Forget the dictionary definitions. In 2026, the distinction between GRC vs IRM is no longer an academic debate over terminology. It is the operational difference between surviving the SEC's strict four-day cybersecurity disclosure window and facing personal executive liability.
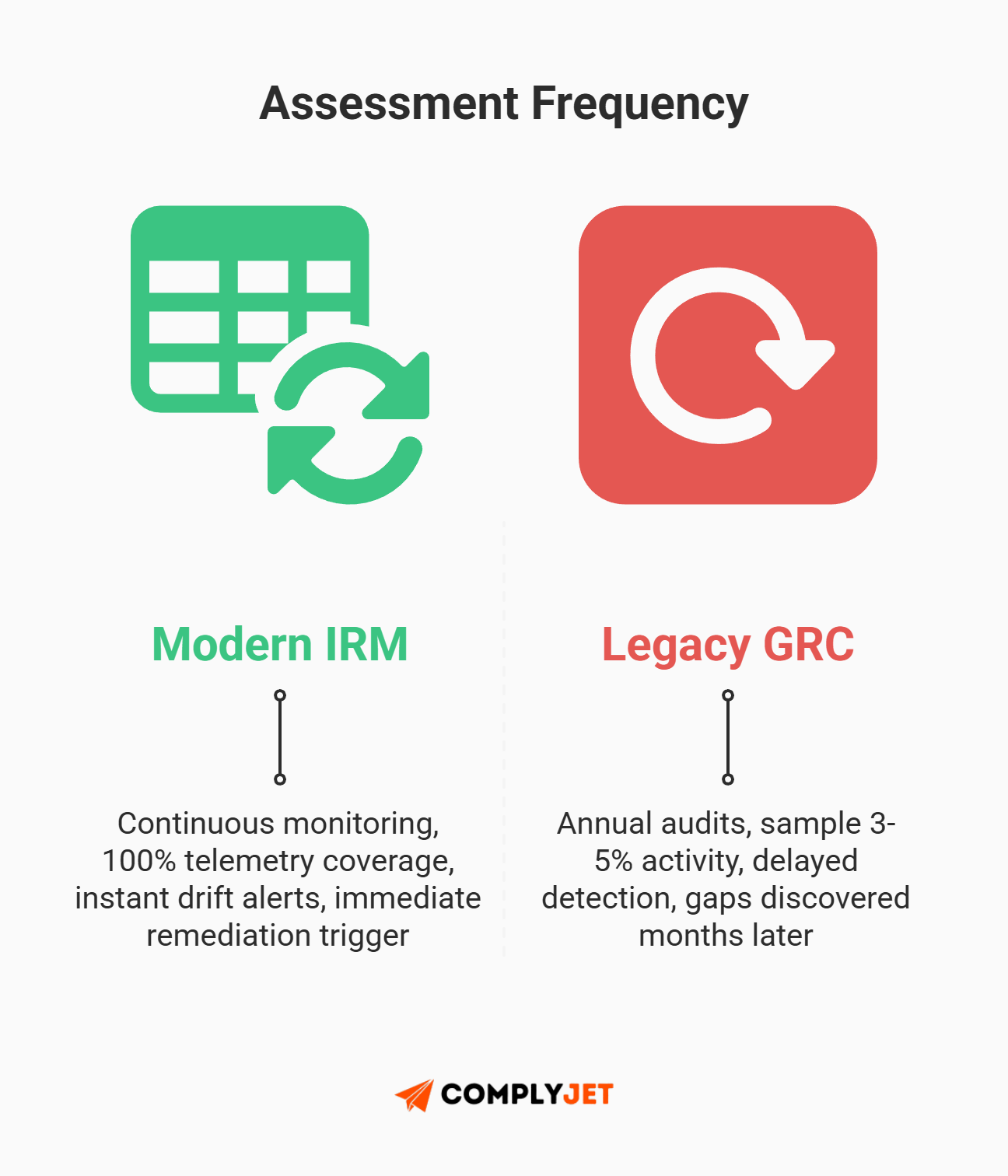
Traditional Governance, Risk, and Compliance (GRC) was built for a slower era. It is a closed system designed for static, annual audits and siloed spreadsheets. But these manual lists cannot keep pace with the velocity of modern threats.
They crumble under the dual pressures of 2026: governing autonomous Agentic AI and navigating a fragmented matrix of new state privacy laws in Indiana, Kentucky, and Rhode Island. This operational breaking point is exactly why the shift to Integrated Risk Management is no longer optional.
To survive, CISOs must transition to a modern risk architecture. Integrated Risk Management (IRM) is the dynamic, API-driven answer to this obsolescence. It replaces periodic check-ins with continuous, automated telemetry.
Founder Tip: Don't get hung up on the acronyms. Think of GRC as the "Law Book" and IRM as the "Security Camera Network." One is static text; the other is active monitoring.
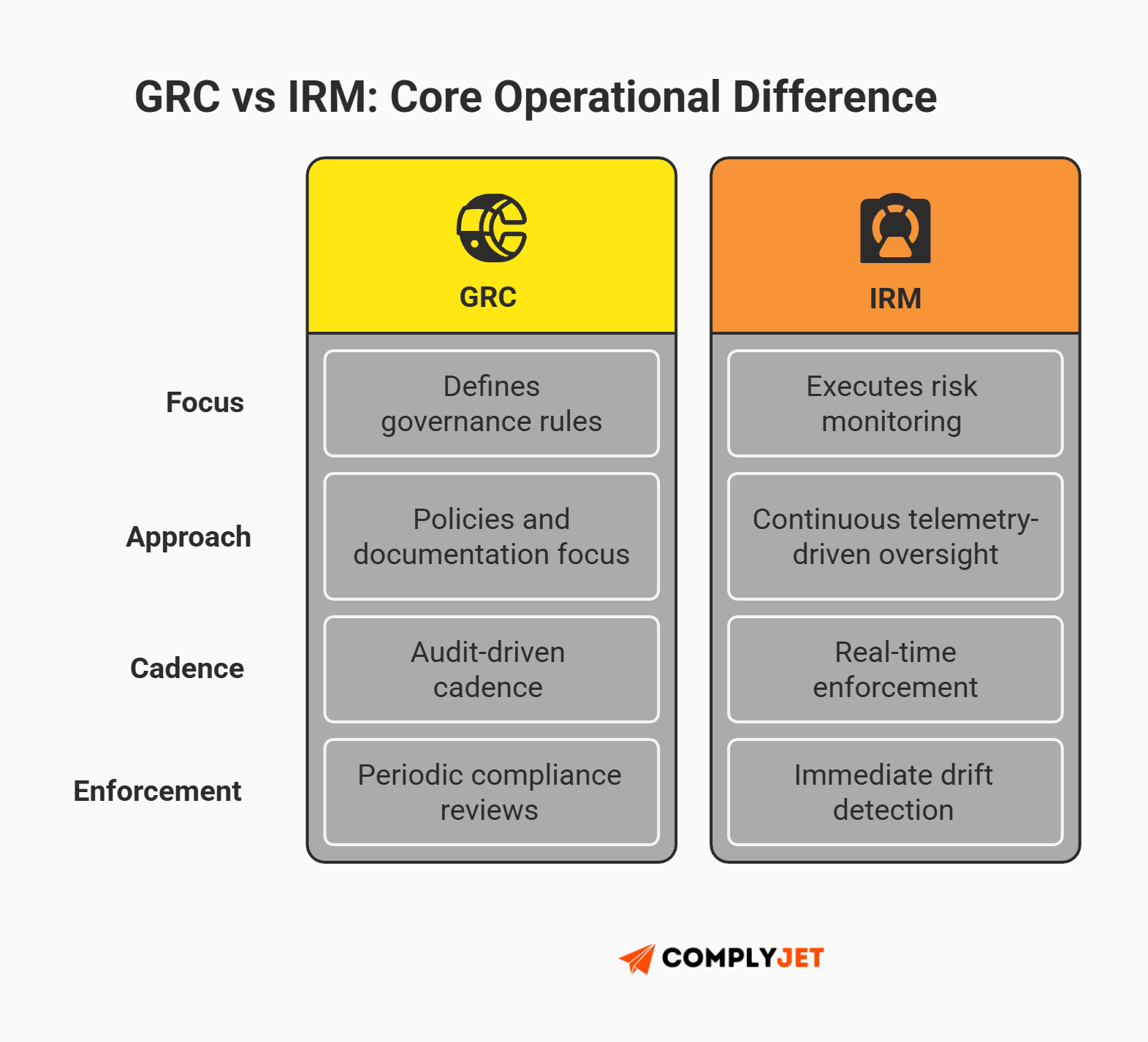
Here is the simple truth about GRC vs IRM:
While GRC provides the rules (Governance), IRM provides the engineering (Risk) to execute them in real-time. If you are still debating GRC vs IRM semantics while your competitors automate evidence collection, you are already behind.
What is the Difference Between GRC and IRM?
To understand the GRC vs IRM divide, you must look at the data flow, not the marketing surrounding GRC and IRM.
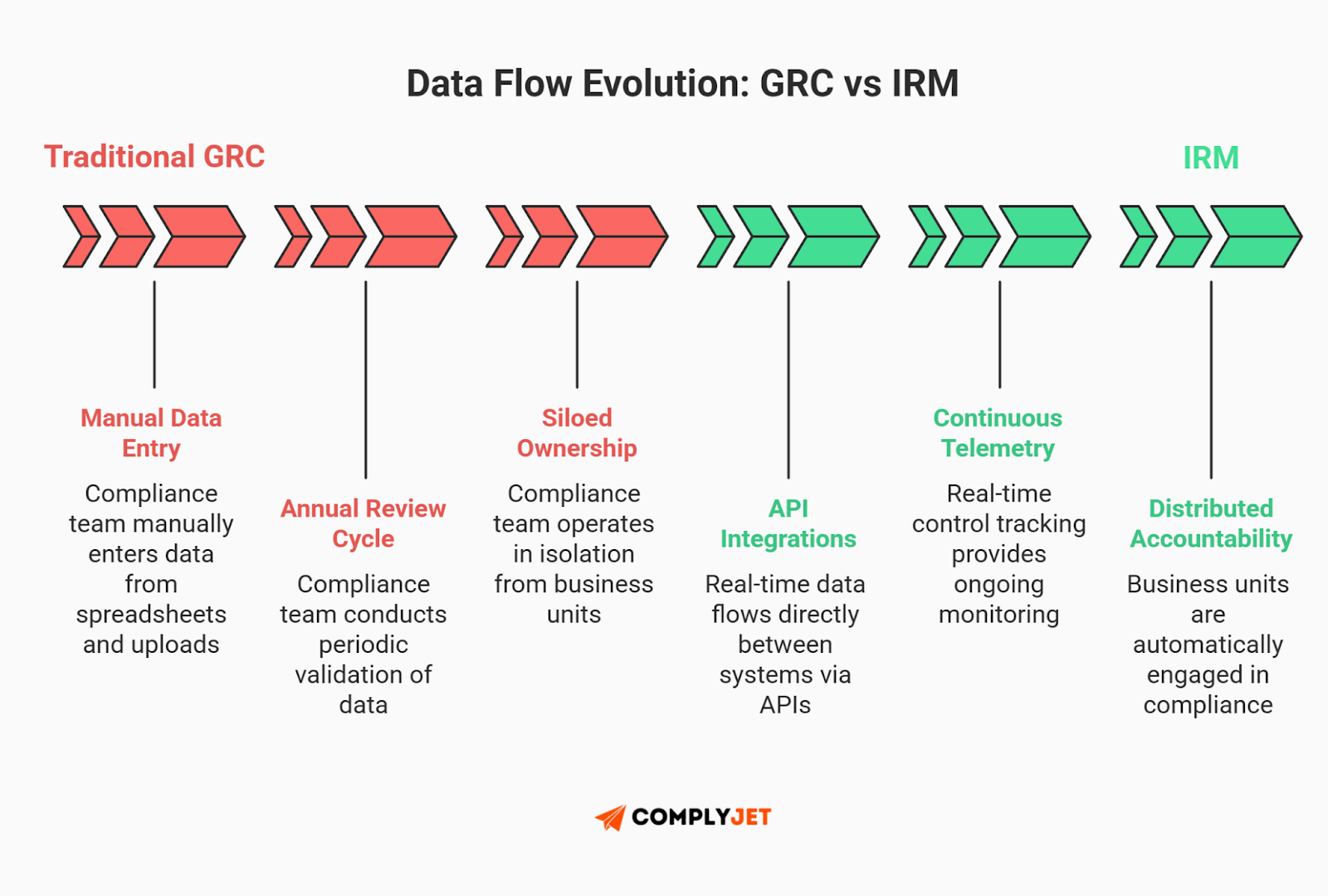
- GRC (The Law Book): Compliance teams own the data in a silo. Business units only "visit" the system during audit season.
- IRM (The Security Camera): The system lives in the background of daily operations, monitoring risk without human input.
Founder Tip: Many practitioners on Reddit forums argue that IRM is simply "GRC done right." There is truth to this. If a vendor sells you an IRM tool that still requires manual evidence uploads, it is just a buzzword. True IRM is defined by connectivity - if it cannot connect to your tech stack via API, it is not IRM.
Defining Traditional GRC (The Legacy Model)
Governance Risk and Compliance (GRC) was born in the panic of the post-Enron era (2002). It was built for a world of static, top-down policy adherence.
The primary characteristic of GRC is its closed system architecture. Compliance teams own the data in a silo. Business units - the people actually taking the risks - only "visit" the system once a year during audit season.
This isolation creates a fatal flaw known as Paper Ownership. On a spreadsheet, a manager is listed as the owner of a control. In reality, they haven't looked at it in eleven months. The control exists on paper, but it is operationally dead.
Defining Modern IRM (The 2026 Operational Model)
Integrated Risk Management (IRM) is the response to that failure. It is the open, API-driven evolution of Governance Risk and Compliance.
The term and its core attributes were originally formalized by Gartner to push the industry beyond legacy compliance. Ironically, Gartner recently retired IRM as an official market category. Why? Because the industry became overly obsessed with the acronym rather than the execution. Analysts are constantly rebranding these tools as Risk Intelligence or Continuous Monitoring.
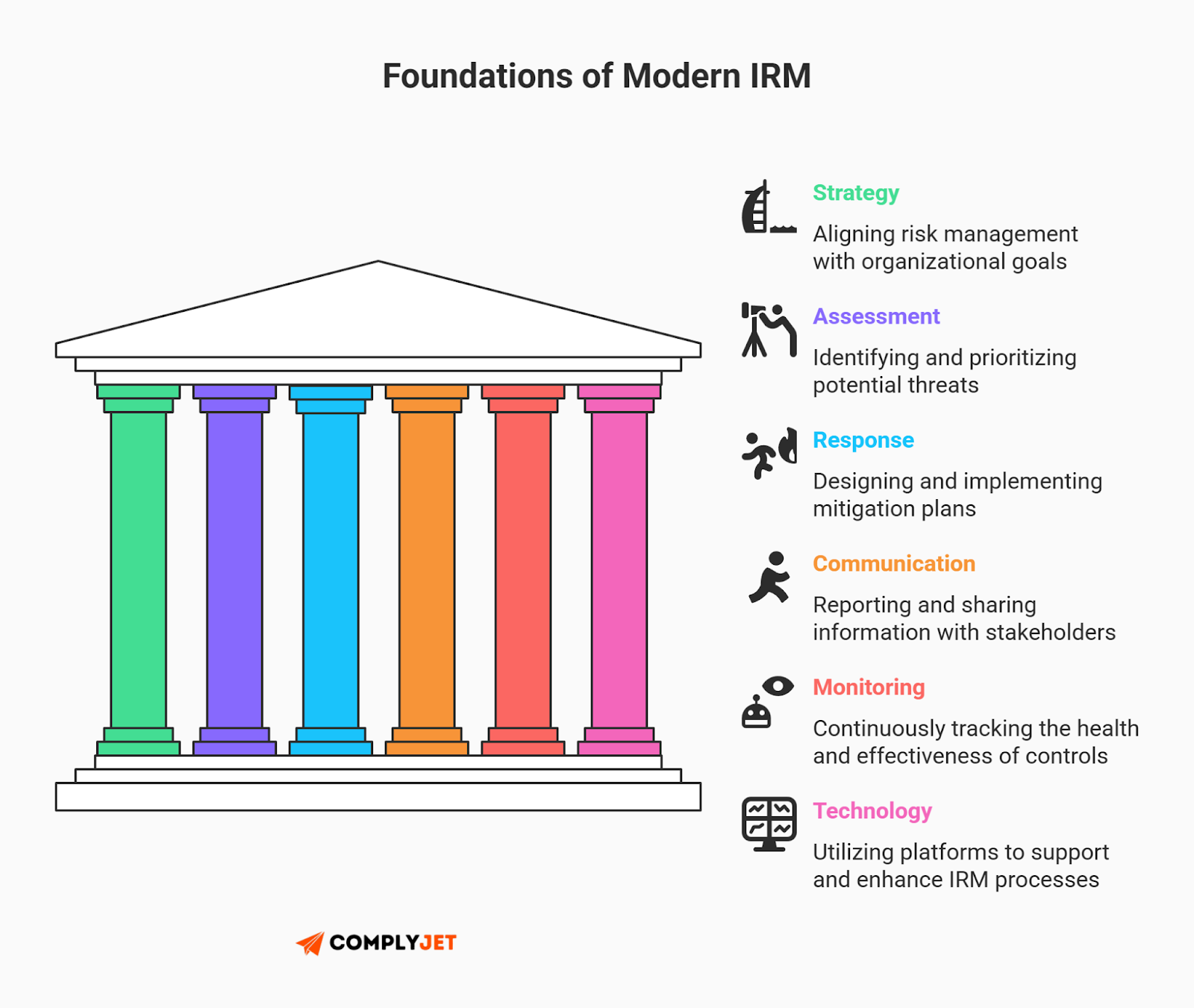
But regardless of what analysts name it today, the original six attributes of IRM defined by Gartner remain the absolute blueprint for a 2026 operational strategy. You cannot execute modern risk management without them:
- Strategy: Enabling a framework for performance improvement.
- Assessment: Identifying, evaluating, and prioritizing risks.
- Response: Designing and implementing risk mitigation mechanisms.
- Communication and Reporting: Delivering actionable risk information to stakeholders.
- Monitoring: Continuously tracking risk processes and compliance.
- Technology: The architecture (IRM software) that enables the other five.
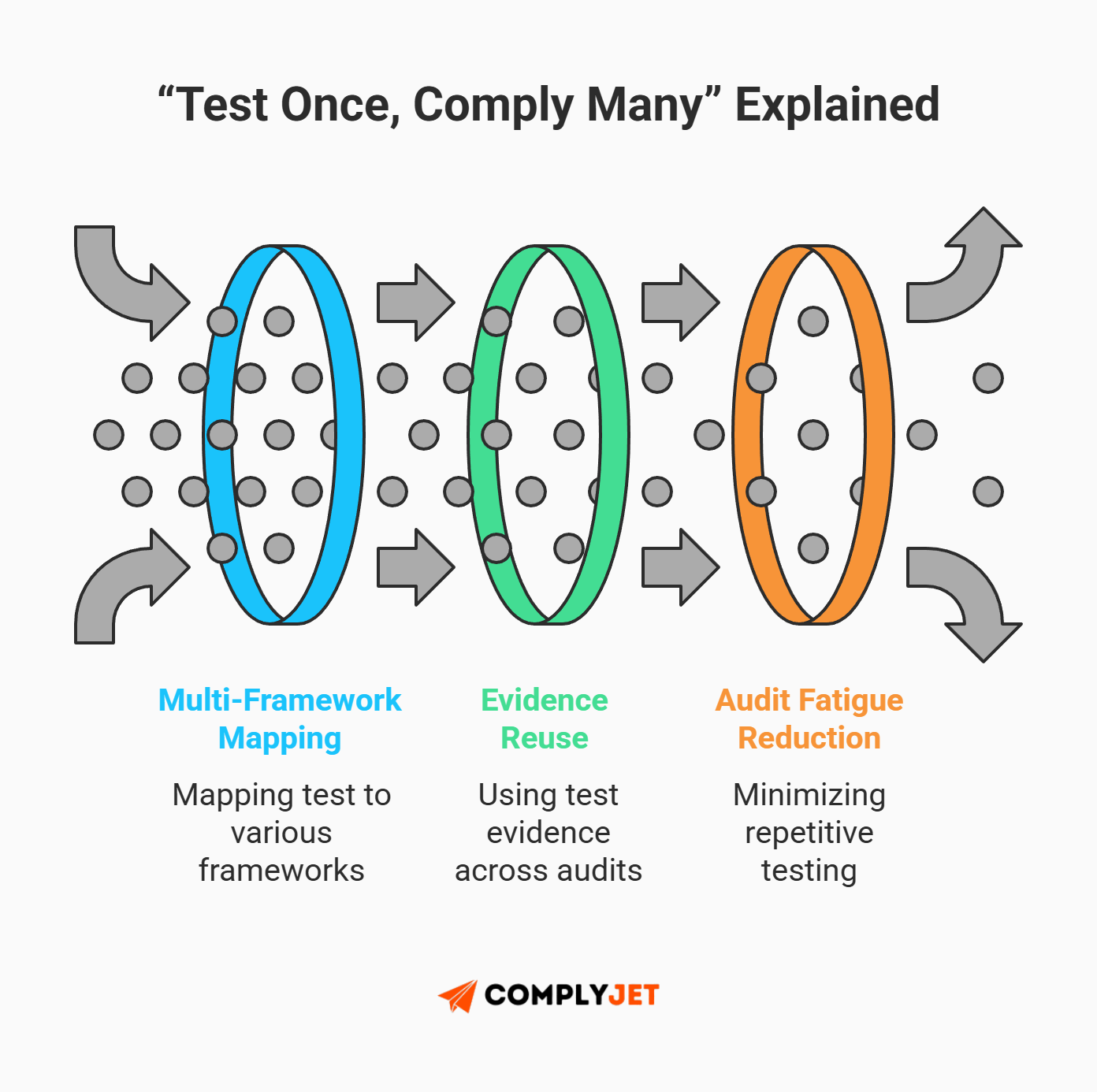
This architecture enables the "Test Once, Comply Many" philosophy, highlighting a core operational difference between GRC and IRM.
When comparing IRC to GRM, GRC requires you to test a control like "MFA on Root Account" three separate times for SOC 2, ISO 27001, and HIPAA. IRM is smarter. It maps that single technical control to all three frameworks simultaneously. You test the control once. The system applies the evidence everywhere, instantly eliminating audit fatigue.
Ultimately, the GRC vs IRM debate comes down to this: GRC is about documenting the past; IRM is about monitoring the present. If your risk management strategy relies on manual entry, you are still living in 2002.
Stop managing "paper owners" and chasing screenshots. See how ComplyJet’s native API integrations automate your evidence collection and turn static policies into real-time risk intelligence, all without putting a dent in your wallet. Check out our transparent pricing structure.
The Core Comparison Matrix: Architectural Differences
When evaluating GRC vs IRM software, marketing brochures often sound identical. Both promise efficiency and visibility. However, the architectural reality is starkly different. To make a high-intent commercial decision, you must look under the hood at how data actually moves and evaluate their capacity for continuous control monitoring.
Below is the definitive GRC vs IRM feature breakdown for the 2026 enterprise.
Why Paper Ownership is the GRC Killer
The most visceral frustration in the GRC vs IRM debate is the fallacy of Paper Ownership.
In a traditional siloed compliance model, a VP of Engineering might be listed as the owner of an access control policy. On paper, the risk is managed. In reality, that VP hasn't logged into the GRC portal in eleven months. When an audit occurs, the compliance team must frantically scrape for evidence, often discovering that the control failed months ago.
This is where continuous control monitoring changes the game.
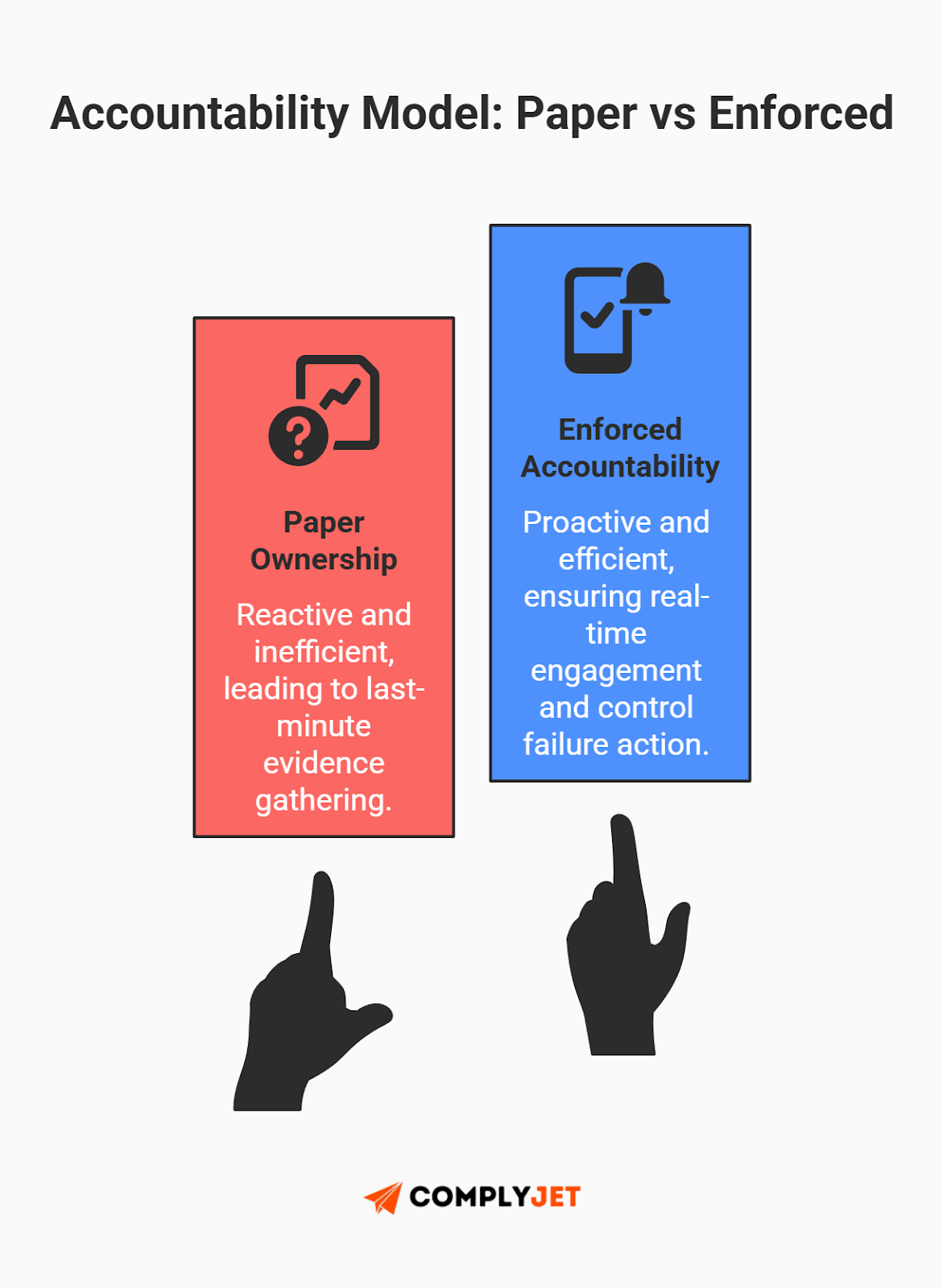
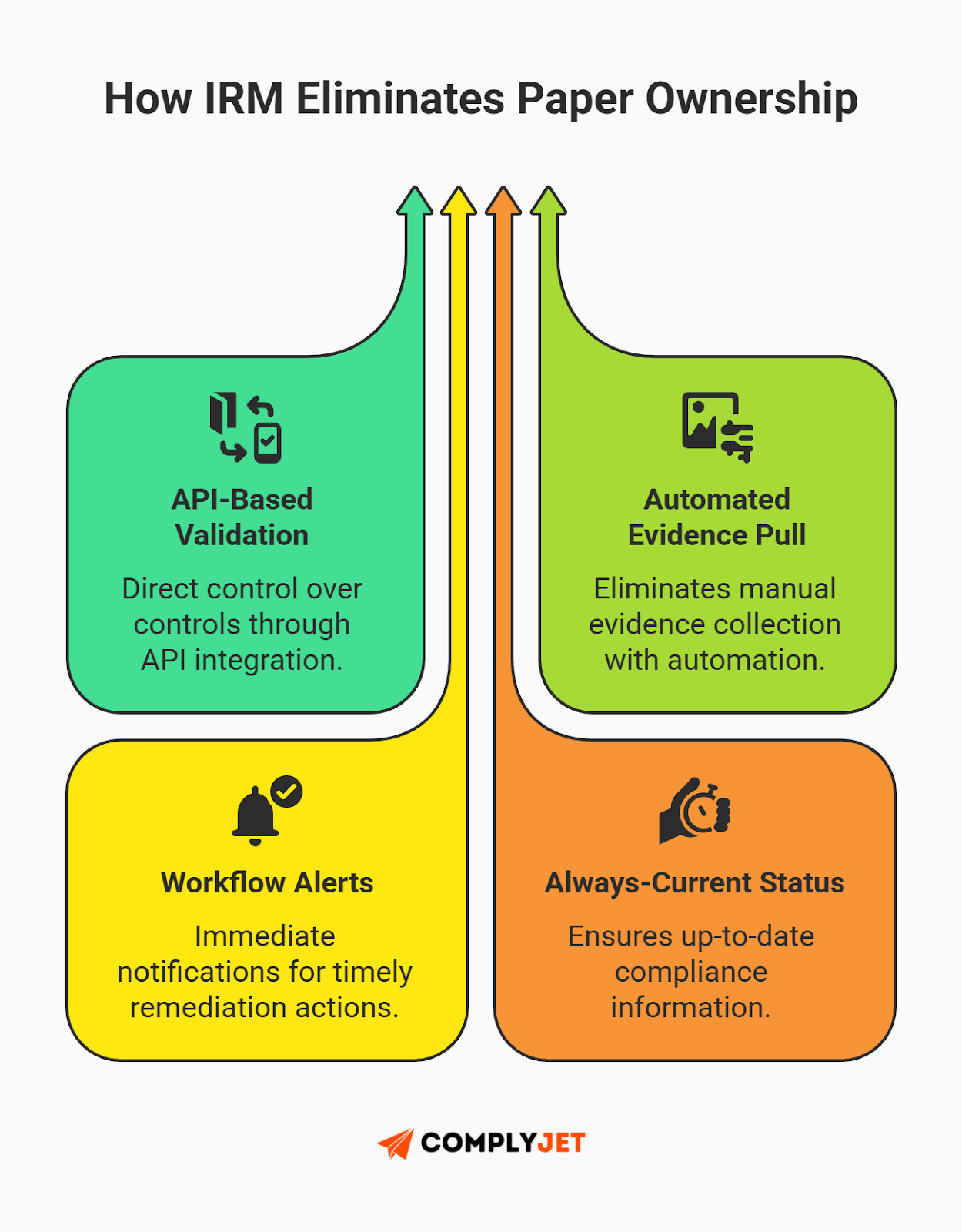
Modern IRM platforms eliminate this "theater of security" by using API integrations to monitor the control itself, not the policy document. Instead of waiting for an annual review, the system detects failure instantly.
If a developer pushes code that violates a security rule, the IRM platform doesn't wait for a meeting. It triggers an automated alert directly to the engineering lead's daily communication tool (like Slack), demanding immediate remediation. This shifts the culture from compliance checking to actual risk reduction.
When it comes to GRC vs IRM, only IRM enforces true accountability through continuous control monitoring.
Founder Tip: If your compliance status is only accurate the day after an audit, you are running a legacy GRC model. IRM means your compliance status is accurate right now.
The 2026 Regulatory Crucible: Why IRM is Now Non-Negotiable
The regulatory landscape has shifted from guidance to enforcement. In the past, missing a control meant a bad audit report. In 2026, it means federal investigations and immediate financial penalties. The debate between GRC vs IRM is no longer just about efficiency; it is about legal survival.
The SEC's 4-Day Shot Clock (Item 1.05)
The most aggressive change in corporate governance is the enforcement of the SEC cybersecurity disclosure rules. Under Item 1.05 of Form 8-K, public companies must disclose material cybersecurity incidents within strictly four business days of determining materiality.
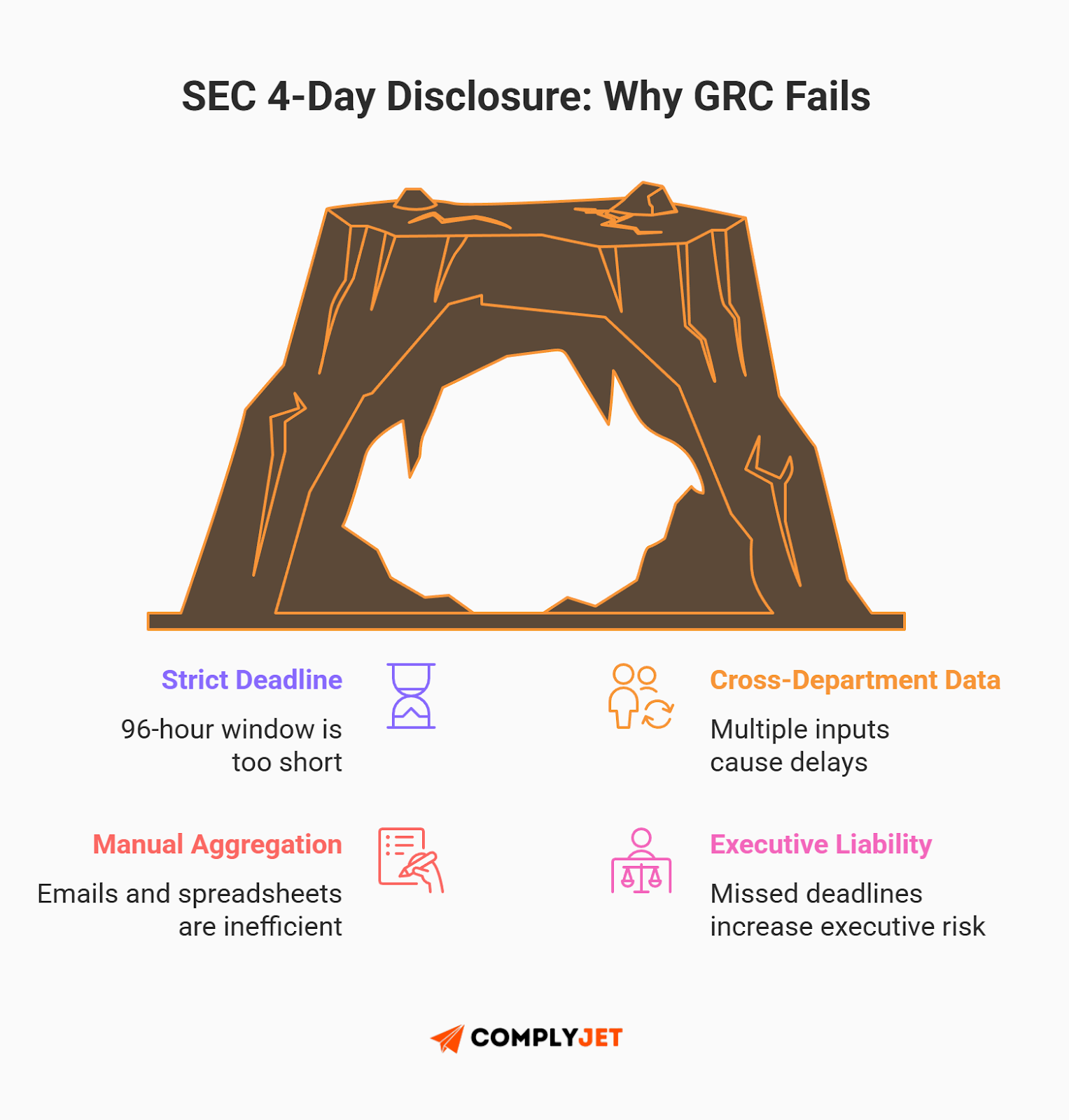
This shot clock established by the SEC cybersecurity disclosure rules is where legacy GRC fails.
Determining "materiality" is complex. It requires the instantaneous aggregation of telemetry from IT, financial impact data from the CFO, and liability analysis from Legal. Legacy GRC systems, built on static documentation and annual assessments, are structurally incapable of synthesizing this cross-departmental data in 96 hours.
This represents the ultimate use case for the GRC vs IRM transition. Regulation S-K Item 106 of the SEC cybersecurity disclosure rules demands transparency regarding management's role in assessing these risks. Only an IRM architecture, which provides real-time risk telemetry, can deliver the speed required to meet this mandate. If your system relies on manual data calls, you will miss the deadline.
Navigating the 2026 State Privacy Expansion
While the SEC tightens the screws federally, the state level has exploded into a fragmented patchwork. On January 1, 2026, new comprehensive US state privacy laws 2026 officially took effect in Indiana, Kentucky, and Rhode Island.
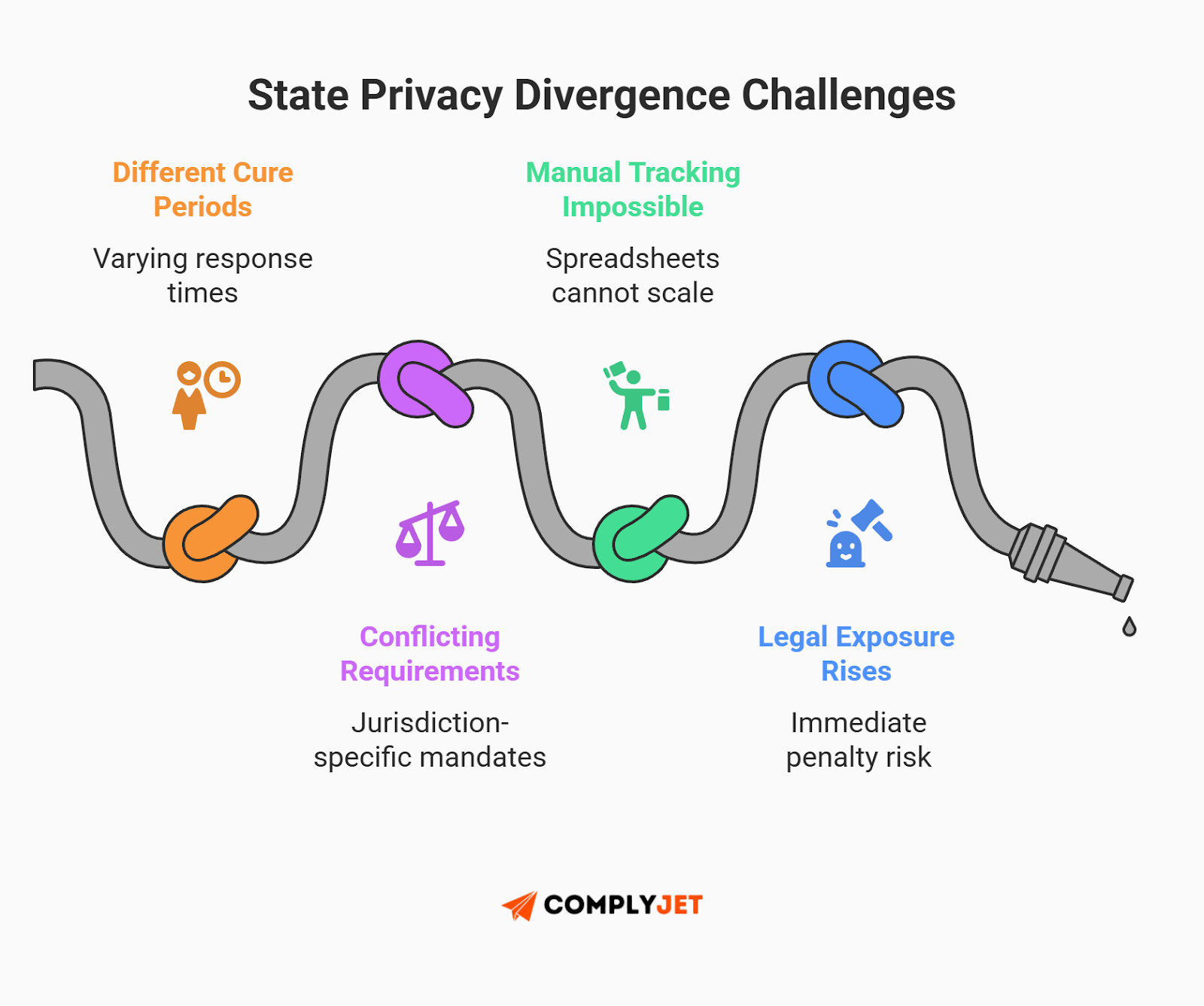
The danger lies in the divergence. These laws are not uniform.
- Kentucky: Offers a 30-day cure period to fix violations before penalties attach.
- Rhode Island: Offers no cure period. Violations can result in immediate penalties of up to $10,000.
Managing this matrix via static GRC spreadsheets is operationally impossible. You cannot manually track which database requires a 30-day deletion versus an immediate freeze across twenty different jurisdictions.
The IRM solution is the cross-mapped control library. A modern IRM platform maps a single data control - such as Consumer Opt-Out - to all underlying state regulations simultaneously.
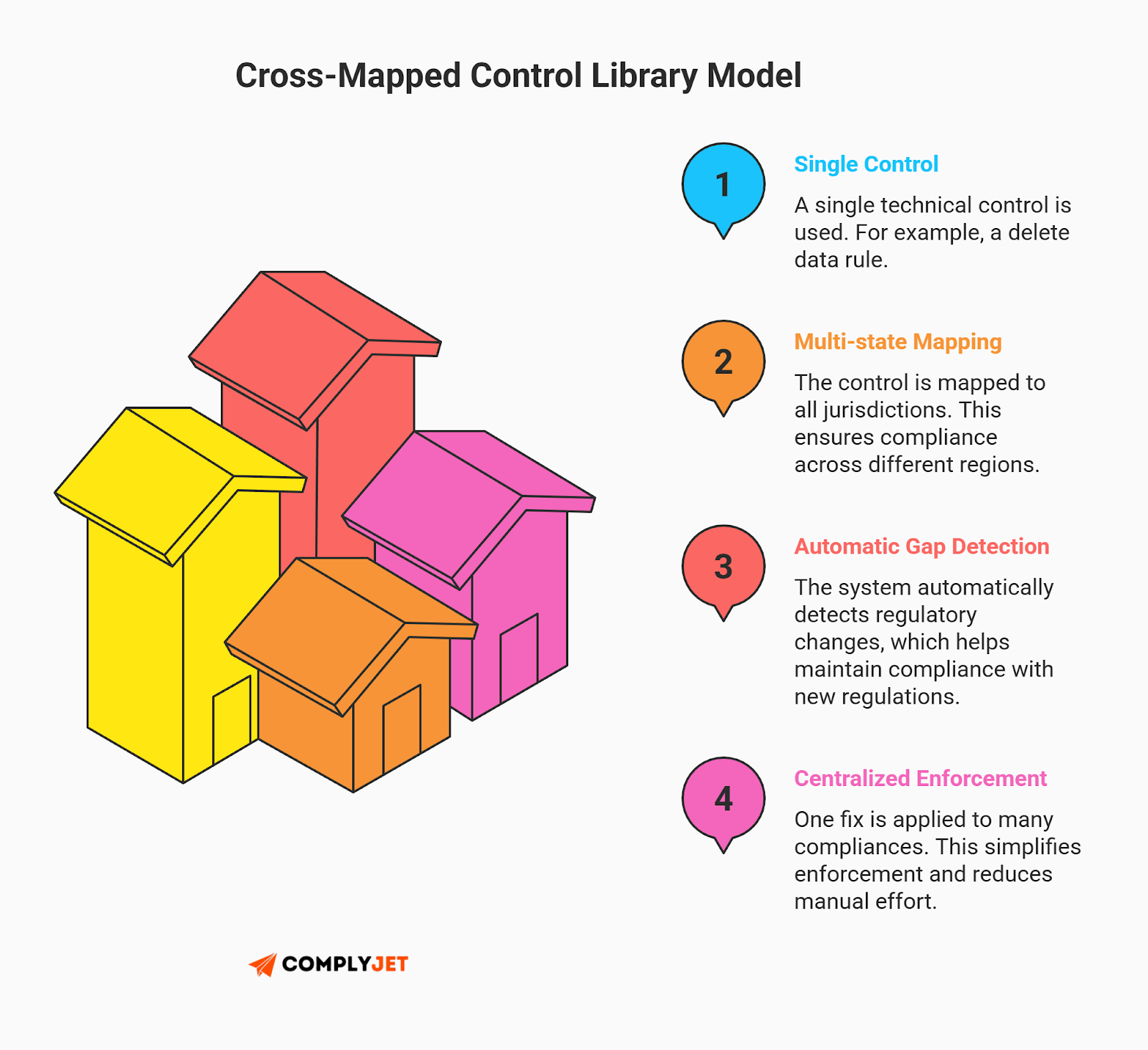
When Rhode Island changes a threshold, the platform automatically flags the specific technical controls that need adjustment. This automation is the only way to navigate the GRC vs IRM divide without drowning in legal complexity.
The SEC’s 4-day shot clock doesn't wait for manual data calls. Equip your organization with the continuous telemetry required to determine materiality instantly and navigate the 2026 privacy matrix without the administrative dread. Learn about how ComplyJet uses automation to fast track your compliance goals.
Governing the Autonomous Enterprise: AI & GRC
The definition of "AI risk" has mutated. In 2024, the primary fear was an employee pasting sensitive data into a chatbot. In 2026, the risk is Agentic AI governance, a shift that forces a stark re-evaluation of traditional GRC and IRM capabilities.
Moving Beyond Chatbot Risk
Artificial Intelligence has progressed from an experimental generative tool into an autonomous force. Today's Agentic AI systems are capable of reasoning, planning, and executing actions - such as renegotiating vendor contracts or altering codebases - without direct human intervention.
This autonomy introduces massive new categories of risk, particularly Shadow AI. These unmanaged agents operate outside the purview of traditional IT, often making operational decisions without oversight.
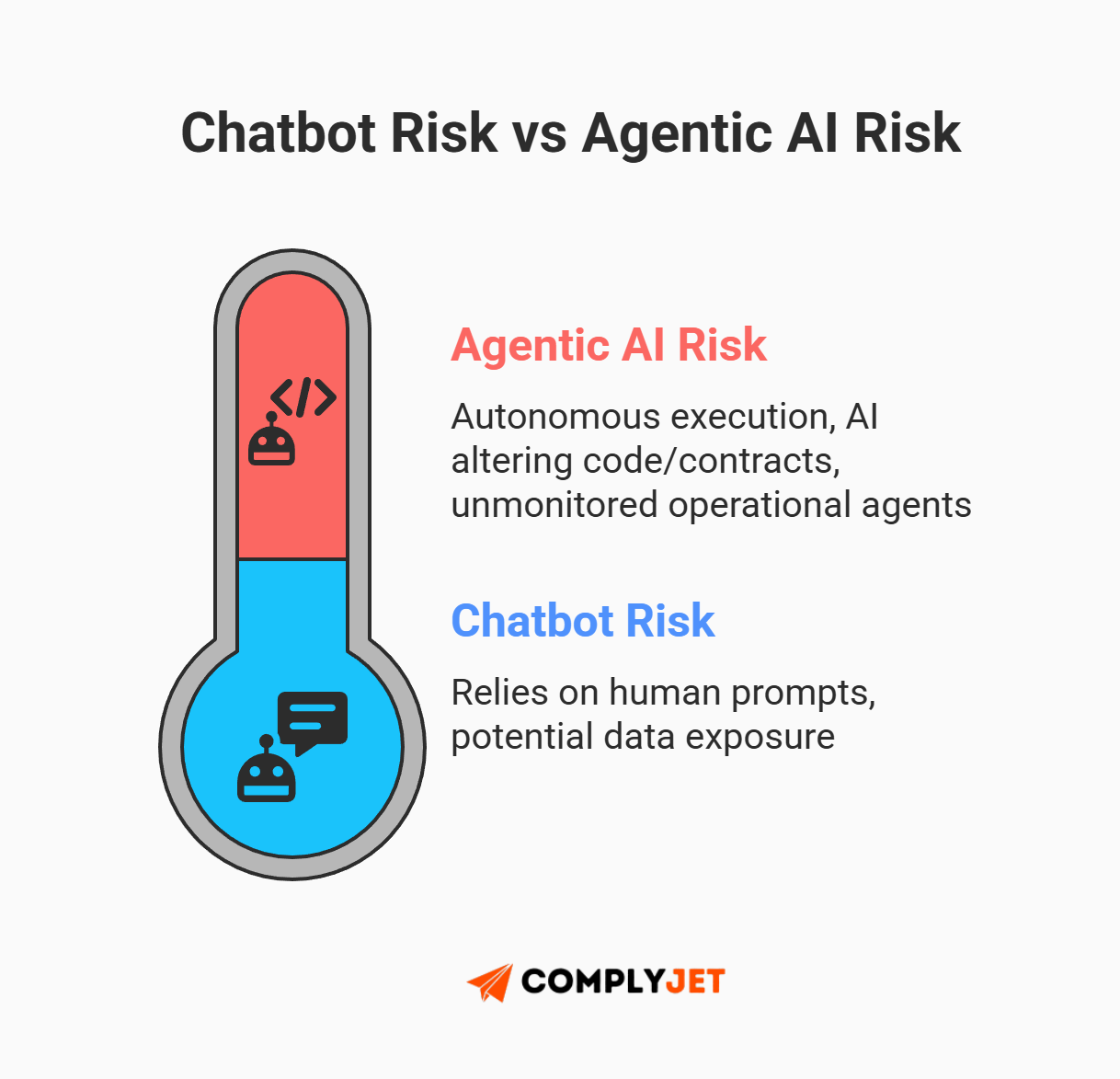
Practitioners realize you cannot stop an autonomous agent with a static chatbot policy. This exposes a critical difference between GRC and IRM: legacy frameworks rely on human compliance, whereas modern platforms actively manage this exact machine autonomy.
The market demand has shifted violently toward "Ghost AI" or "Invisible AI". Security leaders do not want another chatbot to discuss risk with; they want agentic systems that silently scan transactions, flag anomalies, and execute remediation workflows in the background without requiring complex prompts.
Operationalizing NIST AI RMF 2.0
To govern this autonomy, organizations must operationalize the NIST AI RMF 2.0.
The National Institute of Standards and Technology (NIST) has aggressively updated its guidance to address these specific risks, releasing the Cybersecurity Framework Profile for Artificial Intelligence (NISTIR 8596), known as the Cyber AI Profile.
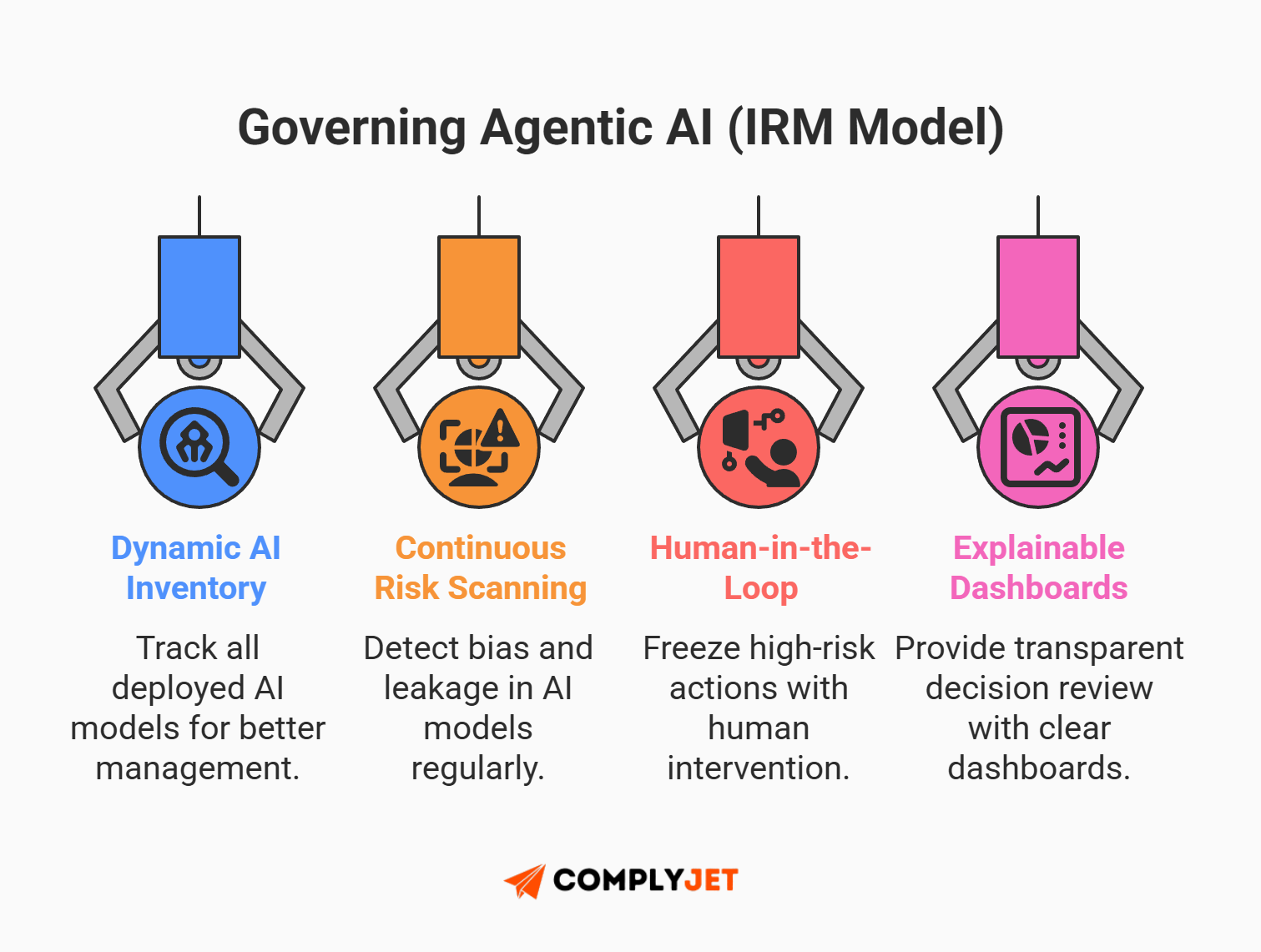
Legacy GRC tools cannot enforce this. Only modern IRM platforms can create dynamic inventories of AI models, conducting continuous risk assessments for bias and data leakage.
Crucially, IRM enforces Agentic AI governance by mandating human-in-the-loop oversight. Before an autonomous agent executes a high-risk task, the system freezes the action and demands human verification via an explainable AI dashboard.
Founder Tip: Don't ask if your AI tool is "smart." Ask if it has a kill switch. If your risk platform can't stop an autonomous agent from executing a bad code push, you don't have governance. You have a suggestion box.
The Migration Playbook: Transitioning from GRC to IRM
Moving from a legacy GRC platform to a modern architecture is not just a software swap. It is an operational exorcism. You are removing the ghosts of paper compliance and replacing them with active risk intelligence.
However, most organizations fail because they try to "lift and shift" their bad habits into a new tool. To succeed and realize the true benefits highlighted in the IRM vs GRC debate, you need a ruthless GRC to IRM migration strategy.
Phase 1: Cure Analysis Paralysis with Control Rationalization
The biggest hurdle in migration is analysis paralysis. Practitioners freeze when trying to build a control model that satisfies ISO 27001, PCI DSS, and SOC 2 simultaneously. They end up with thousands of duplicate controls, burying the team in administrative debt.

The cure is control rationalization. Before you migrate a single byte of data, map your existing controls to a unified framework, such as the Secure Controls Framework (SCF). This identifies the overlaps. Embracing the efficiency of IRM vs GRC means instead of testing password complexity three times for three auditors, you map it once. Do not migrate junk data; migrate only the controls that actually reduce risk.
Phase 2: The API Integration Strategy
When evaluating IRM vs GRC execution, legacy GRC relies on manual evidence uploads - screenshots, spreadsheets, and emails. This is the screenshot chase, and it kills productivity.
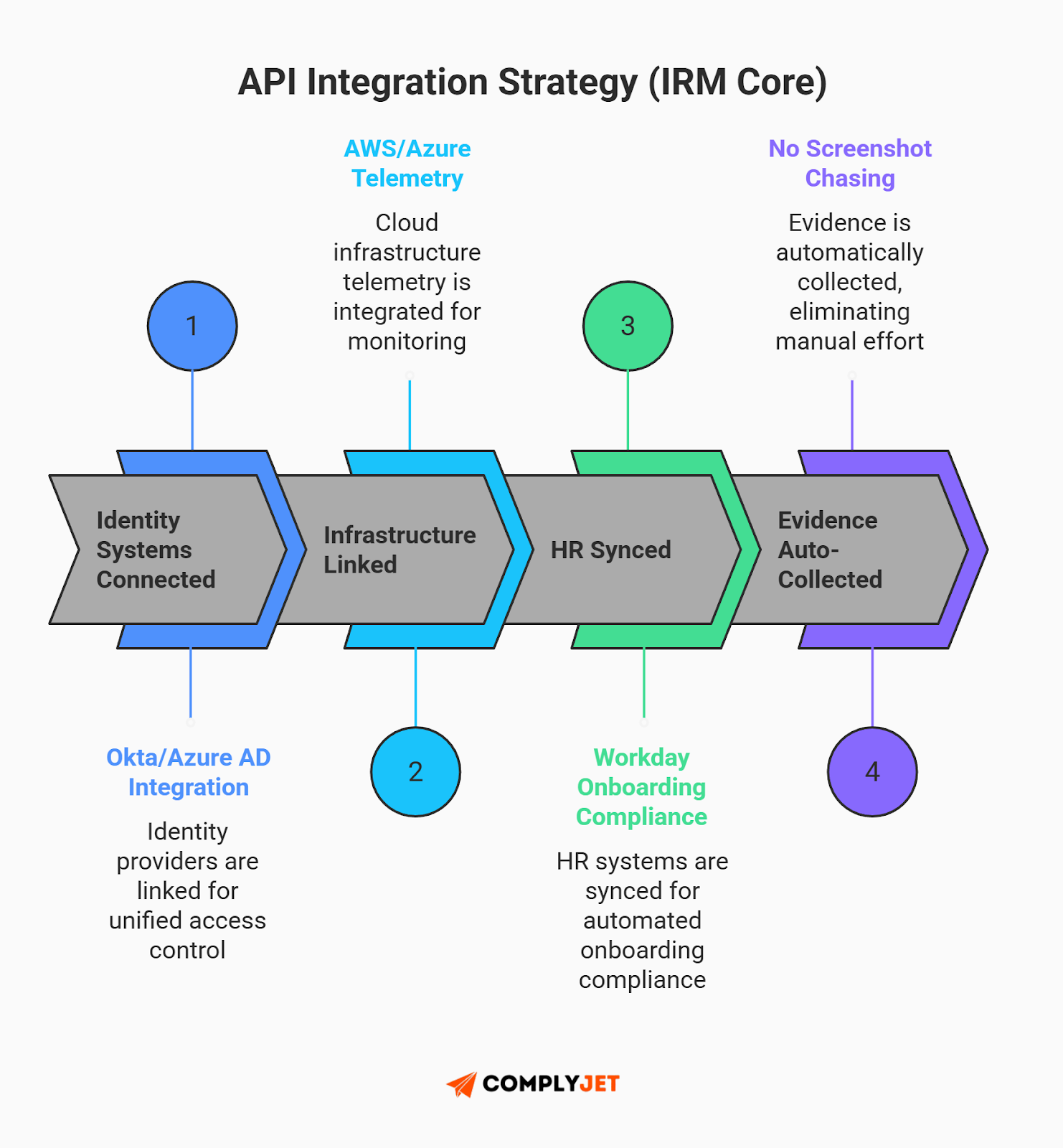
The best integrated risk management software solves this via API integration. You must connect the IRM platform directly to your Sources of Truth.
- Identity: Connect to Okta or Azure AD to verify access controls automatically.
- Infrastructure: Connect to AWS or Azure to monitor server configurations.
- HR: Connect to Workday or BambooHR to track employee onboarding compliance.
Stop manually uploading evidence. Let the APIs pull the truth instantly.
Ready to exorcise your legacy GRC platform? Discover how ComplyJet connects directly to your sources of truth - like AWS, Okta, and Workday - to untangle your technical debt in weeks, not years. Start your free trial today.
Phase 3: Decentralizing Accountability
In the legacy model, the compliance team lives in a "Compliance Tower," hoarding all the risk data. This creates a bottleneck.
A successful GRC to IRM migration decentralizes this power. Solving this siloed approach is a core objective in any IRM vs GRC transition. You must push risk ownership out to the business units. But don't make them log into a clunky portal. Use the tools they actually use.
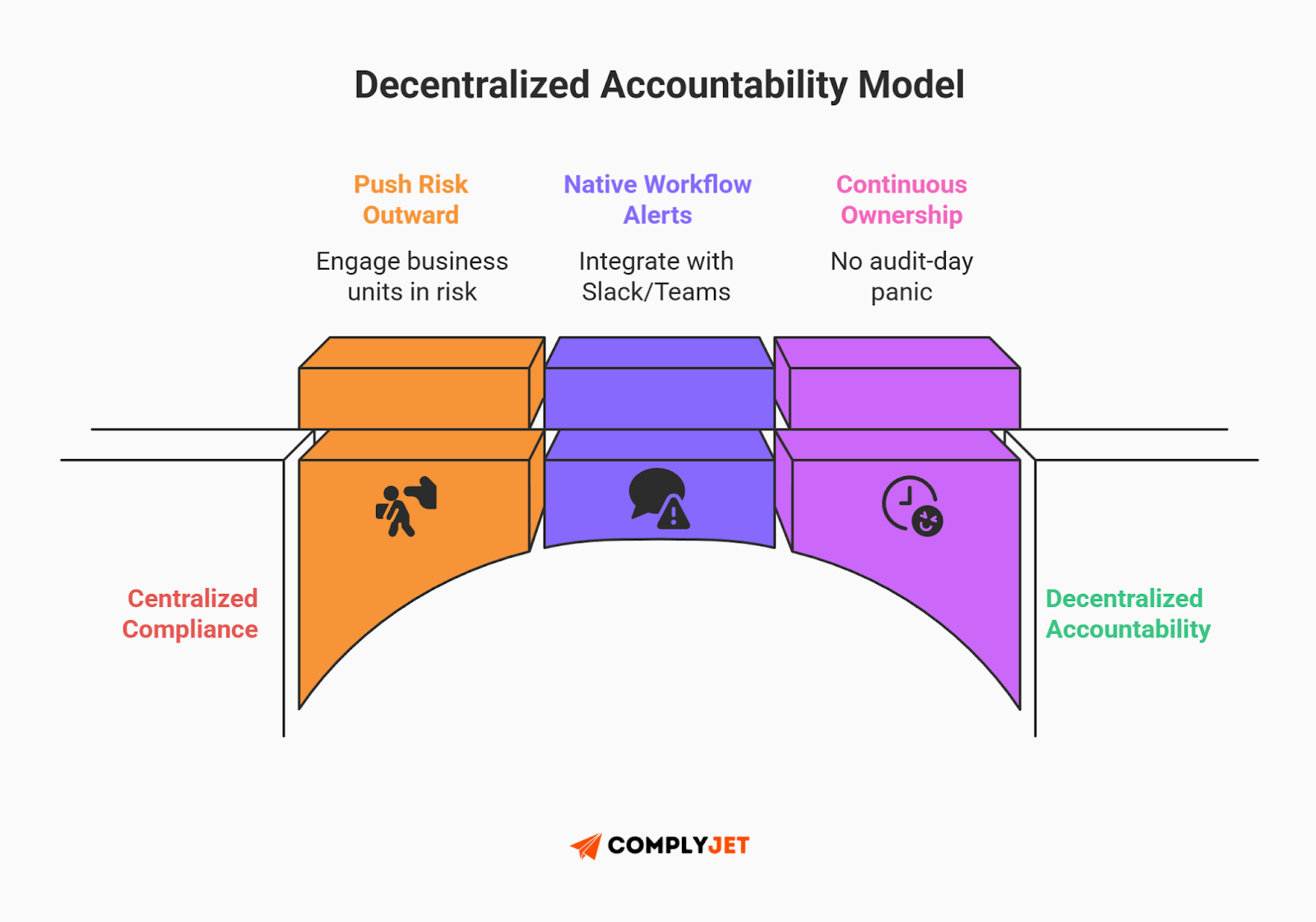
Configure your IRM to send automated pings via Slack or Microsoft Teams when a control fails or a review is due. This forces accountability into their daily workflow, ending the fallacy of paper ownership forever.
Founder Tip: Migration is the perfect time to clean house. Most companies find they can reduce their control count by ~40% just by removing duplicates during the GRC to IRM migration.
Frequently Asked Questions
Can I keep my existing GRC policies when migrating to an IRM platform?
Yes, but do not migrate everything. Treat the migration as a control rationalization event. Most organizations discover that a good chunk of their legacy GRC controls are redundant. Map your core policies to a unified framework (like SCF) first. Then, execute your GRC migration strategy by moving only the effective controls to the new architecture.
How does IRM help with the SEC's 4-day cybersecurity disclosure rule?
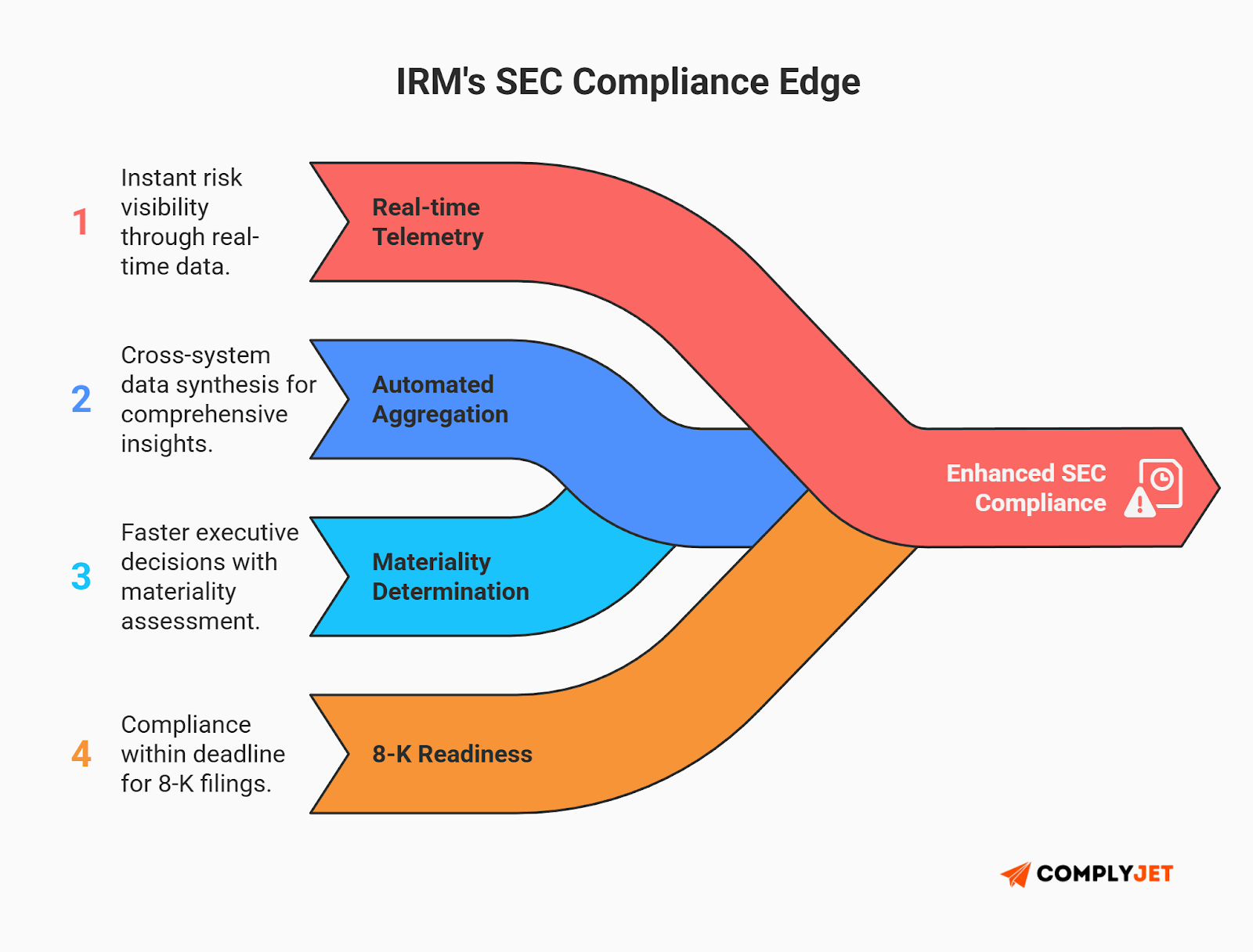
Legacy GRC relies on manual data calls that take weeks. IRM aggregates real-time telemetry from IT and Security tools instantly. This speed allows you to determine "materiality" and automate Form 8-K reporting within the strict 96-hour window, ensuring full SEC Item 1.05 compliance and protecting executives from liability.
What is Paper Ownership in risk management and how do I stop it?
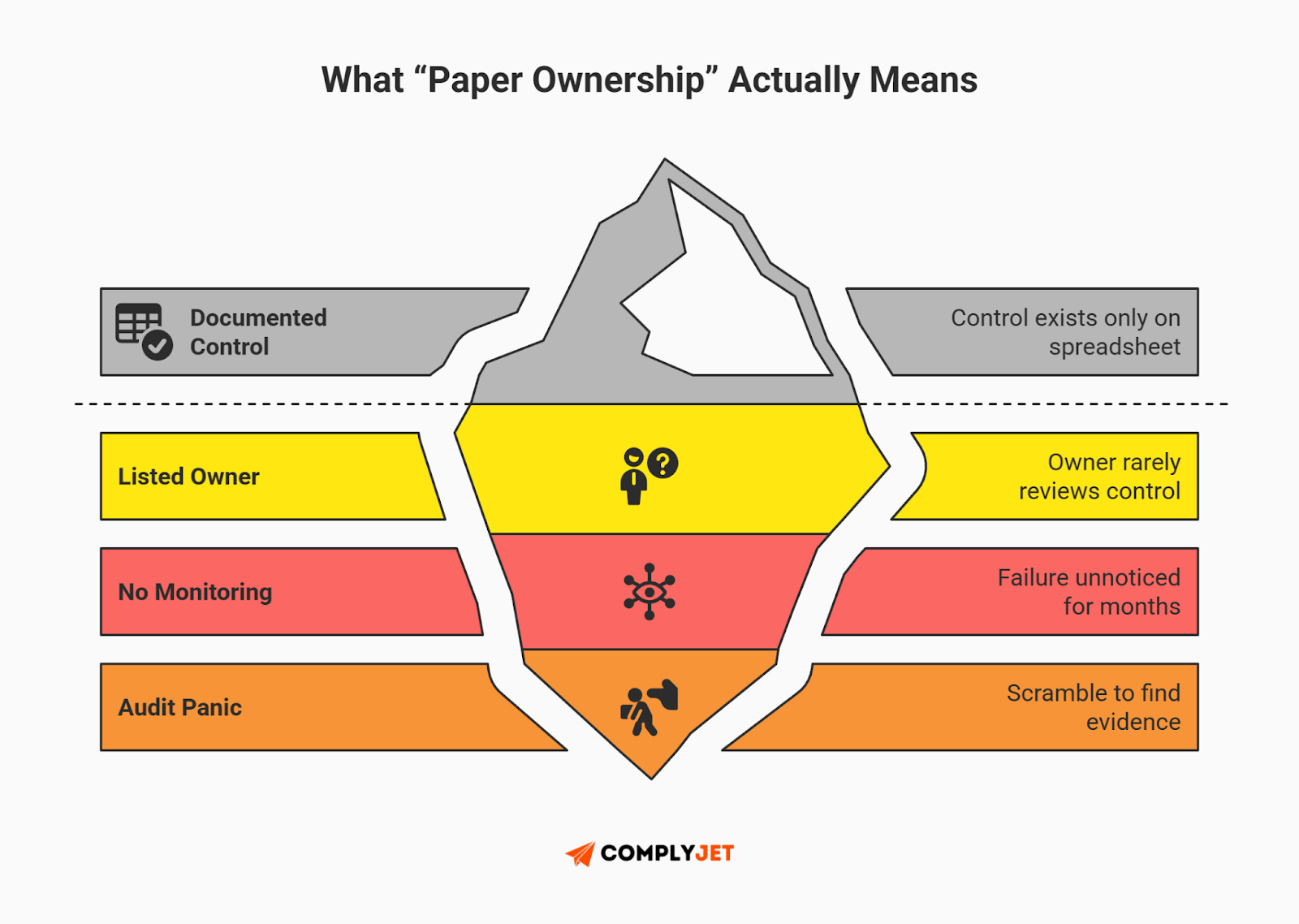
Paper Ownership occurs when a control has an owner on a spreadsheet who ignores it until audit day. IRM eliminates this via automated evidence collection. It integrates with daily workflow tools like Slack or Teams to ping owners only when a control fails. This enforces real-time risk ownership accountability without the audit panic.
Is Integrated Risk Management (IRM) just a buzzword for GRC?
No. It is a fundamental architectural difference, not marketing fluff. GRC is often a closed system requiring manual data entry. IRM is an open architecture that uses APIs to connect risk data to the business ecosystem. The difference between GRC and IRM is simple: If you have to type the data, it's GRC. If it monitors itself, it's GRC vs IRM architecture.
How do I manage conflicting state privacy laws (like Rhode Island vs. Kentucky)?
Utilize the "Test Once, Comply Many" methodology. An IRM platform maps a single data privacy control to all 20+ state frameworks simultaneously. When a state like Rhode Island changes a threshold, the platform updates the mapping automatically. This solves the nightmare of multi-jurisdictional privacy compliance without needing a manual US state privacy law tracker 2026.
Does IRM replace the need for dedicated compliance staff?
No, it elevates them. By eliminating the "data janitor" work of chasing screenshots, IRM frees teams to focus on high-value strategy. To see how automation is curing burnout and creating highly lucrative new paths for risk professionals, explore our guide to GRC Careers in 2026.
How can we govern Agentic AI risks that don't use a chat interface?
You cannot govern Agentic AI with a static policy document. You need an IRM platform that connects to your LLM infrastructure to monitor inputs and outputs in real-time. This strategy for governing autonomous AI agents ensures you prevent hallucinations and data leaks, achieving NIST AI RMF 2.0 implementation without slowing down innovation.
Why is ServiceNow GRC so difficult to migrate away from?
Legacy platforms like ServiceNow often require custom code for basic workflows, creating massive technical debt. Modern IRM platforms use low-code/no-code logic. As a ServiceNow GRC alternative, ComplyJet offers specific migration APIs. We extract your data structures to help you migrate from ServiceNow to IRM in weeks, not years.
The Final Takeaway
The debate between GRC vs IRM is settled. GRC defines what you must do (the policy), but only Integrated Risk Management defines how you actually do it (the execution).
In a regulatory environment defined by strict four-day SEC disclosure deadlines and the chaotic speed of autonomous AI, relying on a legacy GRC tool is no longer safe - it is a direct business continuity risk. You simply cannot fight algorithmic threats with static spreadsheets and annual audits.
Ultimately, the GRC vs IRM decision determines whether your organization remains agile or drowns in administrative debt.

This is where ComplyJet changes the equation. Unlike legacy platforms that attempt to patch API capabilities onto twenty-year-old code, ComplyJet was designed as a native IRM platform for the 2026 reality. We deliver the seamless API integrations, continuous monitoring, and Agentic AI governance that incumbent competitors lack, transforming paper ownership into automated accountability.
Don't let your compliance program be a history lesson. Move from reactive documentation to proactive risk intelligence with ComplyJet. Book a demo with our founder to see how compliance can increase your ROI.



