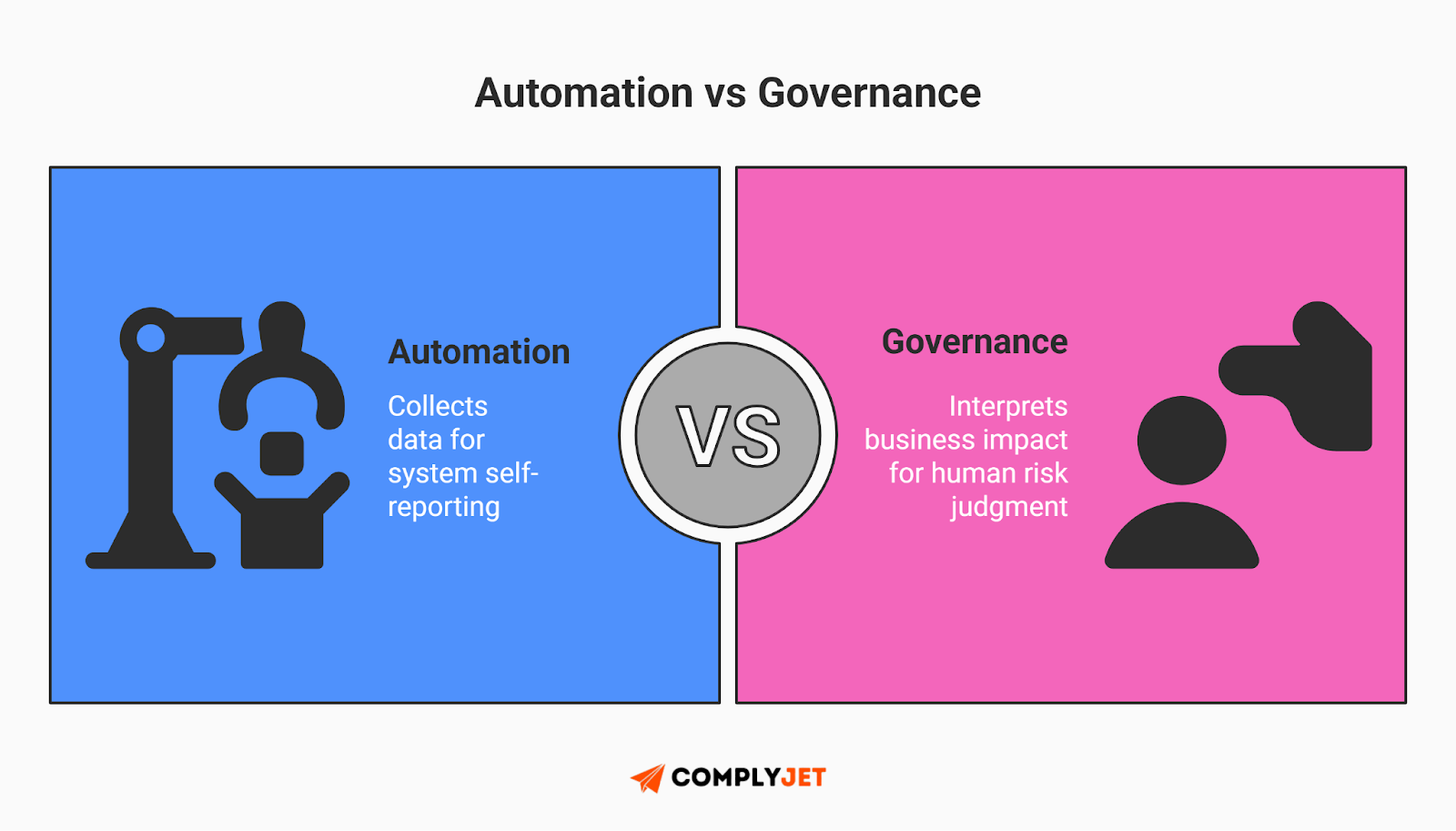
Without a human compliance lead to interpret the data, legacy tools often become expensive evidence vacuums. They collect artifacts but leave founders staring at dashboards full of red alerts. ComplyJet changes this by combining Tier 2 automation with real GRC expertise so teams can turn data into action and move toward NIST compliance.
Resource Allocation Models (2026 Costs)
You must build a budget that matches your maturity. In the U.S., a mid-level GRC Analyst commands $120,000 to $160,000, while a CISO floor is $200,000+. (See our 2026 GRC compensation breakdown for full salary benchmarks.) When factoring in talent and GRC software pricing in 2026, your allocation must be ruthless:
- Model A: The Lean Startup: Retain a Virtual CISO (vCISO) for strategic guidance ($5k/month) and invest in a Tier 2 platform to handle the heavy lifting.
- Model B: The Regulated Mid-Market: Hire a dedicated internal GRC Lead ($140k/yr) to own the SSP and audit relationship, supported by dedicated vulnerability management and MDR services.
Mapping CSF 2.0 shouldn't stall your product roadmap. ComplyJet automates evidence collection so you can actually focus on building your startup. Get the premium, automated compliance experience of the legacy players, but with hands-on help and a startup-friendly price point.
Sector-Specific NIST Compliance Fast Tracks: Community Profiles
The fastest way to stall your security roadmap is to stare at a blank spreadsheet of a thousand controls. Fortunately, you can now bypass the guesswork by leveraging tailored Community Profiles. This "fast track" can reduce your initial mapping workload for NIST adherence by ~30-40%.
SaaS & Cloud Service Providers (CSPs)
Align your architecture directly with the NIST CSF v2 Cloud Community Profile, which heavily leverages the CSA CCM v4.0 mapping. If you are selling to the government, remember that FedRAMP Rev 5 baselines are significantly more rigorous than commercial standards, particularly regarding supply chain security.
Healthcare & MedTech
NIST adherence can lay the foundation for protecting sensitive data and aligning with the HIPAA Security Rule. As the Internet of Medical Things (IoMT) expands, NIST SP 1800-30 provides practical guidance to secure the continuous data flow between connected patient devices and cloud systems.
Manufacturing & Critical Infrastructure
Your biggest existential threat is OT/IT Convergence. To achieve NIST compliance in this sector, manufacturers should follow the NIST CSF 2.0 Manufacturing Profile (IR 8183 Revision 2), finalized in late 2025, which provides a tailored roadmap for aligning OT systems with the new 'Govern' function.
The NIST "Monday Morning" Action Plan
Reading about cybersecurity strategy doesn't actually secure your revenue; execution does. Here is your immediate, four-step action plan to operationalize the NIST Cybersecurity framework before your next enterprise audit. Meeting modern NIST standards is a marathon, but these steps set the pace:
- Adopt CSF 2.0 (Govern Workshop): Formally transition your internal risk register to the 2.0 structure. Schedule an executive "Govern" workshop this week to define your organization's risk tolerance.
- Inventory Assets: You cannot protect what you cannot see. Immediately deploy discovery tools for hardware, software, and AI models to map your ephemeral cloud assets.
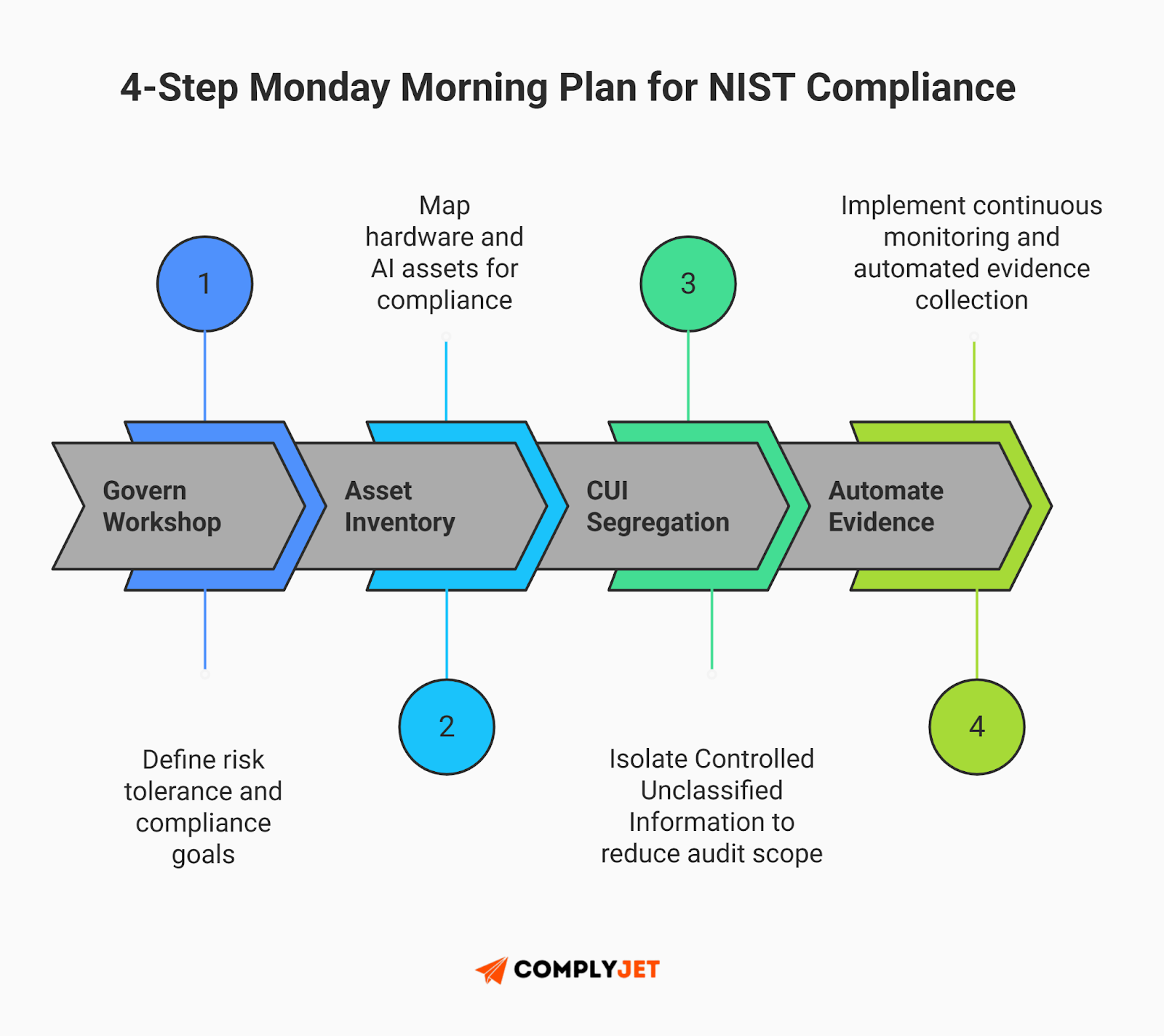
- Segregate CUI: If you are chasing federal defense contracts, architect a secure CUI enclave architecture. This isolates Controlled Unclassified Information and significantly reduces the potential blast radius and audit scope.
- Automate Evidence: Ditch the manual spreadsheets. Implement a GRC platform to move from audit panic to continuous NIST compliance.
The 2026 NIST Compliance Glossary
The government loves acronyms, but bouncing to a search engine every two minutes kills your momentum. To maintain your NIST compliance flow, here is your rapid-fire translation guide:
- CUI (Controlled Unclassified Information): Sensitive data requiring protection; it is the core focus of the NIST 800-171 standard.
- CMMC (Cybersecurity Maturity Model Certification): The Department of Defense's enforcement mechanism validating that you are actually meeting the requirements for NIST compliance.
- C3PAO (Certified Third-Party Assessor Organization): Independent auditors required for CMMC Level 2 assessments.
- SPRS (Supplier Performance Risk System): The federal database where your NIST 800-171 self-assessment scores must be submitted.
- SBOM (Software Bill of Materials): A nested inventory of software ingredients, vital for Supply Chain Risk Management.
- PQC (Post-Quantum Cryptography): Algorithms secure against future quantum attacks.
2026 NIST Compliance FAQs
Is NIST CSF 2.0 mandatory for small SaaS startups?
While technically voluntary, the reality of Supply Chain Risk Management (C-SCRM) makes it effectively mandatory for NIST compliance. Enterprise buyers will legally flow down their own requirements to your startup.
What is the trap between NIST SP 800-171 Rev 2 and Rev 3 for DoD contractors?
It is a dangerous conflict. NIST SP 800-171 Rev 3 is the newer standard, but CMMC 2.0 is legally codified around Revision 2. Implementing Rev 3 controls now might cause you to fail a Rev 2 assessment because an auditor will look for specific NFO controls that were removed in the new version.
Can we fully automate NIST 800-53 compliance with software?
No. Automation handles evidence collection, but achieving true NIST compliance requires human governance. A tool can flag a missing policy, but a human must make the strategic business risk decisions.
Exactly how much does a CMMC 2.0 audit cost in 2026?

Prepare your runway. For a small business, the C3PAO audit cost in 2026 alone ranges from $30,000 to $50,000. Total year-one investments for NIST compliance often exceed $100,000.
How does the new Cyber AI Profile affect our employees using ChatGPT?
Unauthorized Shadow AI usage is a massive risk. The Cyber AI Profile requires you to identify this usage via discovery tools and establish a strict Acceptable Use Policy.
What is a CUI Enclave Strategy, and how does it save money?
Instead of bringing your entire network into scope for NIST compliance, you architect a secure, isolated environment strictly for CUI. This can reduce assessment costs by 40% to 60%.
What are the NIST CSF 2.0 Implementation Tiers?
Tiers range from 1 (Partial) to 4 (Adaptive). In 2026, Tier 3 (Repeatable) is the target state required for most enterprise vendor assessments.
Why is Post-Quantum Cryptography (PQC) a 2026 problem?
Adversaries are executing a "Harvest Now, Decrypt Later" strategy - stealing your data today to break it open once quantum tech matures. Transitioning is a long-term NIST compliance priority.
Make NIST Compliance Your Competitive Edge
In 2026, being NIST aligned is not a burden; it is your ultimate sales enabler. By building a robust, defensible infrastructure around the latest NIST frameworks, you instantly signal maturity to Fortune 500 buyers.
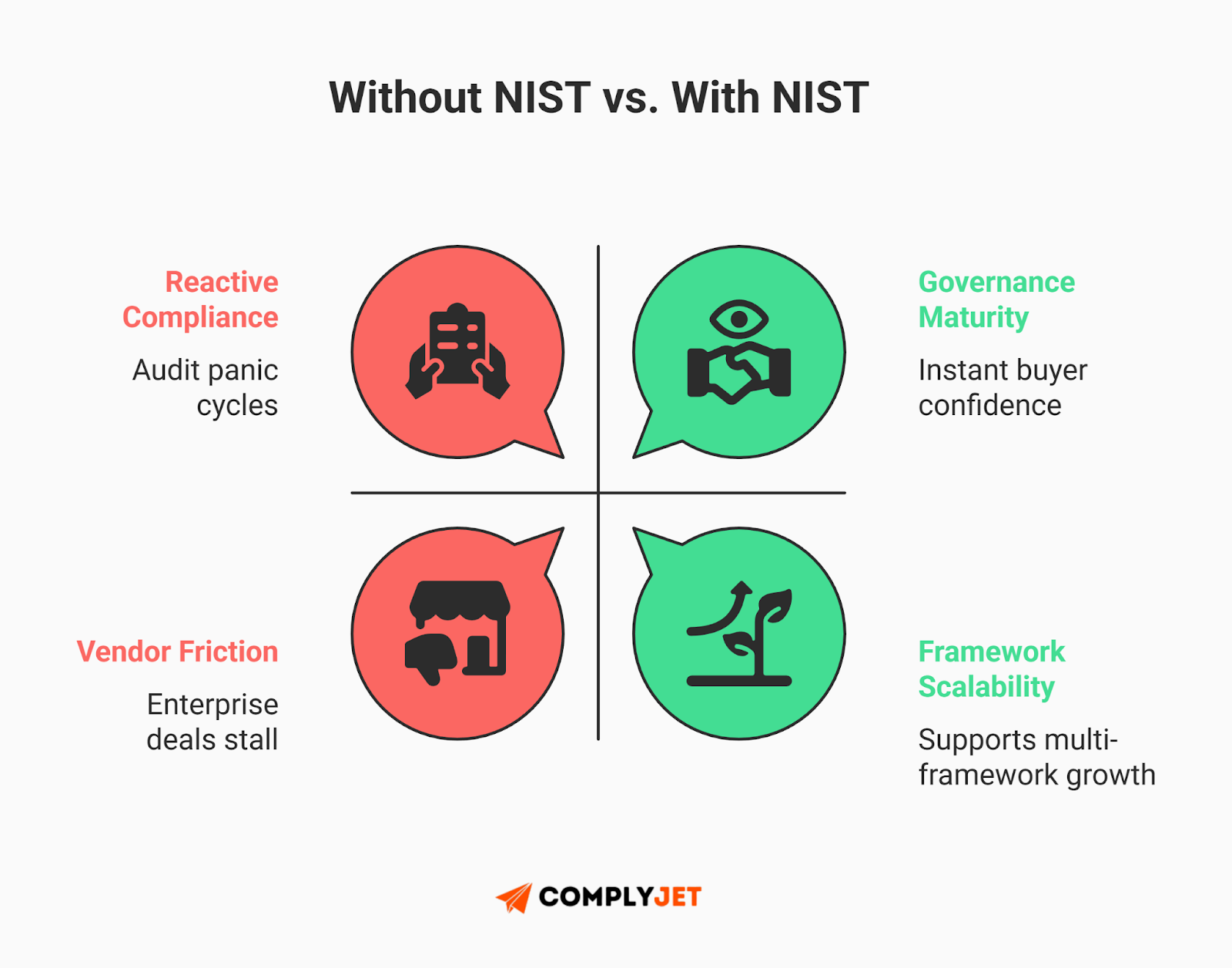
Do not let the complexity of NIST CSF compliance or the high C3PAO audit cost 2026 paralyze your team. It is very achievable when you pair targeted automation with the right human oversight. In 2026, it is time to make NIST compliance your strongest competitive differentiator.
Navigating CMMC enclaves, Shadow AI, and critical NIST controls shouldn't feel like a solo mission. At ComplyJet, you get direct access to founders who have been in your shoes and will handhold you across the finish line. We make enterprise-grade NIST compliance affordable, fast, and painless. Stop treating compliance like a guessing game. Book a demo today and let us relieve the pressure.



