€7.1 billion. That is how much money organizations have been fined under the GDPR since its enforcement in 2018.
Many organizations still treat GDPR as Europe-only and ignore its extraterritorial scope and the need to understand GDPR requirements to manage real financial risks. In 2024 alone, Clearview AI, a US-based company with no EU establishment, faced over €100 million in penalties across multiple enforcement actions.
The impact of GDPR is no longer limited to European organizations; it extends to any business that processes the personal data of EU residents.
Though this shift is not purely restrictive, organizations that operationalize GDPR compliance strategies build trust, reduce regulatory risk, and strengthen their position in global markets.
However, to realize that advantage, organizations must understand and meet core GDPR compliance requirements as explained in this article.
At A Glance: The Essential GDPR Compliance Requirements
Here’s a quick overview of the 10 important compliance requirements every business should be aware of (click any of them to jump directly to a specific requirement):
- Establish a lawful basis for processing
- Follow 7 core GDPR principles
- Honor the 8 data subject rights
- Implement consent & cookie compliance
- Apply security measures
- Prepare for breach notifications
- Define data retention policies
- Ensure accountability & governance
- Manage international data transfers
- Conduct audits & ongoing compliance
Not sure where your business stands on these 10 GDPR requirements? Book a demo to kickstart your GDPR compliance workflow with ComplyJet!
Understanding how these requirements apply to your business is the next step. Because GDPR compliance is not just about knowing the rules. It is about knowing when they apply, why they apply, and how they affect your operations.
What is GDPR Compliance and Who Must Comply?
Let's start with a common question first, what is GDPR?
GDPR stands for General Data Protection Regulation. GDPR is the European Union's flagship data privacy law to protect EU region users' data.
GDPR governs how companies collect, use, and store the EU residents' personal data. This regulation replaced the 1995 data protection directives from May 25, 2018, onwards.
Who needs to follow GDPR compliance requirements?
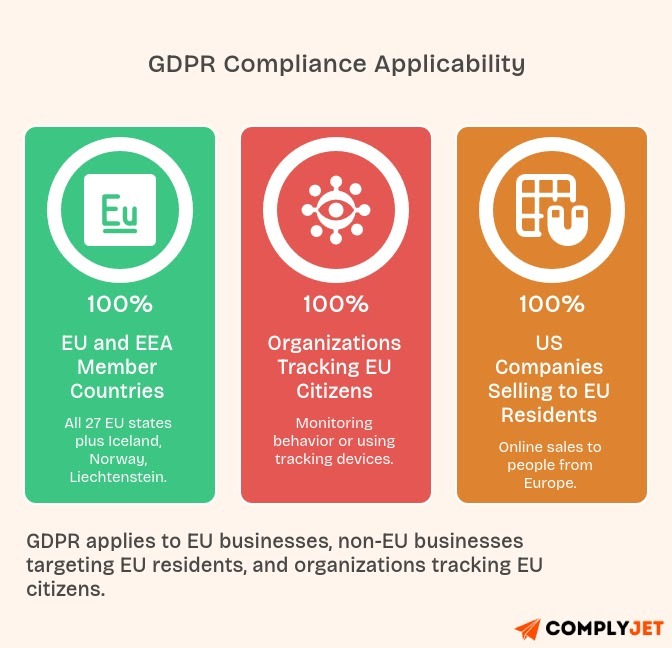
In addition, any business entity registered in one of the EU and EEA member countries has to adhere to GDPR compliance requirements. The countries mentioned include all 27 EU member states plus Iceland, Norway, and Liechtenstein.
The second scenario covers organizations located outside the EU that offer goods and services to EU nationals. Here, US companies may find themselves unaware of this condition. Selling goods online to people from Europe? Your company is subject to GDPR.
And finally, any organization that tracks the activities of EU citizens. Placing any tracking devices or monitoring the behavior of visitors coming from the EU? Then your website is subject to GDPR.
GDPR mentions the following important positions that should be familiar to all:
- Data Controller: The entity that decides why and how personal data gets processed
- Data Processor: The entity that processes data on behalf of the controller
- Data Subject: The individual whose personal data is being processed
- DPA: Data Protection Authority, the government agency that enforces GDPR
National Data Protection Authorities handle enforcement in each country. The European Data Protection Board coordinates its efforts across the EU.
Penalties come in two tiers. Tier 1 violations can result in fines up to €20 million or 4% of global annual turnover, whichever is higher. Tier 2 violations max out at €10 million or 2% of turnover.
Does GDPR apply to my US company?
For basic understanding, answer these three questions:
- Do you have website visitors from the EU?
- Do you sell products or services to EU residents?
- Do you use cookies or analytics that track EU visitors?
If you answered "yes" to any question, GDPR likely applies to your business.
Now, if GDPR applies, the next step is understanding what compliance actually requires in practice. These requirements are not arbitrary. They are grounded in the regulation’s core principles and legal framework.
Let’s start with the first and most fundamental requirement.
Requirement 1: Establish a Lawful Basis for Processing
Before processing any personal data, you must identify a lawful basis under Article 6. This isn't optional. Choose one of six legal grounds before you start collecting information.
The 6 Legal Grounds Under Article 6 of GDPR
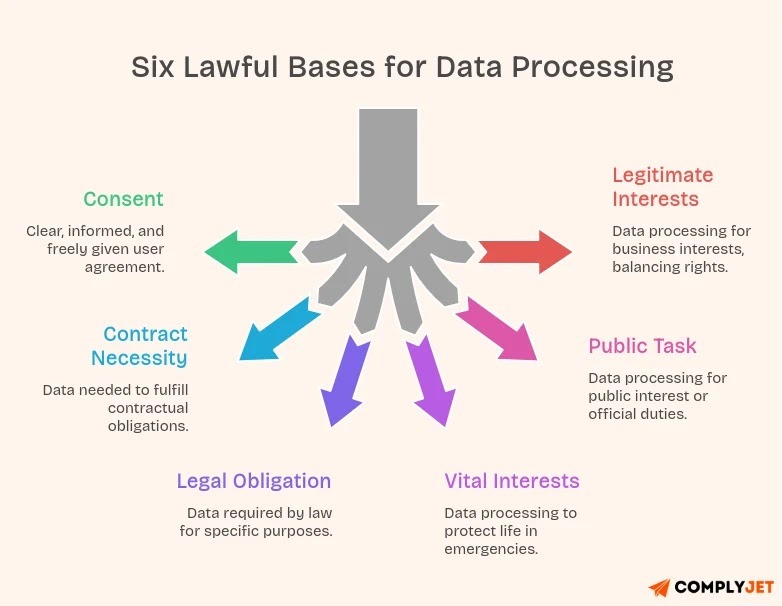
1. Consent (Article 7)
Firstly, if you’re relying on consent, it has to be crystal clear. It is a must that the user should know exactly what they’re agreeing to. As per EU GDPR, there should be no pre-checked boxes. No hiding it in fine print.
2. Contract Necessity
Sometimes, data is needed just to make things work. If someone buys from you, you need their details to complete the order. That’s simply part of the deal.
3. Legal Obligation
There are times when you don’t have a choice. Laws may require you to store or process certain information, like financial records for tax purposes.
4. Vital Interests
This one’s about protecting lives. It’s mainly used in emergencies, not everyday business situations.
5. Public Task
If the processing is tied to public interest or official responsibilities, it falls under this category. Typically, this applies to government or public bodies.
6. Legitimate Interests
Processing is necessary for your legitimate interests or those of a third party, unless those interests are overridden by the individual's rights. You must conduct a Legitimate Interests Assessment (LIA) to use this basis.
Special Category Data (Article 9)
Special category data gets extra protection under Article 9. This includes health information, biometric data, genetic data, racial or ethnic origin, political opinions, religious beliefs, and sexual orientation. Processing this data requires explicit consent in most cases.
A critical practice: Document Your Lawful Basis in Your ROPA
Document your lawful basis in your Record of Processing Activities (ROPA). Don't just pick one; write it down with justification.
A common mistake companies make is relying on "legitimate interests" without conducting a proper Legitimate Interests Assessment (LIA assessment). Data protection authorities scrutinize this basis closely. If you choose it, document your assessment thoroughly.
Organizations managing multiple processing activities often benefit from using the best GDPR compliance software to centralize documentation and automate compliance workflows.
Requirement 2: Follow The 7 Core GDPR Principles
Article 5 of GDPR establishes seven fundamental principles. Every GDPR compliance requirement flows from these core concepts. Think of them as the foundation of the entire regulation.
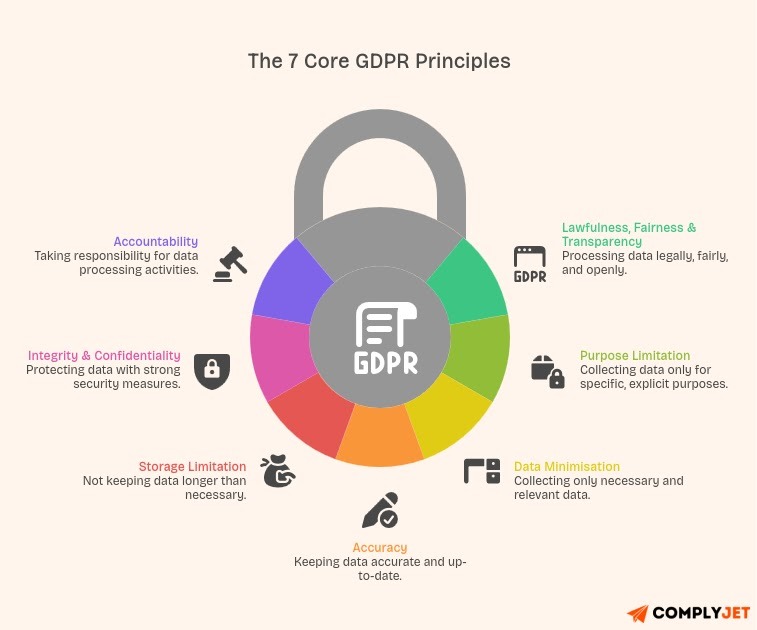
1. Lawfulness, Fairness & Transparency
You must process data legally, fairly, and in a transparent manner. This means being upfront with people about what data you collect and why. No hidden tracking or secret databases.
2. Purpose Limitation
Collect personal data for specific, explicit, and legitimate purposes only. You can't gather email addresses for newsletter signups, then suddenly use them for targeted advertising without new consent.
3. Data Minimisation
Only collect data that's adequate, relevant, and necessary for your stated purpose. If you're processing newsletter subscriptions, you don't need birth dates or phone numbers.
4. Accuracy
Keep personal data accurate and up to date. Provide ways for people to correct inaccurate information. Delete or update outdated records promptly.
5. Storage Limitation
Don't keep personal data longer than necessary. Once data serves its purpose, delete it or anonymize it. This principle directly connects to data retention requirements we'll cover later.
6. Integrity & Confidentiality (Security)
Protect personal data with appropriate security measures. This includes encryption, access controls, and safeguards against unauthorized processing or accidental loss.
7. Accountability
Shouldering accountability is essential. Record-keeping is important, and you will have to show proof of your adherence to the guidelines at all times.
This can be explained with an example: Fitness apps collect data on the health of users. According to the above criteria, the reason for needing health data must be made clear (transparency), the data must only be used for tracking fitness (purpose limitation), secured with encryption (security), and stored only until account deletion (storage limitation).
These 7 principles form the backbone of every GDPR compliance requirement at large.
Requirement 3: Data Subject Rights (The 8 Rights You Must Honor)
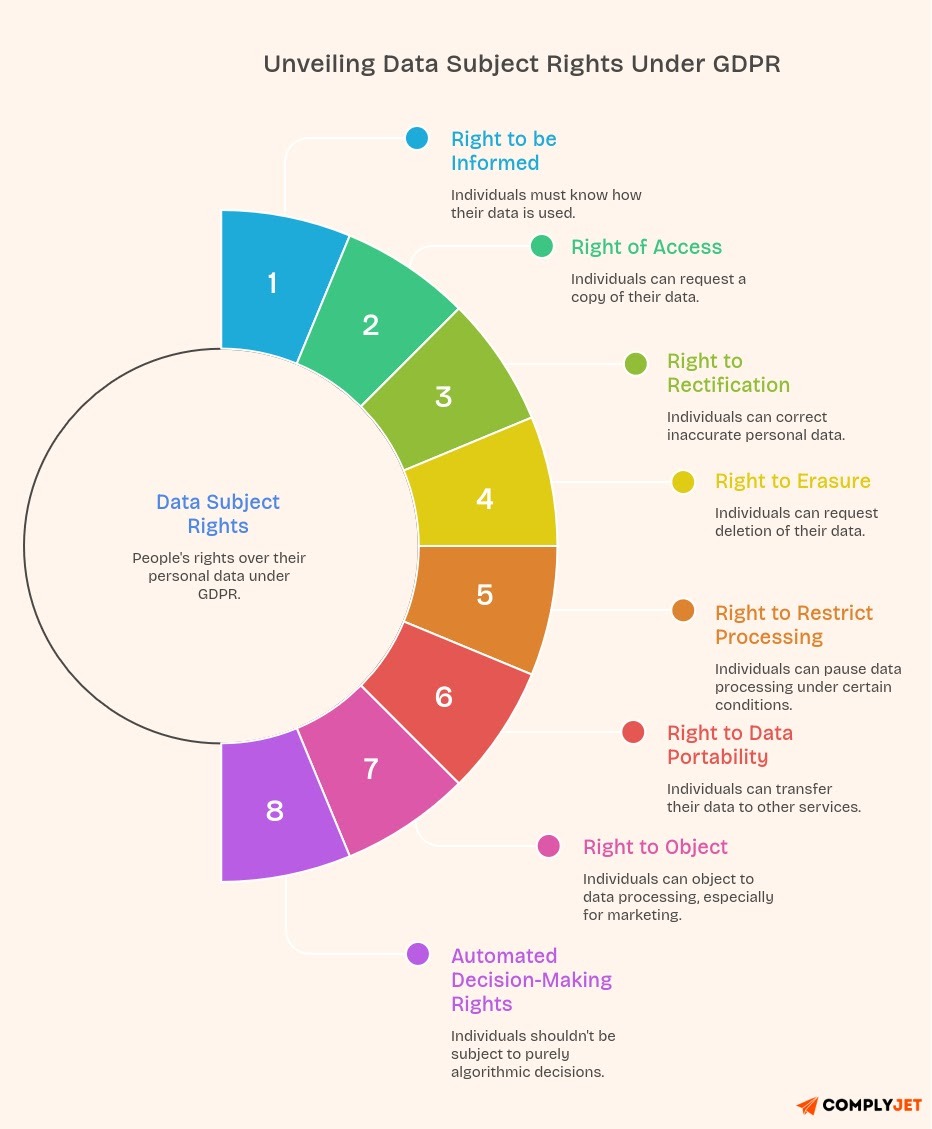
The GDPR Regulations give people real control over their data. Eight rights, to be exact. And these aren’t just guidelines. They’re enforceable, with clear deadlines for businesses to respond.
1. Right to be Informed
People should know what you’re doing with their data. That means clear, simple explanations, not pages of legal text nobody understands.
2. Right of Access
Anyone can ask, “What data do you have on me?” You’ll need to provide a copy, usually for free, and in a format they can actually use.
3. Right to Rectification
If something’s wrong, they can ask you to fix it. And if others have that data, you’re expected to update them too.
4. Right to Erasure
In certain cases, people can ask you to delete their data altogether, especially if there’s no valid reason to keep it.
5. Right to Restrict Processing
Sometimes, it’s not about deleting data but pausing its use, like when accuracy is being questioned.
6. Right to Data Portability
Users can take their data elsewhere. You need to provide it in a format that makes that possible.
7. Right to Object
If someone doesn’t agree with how their data is being used, especially for marketing, they can object. And you may have to stop. A well-known example is Google Spain v AEPD and Mario Costeja González case.
8. Automated Decision-Making Rights
People shouldn’t be subject to major decisions made purely by algorithms without human involvement.
GDPR Request Time Limit
Organizations must respond to these requests within 30 days. You can extend this by another two months for complex requests, but you must inform the individual within the first month.
How to Handle Subject Access Requests (SARs)?
Build a dedicated request portal or intake form on your website. Train staff to recognize requests arriving via email, phone, or social media. Verify the requester's identity before disclosing personal data. Search all systems where data might exist. Compile the data in a clear, accessible format. Respond within the 30-day deadline.
Missing deadlines or ignoring requests can trigger complaints to data protection authorities. Similar to how healthcare organizations must respond to patient data requests under the HIPAA compliance checklist, GDPR mandates strict timelines for data subject requests.
Requirement 4: Implement Consent & Cookie Compliance
Under Article 7 of the GDPR, consent must meet strict criteria. It’s not as simple as clicking a button. Misunderstanding this is where many businesses go wrong.
What qualifies as valid consent?
Consent must be freely given. Users shouldn’t feel forced into accepting non-essential processing just to access your service.
It must be specific. Broad, all-in-one consent doesn’t meet GDPR standards. Each purpose, such as analytics, marketing, and personalization, requires separate approval.
Consent must be informed. Users need a clear explanation upfront, written in plain language.
It must be unambiguous. This means an active step. No pre-selected options or implied agreement shall be shown to users.
And it must be easy to withdraw. If opting out is difficult or hidden, the consent isn’t valid.
Cookie consent Requirements under GDPR
Non-essential cookies require prior opt-in consent. Essential cookies, which enable core functionality, are exempted.
Cookie banner best practices
- Provide equal prominence to both “accept” and “reject” options.
- Avoid repeatedly prompting users who have already declined. Best practice suggests a pause of several months.
- Allow granular control over cookie categories.
- Ensure scripts like analytics only load after consent is given, not before.
Email marketing compliance
- Double opt-in is strongly recommended to verify consent.
- Maintain detailed logs of when and how consent was obtained.
- Include an unsubscribe link in every email and process requests without delay.
2026 Consent Update to Note
If you rely on Google Analytics or Google Ads, implementing Google Consent Mode v2 is now essential for compliance.
Furthermore, consent management should be reviewed regularly.
Requirement 5: Apply Appropriate Security Measures
If you read Article 32 of the GDPR closely, you’ll notice it doesn’t give you a checklist. It says “appropriate measures,” which basically means, “you’re expected to think.”
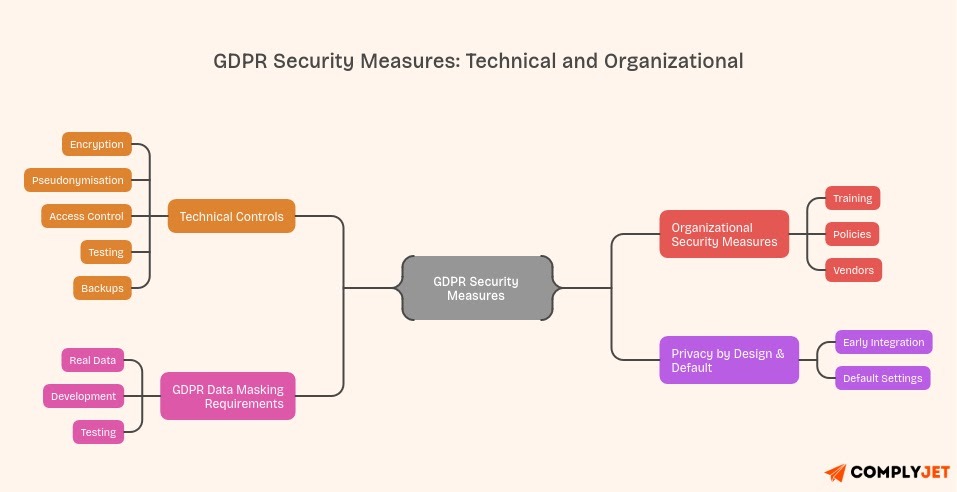
Technical controls (what actually matters?)
Encryption should already be in place. Not “planned,” not “in progress.” It should cover both data at rest and data in transit.
Pseudonymisation is useful, especially when teams don’t need full identity data. It’s not perfect, but it reduces exposure.
Access control sounds simple, but most companies overdo permissions. Too many admins, too many shared accounts. Implementing robust authentication measures similar to those required in an ISO 27001 password policy helps enforce least privilege consistently.
Testing is where shortcuts happen. Pen tests get delayed. Scan reports sit untouched. That’s usually where issues start piling up.
Every company keeps backups, but hardly verifies whether those backups can be successfully restored when needed.
Organizational Security Measures
Training shouldn’t feel like compliance theater. If employees don’t understand real scenarios (phishing, data leaks), the training didn’t work.
Policies? Keep them usable. If they’re too complex, nobody follows them.
Vendors can quietly introduce risk. If they’re handling your data, you need visibility—not just a signed agreement.
GDPR Data Masking Requirements
Still worth repeating: don’t use real data in dev or testing unless you absolutely have to. And most of the time, you don’t.
Privacy by Design & Default
Adding privacy later is always messy. Build it early, even if it slows things down a bit.
Default settings matter more than people think. Most users don’t change them—so choose wisely.
At the end of the day, GDPR security isn’t about passing an audit. It’s about not ending up in a breach headline.
Security gaps don't announce themselves until it's too late. Get your free security posture assessment and see exactly where your GDPR vulnerabilities lie. Takes 15 minutes, could save millions.
Requirement 6: Prepare for Breach Notifications
Data breaches happen even to security-conscious organizations. GDPR doesn't expect perfection. It demands transparency and rapid response when things go wrong.
Notify the Authority Within 72 Hours (Article 33)
When a personal data breach occurs, you must notify the relevant Data Protection Authority within 72 hours of becoming aware of it. "Becoming aware" means when you have reasonable certainty that a breach has occurred.
There's a discussion about extending this to 96 hours in 2026, but 72 hours remains the current requirement. Don't wait for complete information. Notify within the deadline with what you know.
Notify Individuals if High Risk (Article 34)
If the breach likely results in a high risk to people's rights and freedoms, notify affected individuals without undue delay. High risk means potential identity theft, financial loss, discrimination, or reputational damage.
What Your Breach Notification Must Include?
Describe the nature of the breach. Explain what happened, what data was affected, and approximately how many people are impacted.
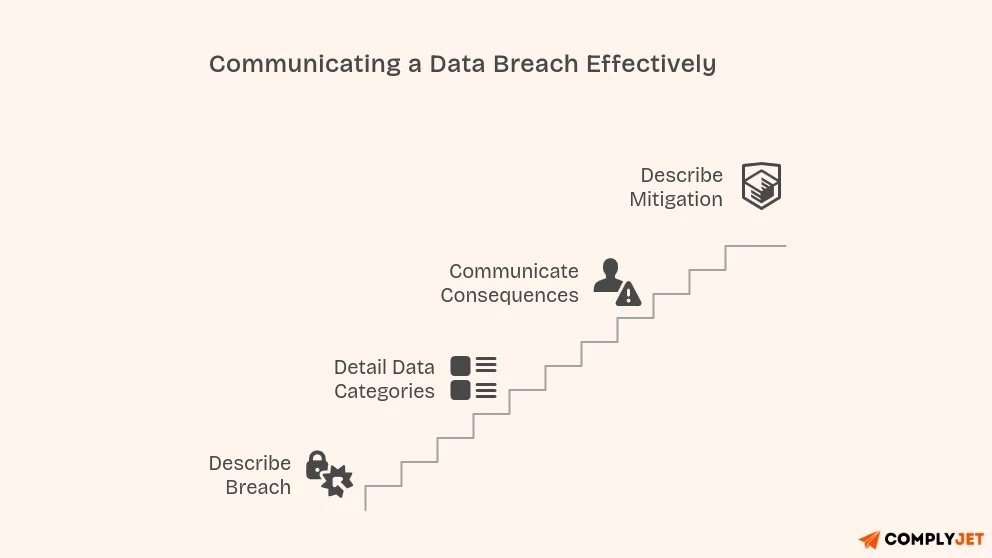
Breach notification shall include:
- Detail the data categories affected. Was it names and email addresses? Financial information? Health records? Be specific about what was compromised.
- Communicate the likely consequences. Help people understand the potential impact. Will they receive phishing emails? Could accounts be compromised?
- Describe mitigation measures. Explain what you've done to contain the breach and reduce harm. Are you offering credit monitoring? Resetting passwords? Enhancing security?
(Important) Prepare an Internal Breach Response Plan
Don't wait until a breach happens to figure out your response. Create a written incident response plan now. Assign roles and responsibilities. Identify who makes the call to notify authorities.
Practice your response with tabletop exercises. Simulating a breach reveals gaps in your plan before they matter in a real emergency.
Healthy Practice: Encryption Reduces Notification Obligations
Here's an important exception: If the breached data was encrypted with strong encryption and the keys weren't compromised, you might not need to notify individuals. The data remains unreadable to unauthorized parties.
This creates a strong incentive to encrypt personal data. It's both a security measure and a breach response strategy.
Document every breach, even if notification isn't required. Keep records of the facts, effects, and remedial actions. Data protection authorities may request these records during audits.
Requirement 7: Define Data Retention Policies
Article 5(1)(e) states that personal data shouldn't be kept longer than necessary. This principle sounds simple, but implementation gets complex quickly.
No Universal Retention Period
GDPR doesn't specify how long you can keep data. Retention periods depend on your purpose for processing and any legal obligations you face.
Common Retention Period Examples
HR and employment records typically require 5-7 years of retention. Employment laws often mandate keeping payroll records, tax documents, and personnel files for this duration.
Customer data should be kept for the duration of the business relationship. After a customer closes their account, you might need certain data for warranty claims, returns, or legal requirements. Define clear retention periods in your policy.
Marketing data can be kept until consent is withdrawn. Once someone unsubscribes from marketing communications, delete their data unless you have another lawful basis for retention.
Financial records usually require approximately 7 years of retention. Tax authorities and financial regulations commonly mandate this period for invoices, receipts, and transaction records.
Create a Data Retention Policy
Document retention periods for each data category you process. Explain the legal or business justification for each period. Make this policy available to data subjects in your privacy notice.
Your policy should specify what happens when retention periods expire. Will data be deleted permanently? Anonymized? Archived in a restricted system?
Secure Deletion and Anonymization
When retention periods end, ensure secure deletion. Overwriting files or using certified data destruction services prevents data recovery. Simply hitting "delete" often isn't enough.
Anonymization offers an alternative to deletion. Strip all identifying information from data so it no longer relates to an identifiable person. Truly anonymized data falls outside the GDPR scope.
Automated Retention Schedules
Manual data deletion doesn't scale. Implement automated systems that flag or delete data when retention periods expire. Regular audits verify that the automation works correctly. Much like conducting an ISO 27001 internal audit, GDPR security assessments should follow a structured methodology to identify and address vulnerabilities.
Many organizations discover data they should have deleted years ago during GDPR audits. Don't let obsolete data create compliance risks. Address retention proactively.
Requirement 8: Ensure Accountability & Governance
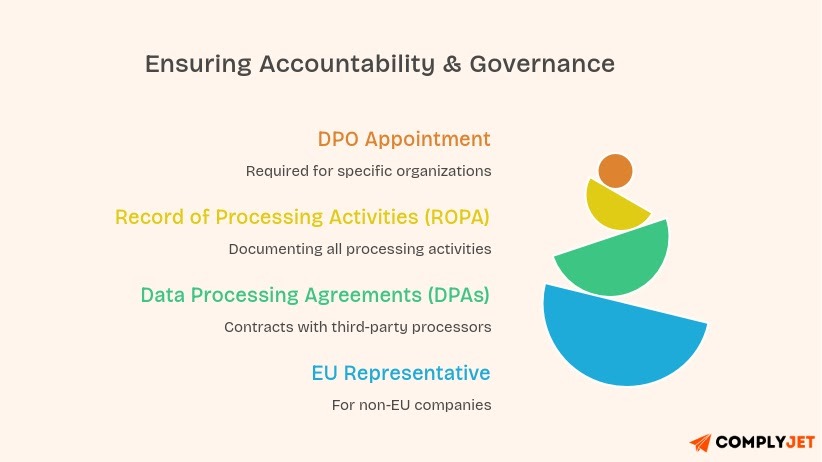
Article 37 of GDPR requires certain organizations to appoint a Data Protection Officer. This role serves as the internal expert and point of contact with data protection authorities.
But when is a DPO appointment required?
You must appoint a DPO if you're a public authority or body. This includes government agencies and public institutions.
You need a DPO if your core activities involve regular and systematic monitoring of individuals on a large scale. Think behavioral advertising platforms or large-scale surveillance systems.
You must have a DPO if your core activities involve large-scale processing of special category data or criminal conviction data. Healthcare providers and background check companies typically need DPOs.
DPO Responsibilities:
The DPO monitors GDPR compliance across the organization. They advise on data protection impact assessments, train staff, and serve as the contact point for data protection authorities.
DPOs must report directly to the highest management level. They need independence-no conflicts of interest with other roles. Don't make your IT director or marketing head your DPO if they make decisions about data processing.
Record of Processing Activities (ROPA)
Article 30 requires maintaining an ROPA unless you're a small organization with fewer than 250 employees processing data only occasionally. Most businesses need an ROPA.
Your ROPA documents all processing activities. It includes what data you collect, why you process it, who you share it with, retention periods, and security measures. Organizations pursuing multiple certifications often align their ROPA documentation with SOC 2 compliance requirements to streamline their overall compliance posture, including the GDPR regulations angle.
Think of the ROPA as your processing inventory. Data protection authorities often request this document first during audits.
Data Processing Agreements (DPAs)
When you use third-party processors, cloud providers, payment processors and email services, you need Data Processing Agreements with them. These contracts specify processor obligations, security requirements, and data subject rights procedures.
Standard GDPR clauses should appear in every DPA. Many vendors offer pre-approved agreements, but review them carefully before signing.
EU Representative for Non-EU Companies
If you're outside the EU but GDPR applies to you, Article 27 may require appointing an EU representative. This person or company serves as your point of contact for data protection authorities and data subjects.
Not everyone needs an EU representative. Small-scale processing unlikely to risk people's rights might be exempt. But most US companies with significant EU customer bases should appoint one.
The representative must be established in one of the EU member states where your data subjects are located. This creates a local point of contact for enforcement.
Accountability isn't about having the right documents. It's about demonstrating ongoing commitment to data protection through concrete actions, regular reviews, and continuous improvement.
Requirement 9: Manage International Data Transfers (Crucial for US companies)
This is where many companies often get confused. Many American businesses assume GDPR doesn't apply to them. That's a costly misconception. GDPR applies extraterritorially. Its reach extends far beyond European borders.
GDPR Applies Based on Data Subject Location, Not Company Location
You don't need an office in Brussels to fall under GDPR. Processing personal data of people located in the EU triggers the regulation. This includes website visitors, newsletter subscribers, and customers.
No Size or Revenue Threshold
Unlike some US privacy laws with employee or revenue thresholds, GDPR doesn't exempt small businesses. A three-person startup faces the same GDPR compliance requirements as a Fortune 500 company.
The regulation does provide some relief for smaller organizations. Those with fewer than 250 employees don't always need a full ROPA, and certain documentation requirements may be reduced. But core requirements still apply.
Additional GDPR Requirements for US Companies
US businesses often need an EU representative under Article 27. This creates a European point of contact for authorities and data subjects.
International data transfers require special safeguards. Moving personal data from the EU to the US needs legal mechanisms like Standard Contractual Clauses (SCCs), Binding Corporate Rules (BCRs), or adherence to the EU-US Data Privacy Framework.
The Data Privacy Framework replaced Privacy Shield in 2023. US companies can self-certify to transfer data legally. But certification requires meeting specific requirements and annual recertification.
GDPR vs US Privacy Laws
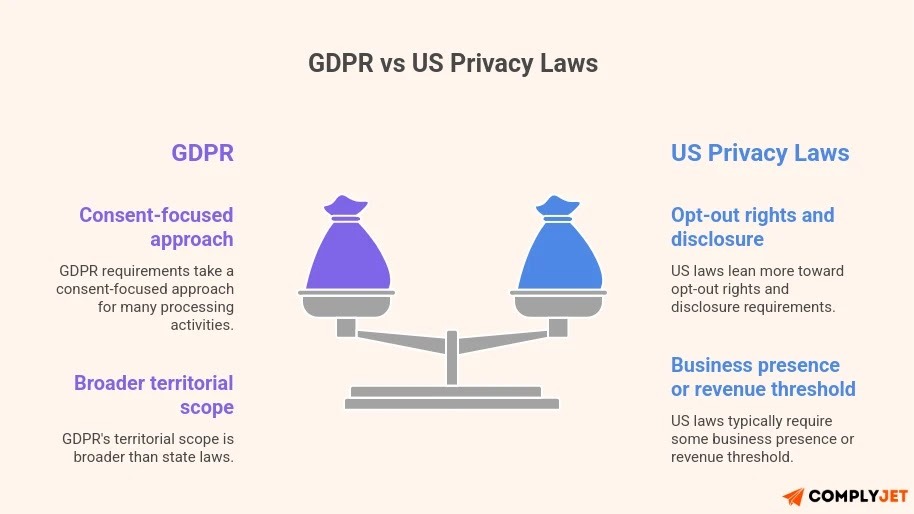
The compliance landscape for US companies gets complicated. GDPR requirements differ from California's CPRA, Virginia's VCDPA, and Colorado's CPA.
GDPR takes a consent-focused approach for many processing activities. US laws lean more toward opt-out rights and disclosure requirements.
GDPR's territorial scope is broader than state laws. US laws typically require some business presence or revenue threshold. GDPR applies based purely on data subject location.
Popular GDPR Violation Cases Affecting US Companies
Google received a €50 million fine in 2019 from France's data protection authority for a lack of transparency and invalid consent. Meta faced €1.2 billion in fines in 2023 related to EU-US data transfers.
Here are a few other cases, as per violation type, to have a look at:
*Note: Actual fine amounts consider violation severity, duration, intentionality, cooperation, and mitigation efforts.
These aren't just European companies. American tech giants pay the largest GDPR penalties because they process massive amounts of EU user data.
So What Shall Businesses Do? Here’s Practical Steps for US Companies
Start with a data audit. Then,
- Identify what EU personal data you process and where it's stored. This reveals your actual exposure.
- Review your privacy policy. Ensure it meets GDPR transparency requirements, not just US standards. Make it accessible and written in clear language.
- Implement a cookie consent management platform if you haven't already. US-style privacy policies don't satisfy GDPR cookie consent requirements.
- Create processes for handling data subject requests. EU residents will exercise their rights. Having systems ready prevents scrambling when requests arrive.
Many US companies take a "privacy by design" approach, with built-in GDPR-level protections for all users. This simplifies compliance and often improves overall data security.
Is Built-In GDPR Compliance Approach Fit for Your Business? Get a clear solution in our Free Demo!
Requirement 10: Conduct Audits & Ongoing Compliance (Follow-Along Checklist)
To operationalize the requirements covered so far, use the following checklist as a working framework. Approach it systematically. Each step builds on the previous ones and helps you maintain long-term compliance.

□ Conduct a Data Audit
Map all personal data you collect, process, and store. Identify data sources, processing purposes, storage locations, and third-party sharing. Document everything in a data inventory.
□ Document Lawful Basis for Each Processing Activity
Identify and record your lawful basis for every processing operation. Update your ROPA with this information. Review bases annually as processing changes.
□ Update Privacy Notices
Ensure privacy policies meet GDPR transparency requirements. Include all Article 13/14 information. Write in clear, accessible language. Make notices easy to find.
□ Implement Cookie Consent Management
Deploy a GDPR-compliant cookie consent platform. Obtain opt-in consent before non-essential cookies fire. Provide granular consent options and easy withdrawal.
□ Build a Data Subject Access Request Workflow
Create procedures for handling the eight data subject rights. Set up request intake mechanisms. Train staff to recognize and process requests. Meet 30-day deadlines consistently.
□ Implement Appropriate Security Measures
Deploy encryption for data at rest and in transit. Establish access controls and authentication systems. Conduct regular vulnerability assessments and penetration testing.
□ Establish Breach Response Procedures
Develop a written incident response plan. Define roles and notification procedures. Practice with tabletop exercises. Ensure you can meet 72-hour notification requirements.
□ Create and Enforce Data Retention Policy
Define retention periods for each data category. Implement automated deletion or anonymization schedules. Conduct regular data purges for expired information.
□ Execute Data Processing Agreements
Review and sign DPAs with all processors. Ensure contracts include required GDPR clauses. Audit key vendors for compliance. Maintain current copies of all agreements.
□ Appoint DPO or EU Representative if Required
Determine whether you need a Data Protection Officer. Appoint an EU representative if you're a non-EU company processing EU data at scale.
□ Conduct Data Protection Impact Assessments
Identify high-risk processing activities. Complete DPIAs before starting such processing. Document risks and mitigation measures. Review DPIAs when processing changes.
□ Train Staff on GDPR Requirements
Provide comprehensive GDPR training to all employees handling personal data. Conduct annual refresher courses. Create role-specific training for different departments.
Compliance isn't a one-time project. Plan quarterly reviews of your GDPR program. Update procedures as regulations evolve and your business changes.
Ready to move from checklist to implementation? Start your guided GDPR setup with ComplyJet. Our platform walks you through every requirement with automated evidence collection and real-time compliance tracking.
(Quick Scan) Summary of 10 Core GDPR Compliance Requirements
Frequently Asked Questions
Q1. What are the GDPR compliance requirements?
Ans. GDPR compliance requirements include establishing a lawful basis for data processing, honoring eight data subject rights, implementing appropriate security measures, obtaining valid consent for cookies and marketing, notifying breaches within 72 hours, maintaining data retention policies, and appointing a DPO when necessary.
Q2. Does GDPR apply to US companies?
Ans. Yes, GDPR applies to US companies that process personal data of EU residents. You don't need a physical presence in Europe. If your website attracts EU visitors, you sell to European customers, or you monitor EU resident behavior through cookies or analytics, GDPR likely covers your operations.
Q3. What is the GDPR request time limit?
Ans. Organizations must respond to data subject requests within 30 days of receipt. You can extend this period by an additional two months for complex requests, but you must inform the requester of the extension and the reasons within the initial 30-day period.
Q4. What are the technical requirements of GDPR?
Ans. GDPR technical requirements under Article 32 include implementing encryption for data at rest and in transit, using pseudonymisation techniques, establishing strong access controls and authentication, conducting regular vulnerability testing and penetration testing, maintaining secure backups, and ensuring disaster recovery capabilities.
Q5. What are GDPR cookie consent requirements?
Ans. GDPR requires opt-in consent before placing non-essential cookies on users' devices. Consent must be freely given, specific, informed, and unambiguous. Users need a clear reject option as prominent as the accept button. Pre-ticked boxes don't constitute valid consent. Essential cookies for basic site functionality don't require consent.
Q6. What happens if you violate GDPR?
Ans. GDPR violations can result in administrative fines up to €20 million or 4% of global annual turnover, whichever is higher. Individuals can also pursue compensation for damages through civil lawsuits.
Q7. What data does GDPR protect?
Ans. GDPR protects all personal data, any information relating to an identified or identifiable natural person. This includes names, email addresses, IP addresses, location data, cookie identifiers, and online identifiers. Special categories receive extra protection: health data, biometric data, genetic data, racial or ethnic origin, political opinions, religious beliefs, and sexual orientation.
Q8. How do I know if I need a DPO?
Ans. You need a Data Protection Officer if you're a public authority. Your core activities involve regular and systematic large-scale monitoring of individuals, or your core activities involve large-scale processing of special category data or criminal conviction data.
Conclusion
GDPR compliance isn't built in a day, but every organization processing EU data must start somewhere. The GDPR compliance requirements are extensive, but they follow a logical pattern: know your data, protect it appropriately, respect individual rights, and demonstrate accountability.
The real challenge isn't understanding what GDPR requires but operationalizing these requirements consistently across your organization. Start with a thorough data audit. Document your current state honestly. Then tackle requirements systematically, prioritizing based on your risk profile.
Compliance is a journey, and you don't have to walk it alone. With ComplyJet, we automate and coordinate every audit end-to-end on one platform with total accountability.







