Data privacy has shifted from a legal requirement to a customer expectation. Users now prefer to read cookie banners and question data practices, and are serious about their data privacy. If you own a SaaS platform, run marketing, or handle EU user data in any way, your GDPR posture needs to be transparent to your customers, your enterprise buyers, and your regulators.
GDPR compliance is no longer a legal formality you can ignore or avoid. It is an ongoing operational commitment, and without a structured strategy, the gaps in your program will eventually result in heavy fines for your business (for instance, recent enforcement actions include a €530 million fine for TikTok and a record €1.2 billion penalty against Meta).
The common misunderstanding among USA-based companies is that the headquarters is on American land and there is no need to be GDPR compliant. And that’s how the USA-based businesses pay high fines.
According to GDPR, if your business is dealing with EU region user data, then the business must be GDPR compliant as per EU regulators.
So, in this guide, you will go through 10 proven GDPR compliance strategies covering audits, consent, breach response, vendor risks, and automation. In addition, sections for SaaS companies, marketing teams, and businesses navigating GDPR alongside HIPAA are covered here.
Without a structured strategy, the gaps in your program will eventually result in heavy fines for your business. Book a free 30-minute GDPR audit with our team. We'll map your current exposure before you read another word of this guide.
GDPR Compliance: Meaning, Scope, and the Business Case

GDPR compliance means adhering to the requirements defined in the General Data Protection Regulation (EU) 2016/679. In simple terms, collect personal data lawfully, safeguard it, respect user rights, and be able to demonstrate compliance when required.
The regulation applies globally. Any organization accessing/dealing with EU resident data falls within scope, regardless of location.
This includes:
- US-based e-commerce businesses with European customers.
- SaaS platforms serving EU users.
- agencies processing data on behalf of EU clients.
Operationally, compliance rests on four pillars:
- Lawful data collection.
- Accountability through documentation.
- Active management of user rights.
- Strong data security practices and clear business incentives.
Business case for treating GDPR compliance as a strategic asset rather than a burden:
Customer trust: 62% of UK consumers reported feeling more comfortable sharing data after GDPR came into effect (DMA). In a market where data breaches make front-page news, demonstrated compliance is a trust signal.
Enterprise sales enablement: Enterprise buyers now routinely require GDPR compliance evidence, DPAs, sub-processor lists, and privacy policies before signing contracts.
Global market access: GDPR has become the global baseline for data privacy. Brazil's LGPD, India's DPDP Act, and a growing number of US state privacy laws are all modelled on GDPR principles. Getting GDPR right means less rework when other regulations land.
The takeaway is that GDPR compliance isn’t a one-time task. It’s a continuous, structured effort.
The 10 Best GDPR Compliance Strategies for 2026
In an era of rapid AI integration and evolving data regulations, staying compliant requires more than just a checklist; it demands a proactive, future-proof approach.
As we look toward 2026, these ten GDPR compliance implementation strategies will help your organization transform GDPR requirements from a legal burden into a powerful engine for building global customer trust.
Strategy 1: Conduct a Full Data Audit and Build a Data Map
You can’t really protect what you haven’t identified yet. And that’s where most organizations struggle. There are always gaps, such as legacy CRM entries sitting untouched, analytics tools collecting more than expected, and HR platforms syncing employee data across regions. A data audit makes those gaps visible.
At a basic level, you’re trying to answer:
- What data do you collect?
- Where is it stored?
- Who has access?
- Why are you collecting it (legal basis)?
- How long do you keep it?
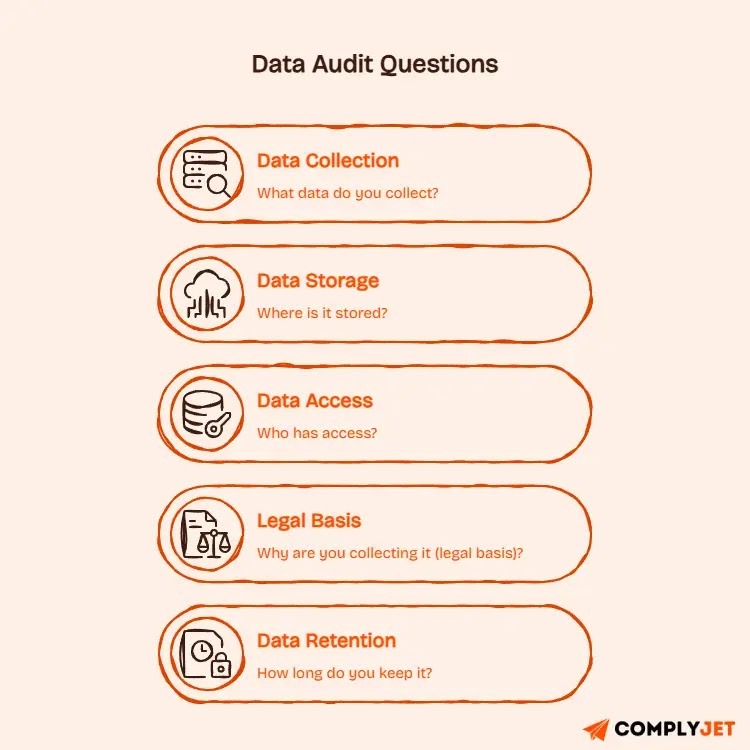
Once you’ve mapped this out, you end up with your Record of Processing Activities (ROPA). Under the General Data Protection Regulation, this isn’t optional for many organizations, especially if you're aligning with broader frameworks like a SOC 2 compliance checklist.
It’s essentially your data map, and regulators will ask for it.
Some data mapping tools, such as Complyjet, Privado.ai, and BigID, are all built to surface data across systems. But even a spreadsheet works if you’re early.
Action step: Assign data inventory owners by department, not just IT. Marketing, HR, finance, and product all handle personal data differently and need to be represented in your ROPA. Review and update quarterly.
Strategy 2: Establish a Lawful Basis for Every Processing Activity
Under Article 6 of the GDPR, you can’t just start handling personal data and figure out the ‘why’ later. You need a documented legal reason locked in before you hit go.
It sounds like a technicality, but ‘implied’ permission is a major red flag for regulators and a leading cause of those massive fines you see in the news, which we have discussed in our GDPR compliance guide.
The Six Paths to Compliance
‘Consent’ is the one everyone talks about, but it’s actually just one of six options. Depending on what you're doing, another path might actually be a better fit:
- Consent: Must be crystal clear, specific, and easy to take back.
- Contract: You need the data to actually deliver what the customer paid for.
- Legal Obligation: You’re required by law to keep or process this info.
- Vital Interests: It’s literally a matter of life or death (rare in business!).
- Public Task: You’re performing a job for the public good/official authority.
- Legitimate Interests: You have a solid business reason that doesn’t override the user's privacy.
Note: Legitimate interests (LIA) require a balancing test. You can't just claim it; you have to prove it and write it down.
If consent is the route you choose, ‘good enough’ isn't good enough anymore. Here is how to keep it user-friendly and legal:
- Be Specific: Don't bundle everything together. Let people choose ‘Yes’ to marketing but ‘No’ to profiling.
- Keep Receipts: Use a Consent Management Platform (CMP) to log exactly when and how someone opted in.
- Make it Easy to Quit: If it took one click to join, it should take one click to leave. Don't hide the ‘unsubscribe’ or ‘withdraw’ button in a maze of settings.
The 2026 Update: Google Consent Mode
If you're running ads or using analytics, pay attention: Google Consent Mode v2 has been the standard since early 2024.
Even now, over two years later, about 67% of sites are still getting it wrong. The biggest mistake? Letting your analytics (GA4) or ads fire the moment a page loads, before the user has even clicked ‘Accept’ on your cookie banner. If you’re using Google’s tools, double-check that.
Strategy 3: Embed Privacy by Design and Default
Under Article 25 of the GDPR, privacy isn’t a ‘fix it later’ task. You’re actually required to bake data protection into your systems from day one. Think of it like building a house; it’s much easier (and cheaper) to install the plumbing while the walls are open than to try to add it after the move-in date.
The Core Mindset - Privacy by Design:
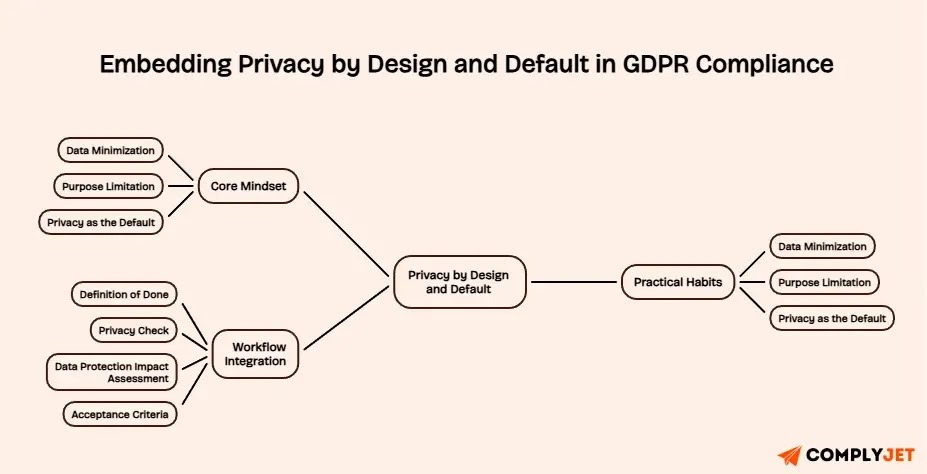
Instead of seeing privacy as a roadblock to innovation, think of it as a quality standard. In practice, this means moving away from "move fast and break things" and toward these three habits:
Data Minimization: If you don’t absolutely need a certain piece of information to make the feature work, don’t ask for it. If your sign-up form asks for a birthday but you don’t have an age-gate, you’re just creating a liability.
Purpose Limitation: Don’t be a data hoarder. If you collected an email address to send a receipt, you can’t quietly slip it into a profiling database for ads later on without a fresh conversation with the user.
Privacy as the Default: This is a big one for SaaS. The most "private" setting should be the standard. Users shouldn't have to go on a treasure hunt through a settings menu just to stop their data from being shared.
- Making it Work in Your Workflow. You don’t need a massive legal team to make this happen; you just need to update your ‘Definition of Done.’
- Add a quick "Privacy Check" to every product sprint. Does this new feature collect new data? If so, why?
- If you’re launching something high-stakes like automated decision-making or handling sensitive health data, run a Data Protection Impact Assessment. It’s basically a formal "what could go wrong?" brainstorm, similar to structured approaches like risk quantification, that keeps you out of trouble later.
- Acceptance criteria for dev teams: a feature isn't "done" until the privacy settings are verified and the data flow is documented.
Add a simple “Privacy Check” to every product sprint: does this feature collect new data, and if so, why?
Build it into your workflow automatically. Start your free trial and see compliance checks run alongside your release cycle, without manual overhead.
Strategy 4: Build a Data Subject Rights Workflow
The GDPR gives people eight specific rights over their data, from the right to see what you have on them to the right to be forgotten entirely. You typically have 30 days to respond, but don't let that long window fool you.
If you're managing these through a cluttered "info@" inbox, especially when responding to external validation requests like customer or vendor security questionnaires, it can quickly turn a single request into a fire drill.”
In 2026, people are incredibly savvy about their data. Complaints for ignored requests are at an all-time high, so having an "ad hoc" process is basically an invitation for a regulatory audit.
Building a proper DSAR workflow means:
Scaling your response process is about removing friction, both for your team and your users.
- Make the Front Door Visible: Don't hide your request form in the footer of a sub-page. Create a clear "Privacy Request" page. It shows you’re transparent and saves your support team from answering "how do I delete my account?" ten times a day.
- Verify, then Deliver: You have a legal duty to make sure you aren't handing data to an impostor. Verify identity early, but keep it simple.
- Set a "Buffer" Deadline: The law says 30 days, but your internal goal should be 25 days. That five-day safety net is a lifesaver if a complex request pops up or a key team member is out sick.
- Log Everything: Keep a clear trail of when a request came in, what was asked, and when it was resolved. If a regulator ever knocks, this log is your best friend.
When to Bring in the DSAR Automation?
If you’re handling more than a handful of requests a month, manual searching is a losing game. Tools like Complyjet, OneTrust, Transcend, or DataGrail can automate the data discovery process, pulling a user’s info from all your different siloes (Slack, AWS, CRM) in seconds. At a certain scale, automation isn't just a luxury; it’s the only way to stay compliant.
Strategy 5: Manage Third-Party Vendor Risk
One of the biggest surprises for growing companies is realizing that under the GDPR, you can’t just point the finger at a vendor if something goes wrong. If your email tool, CRM, or cloud provider has a breach, you are still on the hook. Every third-party tool you plug into your stack is essentially an extension of your own company's privacy footprint.
The "Must-Have" Paperwork: The DPA

Before you send a single byte of customer data to a vendor, Article 28 says you need a “Data Processing Agreement (DPA), similar in structure to a Business Associate Agreement under HIPAA when handling regulated data”. Think of this as a "rules of engagement" contract. It should clearly state:
- What data are they handling and why?
- How are they keeping it secure?
- What happens if they have a breach?
- What do they do with the data once your contract ends (delete or return it)?
Before you send a single byte of customer data to a vendor, Article 28 says you need a Data Processing Agreement in place. We provide ready-to-use DPA templates, a sub-processor tracking dashboard, and automated vendor risk tiers across every plan. See what's included at each pricing tier.
A Practical Playbook for Vendor Risk
You don’t need to audit every single tiny plugin with the same intensity. Use a "tier" approach aligned with a structured TPRM lifecycle to stay sane :
- The Inventory: Keep a simple list of every tool that touches personal data. If it’s not on the list, it shouldn't have access.
- Tier Your Risks:
- High Risk: Your HR system, CRM, or cloud hosting (AWS/Azure). These need deep security reviews and solid DPAs.
- Medium Risk: Analytics and marketing tools.
- Low Risk: Tools that don't really touch personal info (like a project management tool where you only use nicknames).
- Due Diligence: Before signing up for a new "shiny" tool, ask for their security whitepaper and check if their DPA is actually GDPR-compliant.
- Annual Check-ups: For your "High Risk" vendors, don't just set it and forget it. Do a quick check once a year or at renewal time to make sure their security standards haven't slipped.
Red flags when assessing vendors
No published DPA template, no sub-processor disclosure page, vague security statements without specifics, or a privacy policy that has not been updated since 2018.
Strategy 6: Implement Technical and Organizational Security Controls
Under Article 32 of the GDPR, the law doesn't expect you to be "unhackable". It expects you to take appropriate technical and organizational measures.
Security isn't one-size-fits-all. If you're handling medical records or credit card info, the bar is much higher than if you’re just managing a newsletter list. The goal isn't necessarily a perfect system, but a defensible one.
If a regulator asks why you chose a specific security setup, you need to be able to show that it matches the sensitivity of the data you’re protecting.
The Technical + Human Essentials
These are the core technical controls of modern data security. If you’re missing these, it’s much, much harder to defend your setup during an audit, especially when mapped against standardized frameworks like SOC 2 controls:
- Encryption (The Basics): Data should be scrambled both while at rest (AES-256) and in transit (TLS 1.2 or higher).
- The "Need to Know" Rule (RBAC): Not everyone in the company needs access to everything. Set up Role-Based Access Control (RBAC) so employees only see the data required for their specific job.
- Multi-Factor Authentication (MFA): Multi-Factor Authentication shouldn't be optional, especially for any system that processes sensitive data or has admin privileges.
- Pseudonymization: If you’re running tests or analytics, use pseudonymization or data masking. Your dev team doesn't need to see real customer names to fix a bug in the code.
- Proactive Testing: Don’t wait for a breach to find your weak spots. Regular vulnerability scans and "penetration tests" (ethical hacking) show you’re staying ahead of the curve.
- Documented Policies: Make sure your security rules are clear and accessible.
- A "Security-First" Culture: from the CEO to the interns, takes data protection seriously, and you’ve built your strongest firewall.
- Physical Security: Secure your offices and server rooms just as carefully as you secure your cloud.
2026 Note
Several supervisory authorities, including the CNIL and the Irish DPC, have begun conducting automated backend scans of organizations under investigation. Your technical controls need to match what your privacy policy and ROPA say you do. Discrepancies between policy and practice are being flagged and fined.
Strategy 7: Develop a Data Breach Response Plan
Under Article 33, you have a 72-hour hard deadline to notify your supervisory authority once you're aware of a breach. If the risk to individuals is high (Article 34), you must also notify them directly without undue delay. Missing these windows is a standalone violation that often triggers deeper audits.
72 hours is a brutal timeframe for forensics, legal drafting, and internal triage. If you’re figuring out your response on the fly, you’ve already missed the deadline.
The Breach Response Playbook
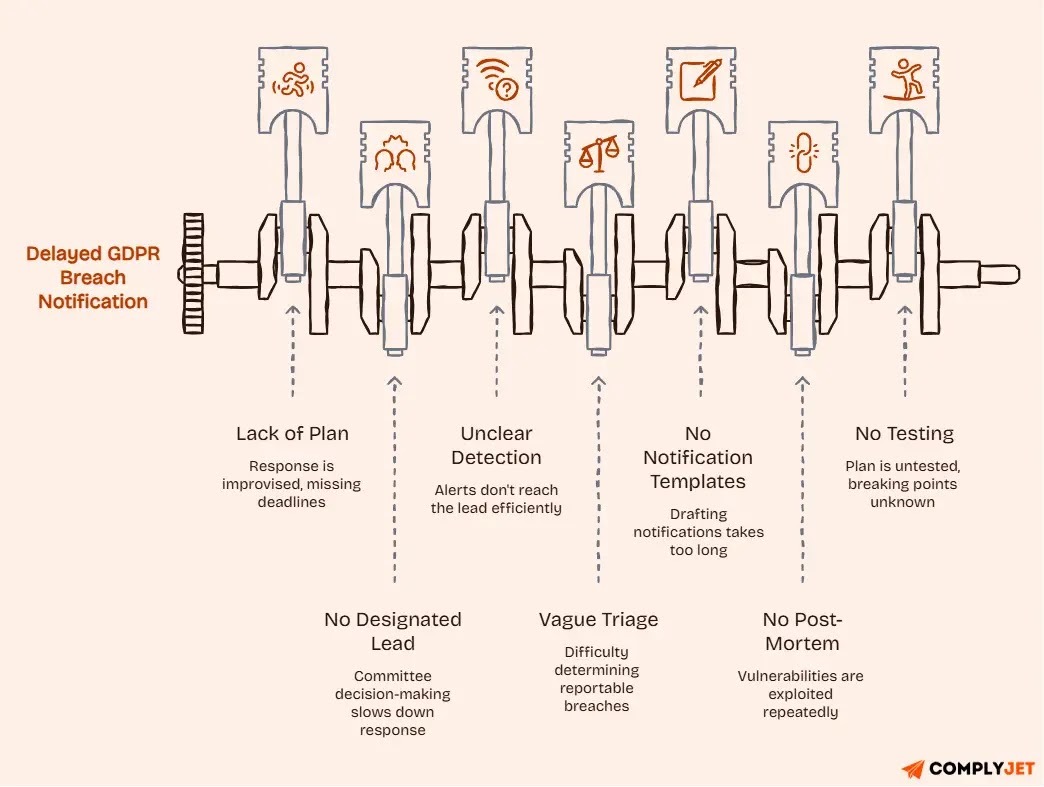
A defensible plan requires these specific mechanics:
- Designated Lead: One person owns the response. No committee-based decision-making during the first 48 hours.
- The Detection Pipeline: Clear protocols for how vendor alerts, IT logs, or staff reports reach the lead.
- Triage Criteria: A pre-set matrix to determine if a breach hits the "reportable" threshold or is a contained incident.
- Notification Blueprints: Pre-approved templates for the DPA and data subjects. You fill in the blanks; you don't draft from scratch.
- The Post-Mortem: A mandatory root-cause analysis to ensure the same vulnerability isn't exploited twice.
The Annual Stress Test
A plan is just a document until it’s tested. Run a tabletop simulation annually. Put your leadership and IT teams in a room, give them a realistic nightmare scenario, and find the breaking points in your 72-hour process before it's live.
Strategy 8: Build a GDPR Training Program for All Staff
The most technically sophisticated compliance program in the world will fail if your staff does not understand their role in it. The majority of personal data breaches originate from human error, a misdirected email, a phishing link clicked, or an unsecured file shared via personal cloud storage. Training is not a tick-box. It is a risk reduction mechanism.
GDPR training needs to reach everyone who handles personal data, not just the compliance team. That means all staff, new hires within their first 30 days, developers who need to understand privacy by design, and marketing teams who are working with consent, cookies, and email lists daily.
A well-built training program includes:
- An annual GDPR refresher for all staff covering current obligations and recent enforcement examples.
- A GDPR induction module for new hires within the first 30 days.
- Role-specific deep dives: developers on secure coding and data minimization; marketers on consent and cookie compliance; customer support on DSAR handling.
- Phishing simulations to test and reinforce security awareness.
- Clear incident reporting procedures so staff know exactly what to do if they suspect a breach.
Under Article 5(2)
The accountability principle requires you to be able to demonstrate compliance, often through structured compliance reporting and documented audit trails, not just claim it. That means tracking training completion rates and maintaining records. A DPA investigation that finds no training records is a fast route to a corrective order.
Strategy 9: Implement Continuous Monitoring and Regular GDPR Audits
GDPR compliance is not a project with a completion date. Products change, vendors change, teams grow, and regulations evolve.
A compliance program that was solid twelve months ago may have significant gaps today if it has not been actively maintained. Continuous monitoring is what separates organizations that pass audits from those that are surprised by them.
Continuous monitoring in practice means:
- Automated consent log reviews monthly checks to verify consent records are being captured and stored correctly.
- Cookie banner testing regular checks to ensure non-essential cookies are not firing before consent is registered.
- ROPA reviews quarterly updates to the Record of Processing Activities as new tools, features, and data flows are introduced.
- Vendor compliance is re-reviewed annually or on contract renewal.
For organizations handling large volumes of personal data, or those in regulated industries, this monitoring needs to be supported by a structured audit cadence:
- Internal audits: quarterly self-assessment, similar to an ISO 27001 internal audit approach covering lawful basis documentation, consent records, DSAR logs, vendor DPAs, security controls, breach response readiness, and staff training records.
- External audits: annual third-party assessment for high-risk or heavily regulated organizations.
The compliance maturity journey moves from reactive (audit-driven, fixing issues when found), to proactive (monitoring before issues surface), to embedded (where privacy is simply how the organization operates). The best GDPR compliance strategies for 2026 aim for that third stage.
Continuous GDPR compliance in big data environments adds another layer of complexity, including automated pipeline scanning, data lineage tracking, and real-time consent signal propagation across processing systems. Tools like BigID and Privado.ai are specifically built for this use case.
Strategy 10: Leverage Compliance Automation Tools
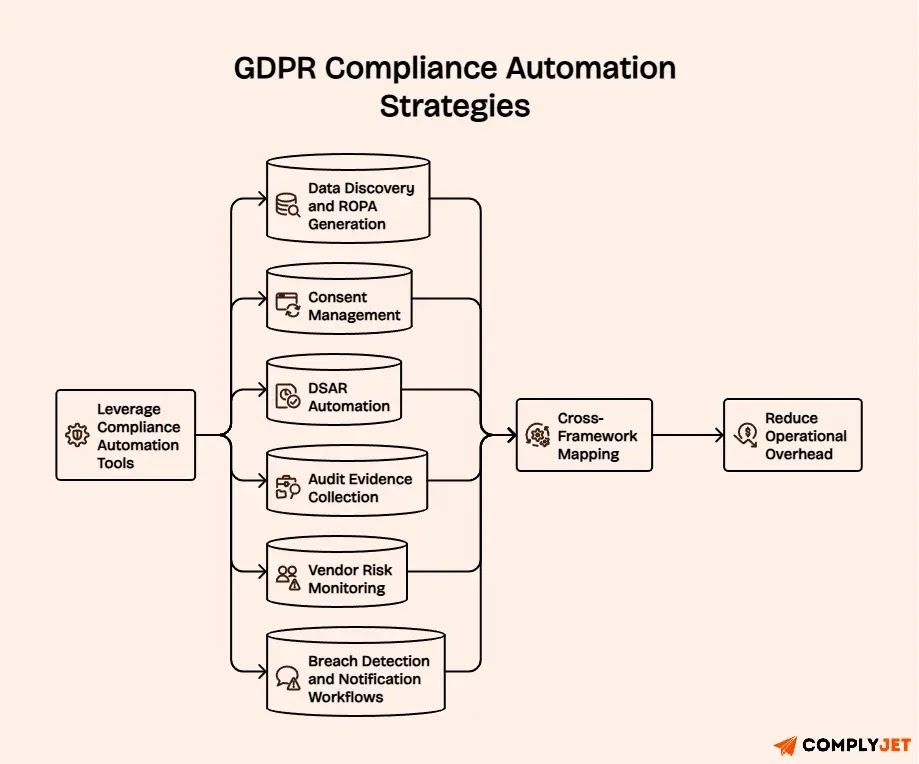
Manual GDPR compliance processes do not scale. A team of three privacy professionals cannot manually track consent across a million-user platform, review every vendor contract on renewal, or handle 200 DSAR requests a month without dropping something. Automation is no longer a nice-to-have; it is a strategic necessity for any organization operating at volume.
The areas where automation delivers the most value are:
- Data discovery and ROPA generation: automated scanning of your infrastructure to surface personal data and pre-populate your processing records.
- Consent management: real-time logging, renewal prompting, and withdrawal tracking across all channels.
- DSAR automation: intake, identity verification, task routing, fulfilment, and deadline tracking.
- Audit evidence collection: automated gathering of control evidence for internal and external audits.
- Vendor risk monitoring: ongoing tracking of third-party compliance signals and sub-processor changes.
- Breach detection and notification workflows: automated alerting and templated notification processes.
The most sophisticated platforms now offer cross-framework mapping, a single control in your system satisfies both GDPR Article 32 and a SOC 2 or ISO 27001 requirement, without duplicated effort. For SaaS companies managing multiple compliance frameworks, this alone can halve the operational overhead of maintaining compliance.
2026 trend
AI-powered compliance tools are emerging that can flag dark patterns in cookie banners, identify consent violations in real time, and detect gaps in ROPA entries automatically. These are no longer experimental; they are actively being used by compliance teams at mid-market and enterprise scale.
GDPR Compliance Strategy Snapshot for 2026
In this table, you can quickly assess which strategies have the highest impact for your organization's current compliance posture.
GDPR Compliance vs. Business Risk
Map your exposure. The six risk areas below represent the most common sources of GDPR enforcement actions and the concrete steps that address each one.
Strategies for Dual GDPR and HIPAA Compliance
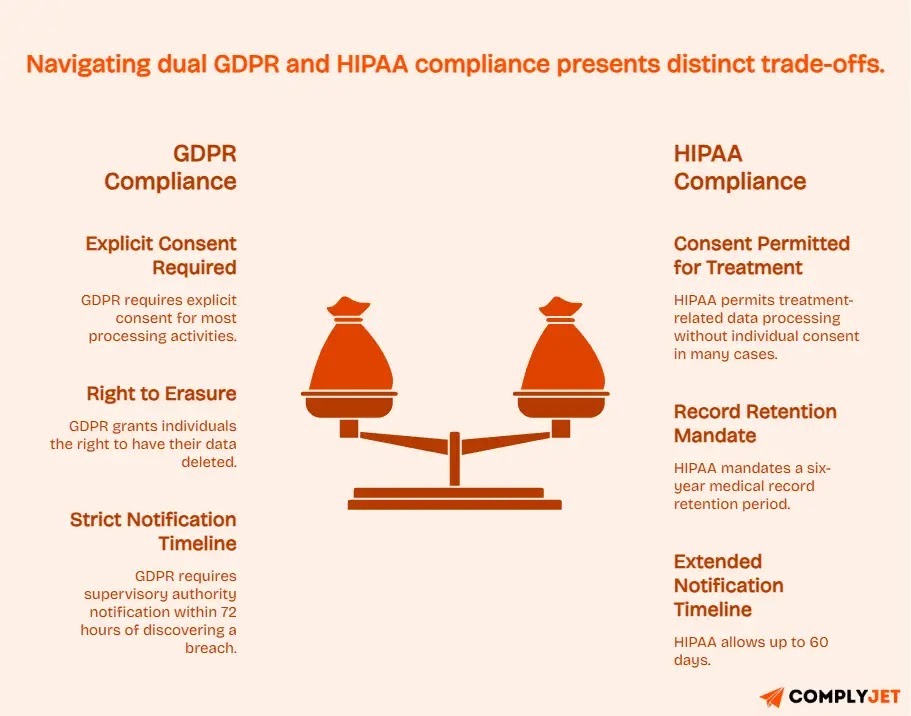
If your organization operates in digital health, healthcare SaaS, or serves both EU residents and US patients, you are navigating two of the world's most demanding data protection frameworks simultaneously.
GDPR governs the personal data of EU residents. HIPAA governs protected health information (PHI) in the US.
They share common goals to protect sensitive data, secure systems, and give individuals rights, but they have enough structural differences to create genuine compliance tension if not handled deliberately.
The Key Differences to Navigate
- Consent models: GDPR requires explicit consent for most processing activities. HIPAA permits treatment-related data processing without individual consent in many cases. For EU patients treated within US health platforms, this creates a conflict because GDPR's standard applies to EU residents regardless of the platform's home jurisdiction.
- Right to erasure vs. record retention: GDPR grants individuals the right to have their data deleted. HIPAA mandates a six-year medical record retention period. These obligations must be balanced, typically by segregating clinical records from marketing or operational data.
- Breach notification timelines: GDPR requires supervisory authority notification within 72 hours of discovering a breach. HIPAA allows up to 60 days. Where both apply, default to the stricter standard of 72 hours and ensure your team understands reporting obligations clearly, as outlined in this HIPAA violation report guide.
Dual Compliance Strategies
- Build one unified data inventory with GDPR and HIPAA flags mapped per data type, clinical records, billing data, patient communications, and analytics data, each of which carries different obligations.
- Create a combined security control framework that maps GDPR Article 32 requirements to the HIPAA Security Rule. The overlap is significant and reduces duplication of effort.
- Use a single vendor agreement template that covers both GDPR Data Processing Agreement obligations and the HIPAA Business Associate Agreement (BAA) requirements. Most enterprise vendors in healthcare can accommodate this.
- Default to the stricter standard on every conflicting requirement: 72-hour breach notification, explicit consent for non-treatment processing, full encryption mandated rather than 'addressable'.
- Run joint GDPR and HIPAA risk assessments. Compliance platforms like Scrut and Drata support cross-framework mapping and can flag gaps against both frameworks simultaneously.
The organizations that handle dual GDPR and HIPAA compliance most efficiently are those that build one integrated program, not two separate ones running in parallel. The shared controls are substantial; the framework differences are manageable with the right structure.
GDPR Compliance Strategies for SaaS Companies
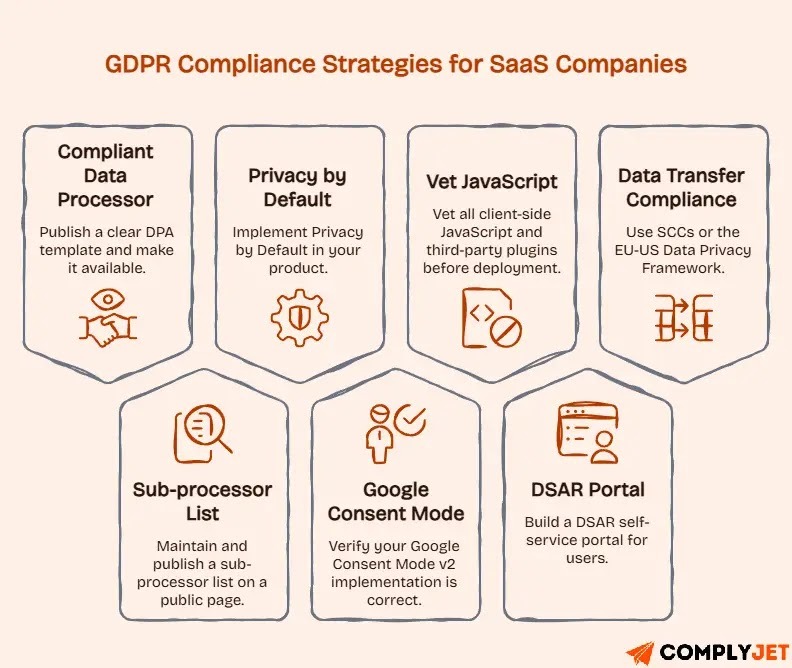
SaaS companies face a set of GDPR challenges that are distinct from those facing traditional enterprises. Multi-tenancy means one platform instance processes data on behalf of dozens or hundreds of clients. Rapid product iteration means new data flows appear in every release cycle.
Client-side JavaScript, third-party APIs, and embedded analytics create data exposure points that are easy to miss. And as an increasingly common enterprise buying requirement, GDPR compliance is also a sales asset.
The best GDPR compliance strategies for SaaS companies in 2026 address both the operational and the commercial dimensions:
- Act as a compliant data processor from day one. Publish a clear, well-drafted DPA template and make it available without a sales call. Enterprise buyers will not sign contracts without one, and having it ready signals maturity.
- Maintain and publish a sub-processor list on a public page listing every third-party tool you use to process customer data. Update it with 30 days' advance notice of changes, as required for processor DPAs.
- Implement Privacy by Default in your product: the most privacy-protective configuration must be the default out of the box. This applies to data retention settings, analytics enablement, and any profiling features.
- Verify that your Google Consent Mode v2 implementation is correct, especially if you use GA4, Google Ads, or any Google measurement stack. Non-compliant implementations are a 2026 enforcement priority.
- Vet all client-side JavaScript and third-party plugins before deployment. Unverified scripts that fire without consent, tag managers, heat mapping tools, and A/B testing platforms are consistently flagged in DPA technical audits.
- Build a DSAR self-service portal where users can request access to, export, or delete their data without having to contact your support team. This reduces operational overhead and demonstrates compliance with enterprise buyers.
- Use Standard Contractual Clauses (SCCs) or the EU-US Data Privacy Framework to cover personal data flows to US-based servers or sub-processors. Cross-border transfer compliance is a 2026 enforcement priority.
If done well, GDPR compliance becomes a commercial differentiator for SaaS companies. Publishing a Trust Center, a single page with your DPA, privacy policy, sub-processor list, security overview, and compliance certifications, is one of the most effective ways to accelerate enterprise sales cycles.
GDPR Compliance Checklist 2026
Use this as your working compliance checklist, tick off completed items, and use gaps to prioritize your next actions.
- Conduct a full data audit and build or update your Record of Processing Activities (ROPA).
- Document the lawful basis for every data processing activity before processing begins.
- Implement a GDPR-compliant Consent Management Platform (CMP) with granular consent and audit logs.
- Build a Data Subject Access Request (DSAR) intake and response workflow with SLA tracking.
- Sign Data Processing Agreements with all third-party vendors that process personal data.
- Apply technical security controls: AES-256 encryption, RBAC, MFA, pseudonymization, and regular pen testing.
- Embed Privacy by Design for all new features, products, and systems from the design stage.
- Develop and test a data breach response plan with 72-hour notification capability.
- Deploy an employee GDPR training program with role-specific modules and completion tracking.
- Set up continuous monitoring: consent log reviews, cookie banner testing, ROPA updates, vendor re-reviews.
- Leverage compliance automation tools for audit readiness and scale.
- (If applicable) Map overlapping controls for dual GDPR and HIPAA compliance in a single framework.
- (If SaaS) Publish your DPA template, sub-processor list, and Trust Center.
- (If marketing) Audit all email lists, cookie banners, and retargeting consent documentation.
Most teams find items 8 through 13 the hardest to maintain manually. See how our platform handles these automatically, so your team focuses on decisions, not data chasing.
GDPR Compliance Strategies Frequently Asked Questions
What are the most effective GDPR compliance strategies in 2026?
In 2026, top strategies blend structure and automation: conduct full data audits and maintain an accurate ROPA for visibility. Document lawful bases, implement a CMP, and manage vendor risks to close enforcement gaps. Prioritize consent management, dark pattern elimination, and cross-border transfers amid heightened regulatory focus. Continuous monitoring with automation ensures scalability.
What tools support GDPR compliance strategies?
Key tools include Complyjet, BigID, Privado.ai, and Varonis for data discovery and ROPA. OneTrust, Cookiebot, and TrustArc lead in consent management. DataGrail, Transcend, and Mine automate DSARs. Scrut, Sprinto, Drata, and Vanta handle audits and multi-framework compliance like SOC 2 and HIPAA, depending on your size and needs.
What is the meaning of GDPR compliance?
GDPR compliance means fulfilling EU Regulation 2016/679 obligations: collect data lawfully, secure it properly, respect individual rights, and document everything. You must prove compliance with authorities on request. It applies to any organization handling EU residents' personal data, regardless of location.
How do agencies ensure GDPR compliance in marketing strategies?
Agencies act as data processors, requiring DPAs with clients before processing. Audit email lists for consent, implement proper cookie banners, and avoid dark patterns. Use standardized templates for DPAs, consent checks, and vendor audits across clients. CNIL and ICO are ramping up audits in 2026.
What are the best strategies for GDPR compliance in SaaS companies?
SaaS firms should publish DPAs, sub-processor lists, and Trust Centers as compliant processors. Embed privacy by default in products and automate DSARs/consent at scale. Ensure cross-border transfers via SCCs or EU-US frameworks for US servers. Leverage compliance as a sales asset for enterprise buyers.
How do you achieve dual GDPR and HIPAA compliance?
Build a unified program: map data with dual flags and align security controls under Article 32 and HIPAA rules. Use combined DPA/BAA templates. Default to stricter rules on consent, retention, and breaches where they differ. Platforms like Scrut and Drata map overlaps for efficiency.
What is continuous GDPR compliance, and how does it work with big data?
Continuous compliance treats protection as ongoing: automate consent reviews, monitor cookies, update ROPAs quarterly, and re-review vendors. For big data, scan pipelines for new personal data, track lineage, and propagate consent withdrawals in real-time.
What happens if you fail to implement GDPR compliance strategies?
Non-compliance risks fines up to €20M or 4% of global turnover, plus orders, audits, and bans. It also brings lost contracts, reputational harm, and investigation disruptions. In 2026, intensified enforcement and automated scans make proactive gap-finding essential.
Final Thoughts
The 10 strategies covered in this guide form a complete, operational approach to GDPR compliance, one that holds up not just against the regulation's text, but against the enforcement reality of 2026. Data audits and data mapping give you visibility. Lawful basis documentation and consent management close the most common enforcement gaps.
Privacy by design, security controls, and staff training build resilience. DSR workflows and breach response plans ensure you meet your obligations when it counts. Vendor risk management closes the supply chain door. Continuous monitoring plus automation make the whole program sustainable at scale.
The organizations that treat GDPR compliance as a living program, not a one-time project, are the ones that pass regulatory scrutiny, win enterprise sales cycles, and avoid the enforcement outcomes that continue to make headlines.
In 2026, with AI-related processing risks, dark pattern crackdowns, and cross-border transfer enforcement all accelerating, the cost of a reactive approach keeps rising.
Ready to go further? Book a free GDPR compliance audit to get a gap assessment tailored to your organization, or explore compliance automation tools that can handle consent management, DSAR workflows, and audit evidence collection at scale.







