What if you're a sales rep. You just had a great call with a Fortune 500 buyer. Things are moving fast. Then the buyer sends over a spreadsheet with 800 questions about your security practices. The deal goes quiet for three months.
That spreadsheet is a security questionnaire.
For most B2B companies, it is one of the most reliable deal blockers between a signed contract and a lost one. The good news is that it does not have to be.
This guide covers everything.
What a security questionnaire is. The main types and standardised frameworks. What a good security questionnaire template looks like. How to answer one well. And how to automate the whole process.
Whether you send questionnaires or receive them, this is the guide you keep open.
Security questionnaires are not a compliance burden. They are a trust signal. The teams who treat them that way close more deals and build better buyer relationships.
See how ComplyJet helps teams respond to security questionnaires in hours.
Now, let's get into the basics.
What Is a Security Questionnaire?
A security questionnaire is a structured list of questions. One organisation sends it to another.
The goal is to understand how the other party handles data security, privacy, and compliance. It almost always surfaces before two companies begin working together.
Think of it as due diligence with a checklist. The buyer needs proof that your systems and practices are solid before sharing data or system access.
The vendor needs to show that they take security seriously. Both sides have real skin in the game.
The Buyer and the Vendor
There are two sides to every security questionnaire.
The buyer side sends the questionnaire. They use it to evaluate third-party vendors and protect their vendor ecosystem from risk. The vendor side receives it and must respond with clear, documented evidence.
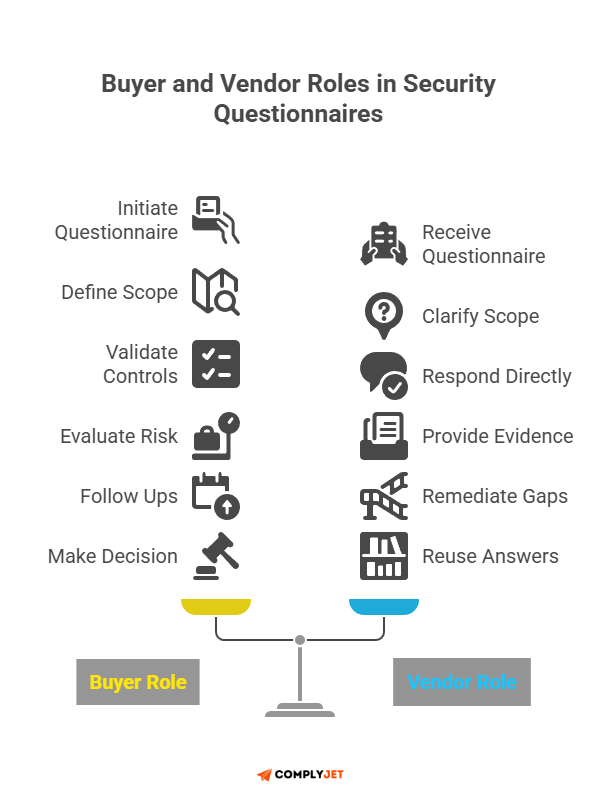
If you are a SaaS company or software vendor, you will spend most of your time on the vendor side.
Your buyer wants proof that you protect their customer data. A strong response builds trust fast. A slow or vague one kills deals before they even reach legal review.
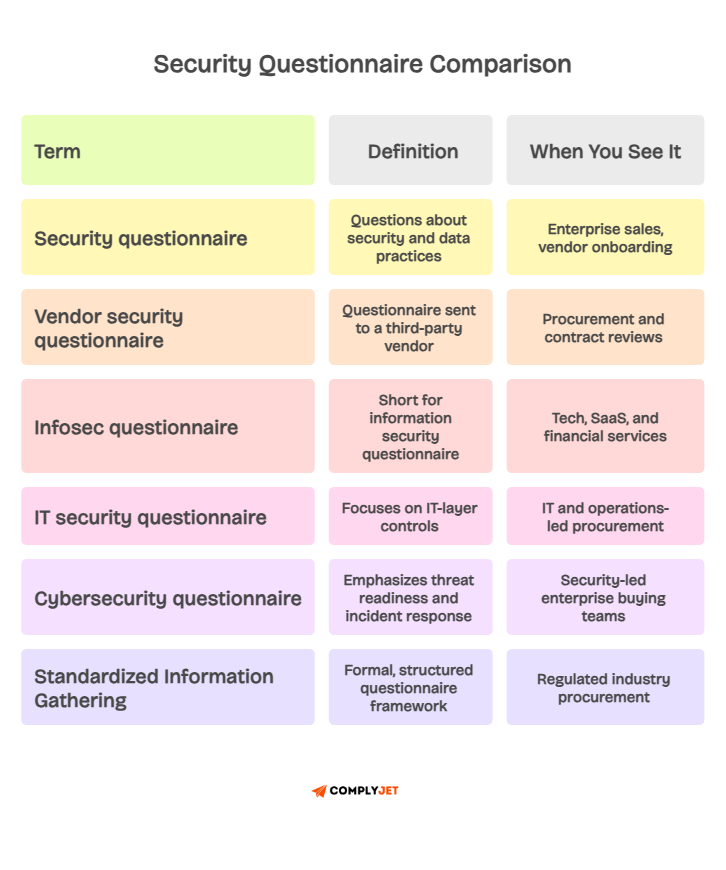
You will also hear this called an InfoSec questionnaire, an IT security questionnaire, or a cyber security questionnaire.
The label shifts by industry and team. The core purpose stays the same across all of them. Evaluate security practices. Document the findings. Reduce third-party risk before it becomes a breach.
Standardized Information Gathering
Most buyers used to build their own questionnaires. That created chaos. Every vendor got a different set of questions with no consistency.
Standardized Information Gathering was created to fix exactly that problem.
Standardized information gathering gives buyers and vendors a shared format.
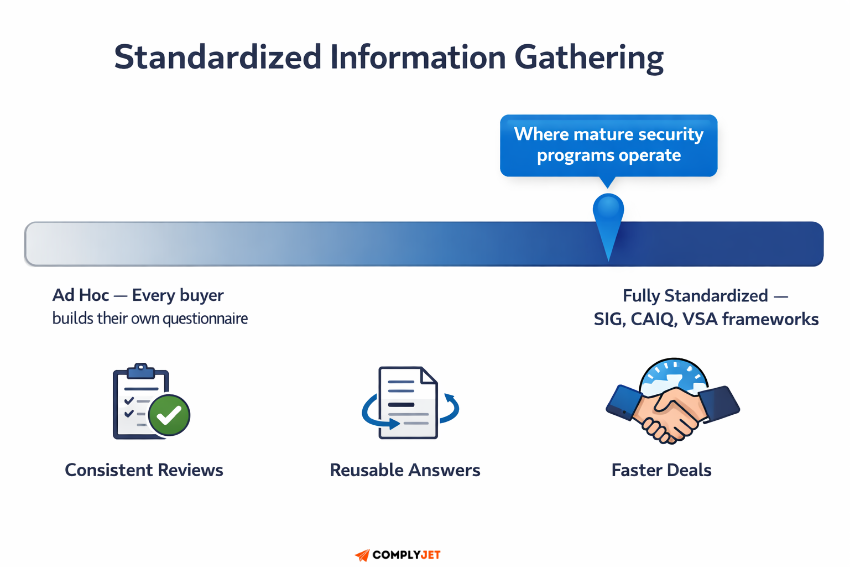
Everyone works within the exact domains and question types. That makes security assessments faster to complete and easier to compare across an entire vendor ecosystem.
Founders' Tip: If you receive a lot of security questionnaires from enterprise buyers, start tracking which questions repeat. You will find that roughly 80 percent of questions appear across multiple buyers. Build your answer library around those first. You will cut your response time dramatically.
Security questionnaires carry legal weight, too. Before a third-party vendor gets access to customer data or internal systems, organizations need documented proof that the vendor has fundamental protections in place.
The questionnaire is that proof. Without it, you have no record of due diligence.
Now you know what a security questionnaire is. Here is why getting them right matters far more than most teams realize.
Why Security Questionnaires Matter?
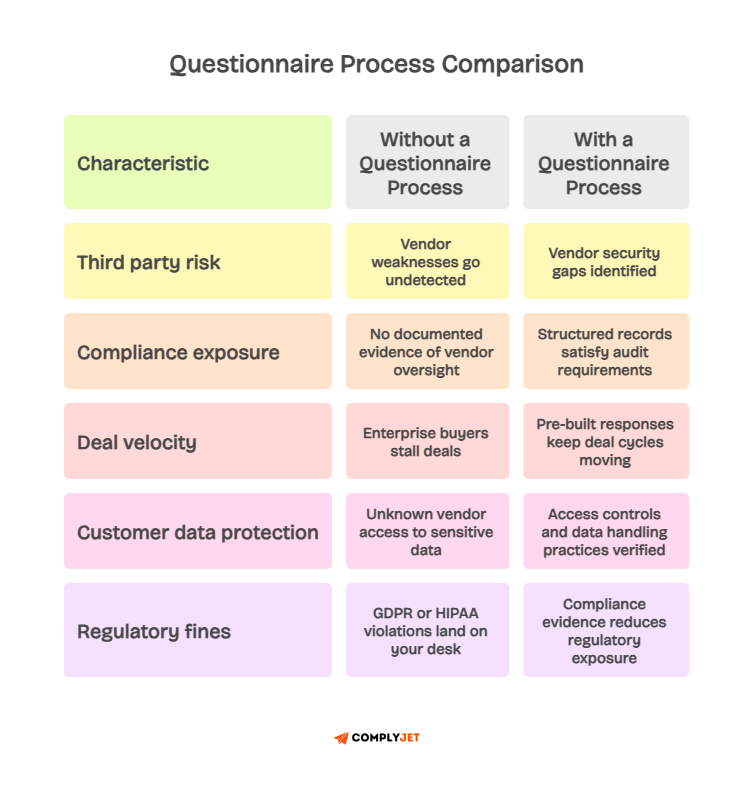
Most teams treat a security questionnaire like administrative overhead. That framing is costly.
A single third-party breach can expose customer data, trigger regulatory fines, and damage years of trust in a single event.
The numbers back this up. According to the IBM Cost of a Data Breach Report, the average cost of a data breach for organizations is $4.88 million in 2024.
Recently, OpenAI had a third-party security incident is another great example of why you should pay more attention to security.
Third-party relationships are one of the most common entry points attackers use to gain access.
The Third-Party Risk Problem
Third-party risk is growing year over year. The same IBM report found the average breach takes 277 days to identify and contain. That is nearly nine months of live exposure before the problem is even detected.
The breach often does not start inside your walls. It begins inside a vendor's system. A security questionnaire gives you a structured way to identify a weak vendor before they become the source of a costly incident.
"In 2024, supply chain and third-party attacks were involved in a significant portion of all recorded breaches, with vendors and service providers serving as the most common indirect access point." – World Economic Forum Global Cybersecurity Outlook
Supply chain management now depends heavily on security assessment processes. Your supply chain is only as strong as the weakest link in your vendor ecosystem.
Without documented due diligence on each third-party vendor, you cannot know where your real risk sits.
The Revenue Case
There is a revenue case here. Not just a risk one. Enterprise buyers now require vendors to pass a security assessment before a contract gets signed. Your security posture is tied directly to your ability to close deals in competitive markets.
For companies in healthcare, finance, and SaaS, third-party oversight is not optional.
Frameworks like SOC 2, HIPAA, and PCI-DSS all require documented evidence of third-party vendor assessment. No documentation means a compliance gap.
Vendors who respond to security questionnaires well tend to win more deals.
A fast, polished, evidence-backed response tells buyers that you run a real security program. That is a competitive advantage in any enterprise sales cycle.
Now, let us look at the different types of security questionnaires you will encounter.
Types of Security Questionnaires
Not every security questionnaire looks the same. Some are internal self-assessments.
Others go to third-party vendors before signing a contract. Some map directly to specific data compliance standards, such as GDPR or SOC 2.
Before diving into standardized frameworks, it helps to understand the three main use-case categories. Knowing which category a questionnaire falls into tells you immediately what the buyer is trying to learn.
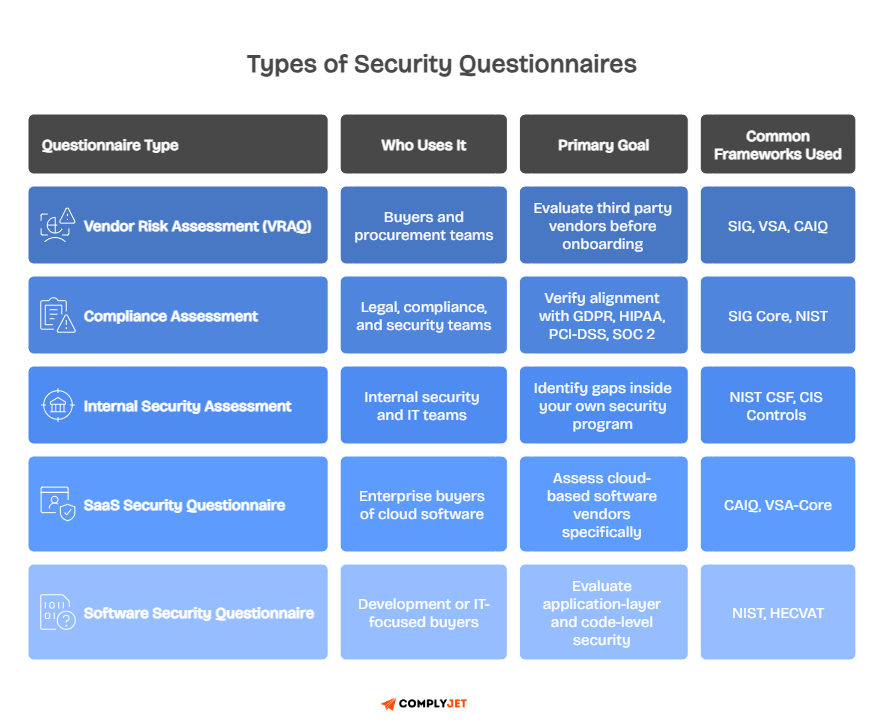
The three main types by use case are:
- Vendor Risk Assessment Questionnaire: Sent to third-party vendors before a contract is signed to evaluate their data security and access controls
- Compliance Assessment Questionnaire: Maps vendor practices to specific regulations, including GDPR, HIPAA, PCI-DSS, and SOC 2
- Internal Security Assessment: A self-evaluation used to identify security gaps inside your own organization
Now, let us go deeper into the standardized frameworks. These are the specific formats you will encounter most often when handling a formal security assessment questionnaire.
SIG: Standardized Information Gathering
The SIG questionnaire was developed by Shared Assessments. It is one of the most comprehensive cybersecurity questionnaire frameworks available. It comes in three versions, each built for a different vendor risk level.
SIG Core covers around 855 questions across 19 risk domains. It is designed for high-risk enterprise vendor assessments. SIG Lite uses about 126 questions and is suitable for preliminary reviews or lower-risk third parties.
Custom SIG lets you pull from a library of over 1,800 questions to build an assessment tailored to a specific vendor relationship.
Founders' Tip: Do not send SIG Core to every vendor. Right-size it based on actual risk. A vendor with no access to your customer data does not need 855 questions. A vendor with production system access and data custody absolutely does.
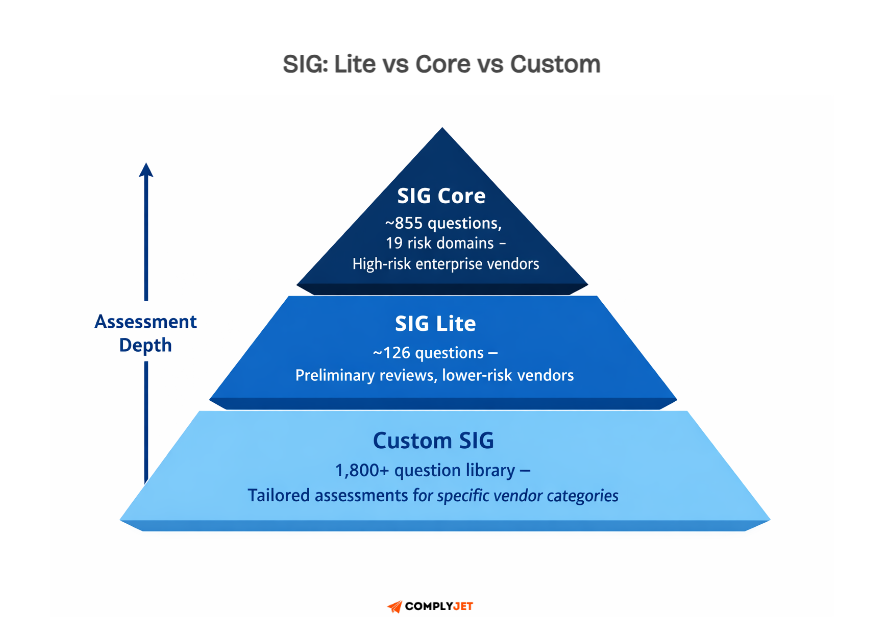
SIG is the gold standard for standardized information gathering in regulated industries. If you work with healthcare or financial services buyers, you will see SIG Core referenced regularly in their procurement and vendor onboarding workflows.
CAIQ: Consensus Assessments Initiative Questionnaire
The CAIQ was developed by the Cloud Security Alliance. It is built specifically for cloud environments. It covers 17 domains focused on cloud service provider controls and security responsibilities.
If you are assessing SaaS vendors, cloud infrastructure providers, or any platform using shared infrastructure, the CAIQ is the proper framework.
It asks questions that a general cybersecurity questionnaire will often miss. Things like how a cloud provider isolates tenant data and manages virtualization security.
The CAIQ is especially relevant when completing a saas security questionnaire review.

Enterprise buyers of cloud-based software use it to understand the shared responsibility model between their cloud service provider and themselves. Your answers here need to be very specific.
VSA: Vendor Security Alliance Questionnaire
The Vendor Security Alliance questionnaire was created by a coalition of companies, including Airbnb, Atlassian, Docker, Dropbox, and Uber. The goal was simple. Eliminate the chaos of every company building its own vendor security questionnaire from scratch.
It comes in two versions. VSA-Full covers vendor security in depth and is used by thousands of companies globally.
VSA-Core focuses on the most critical controls and adds a privacy section covering both CCPA and GDPR compliance. Both versions are free to download on the VSA website.
The VSA framework takes a practical position on third-party risk. The level of assessment should match how sensitive the data is that the vendor accesses and how much of it they handle. Not all vendors deserve the same depth of scrutiny.
HECVAT
HECVAT stands for Higher Education Community Vendor Assessment Tool. It was built for colleges and universities that evaluate cloud-based vendors and software platforms. It focuses specifically on data protection standards common in higher education environments.
Higher education institutions face a unique combination of compliance requirements. Student data privacy laws, open network environments, and cloud adoption all create specific security risks that a standard vendor security questionnaire does not address well.
HECVAT comes in three versions.
HECVAT fully covers around 265 questions for comprehensive cloud vendor assessments. HECVAT Lite is a faster option for lower-risk vendors. The On-premises version handles the evaluation of non-cloud application security.
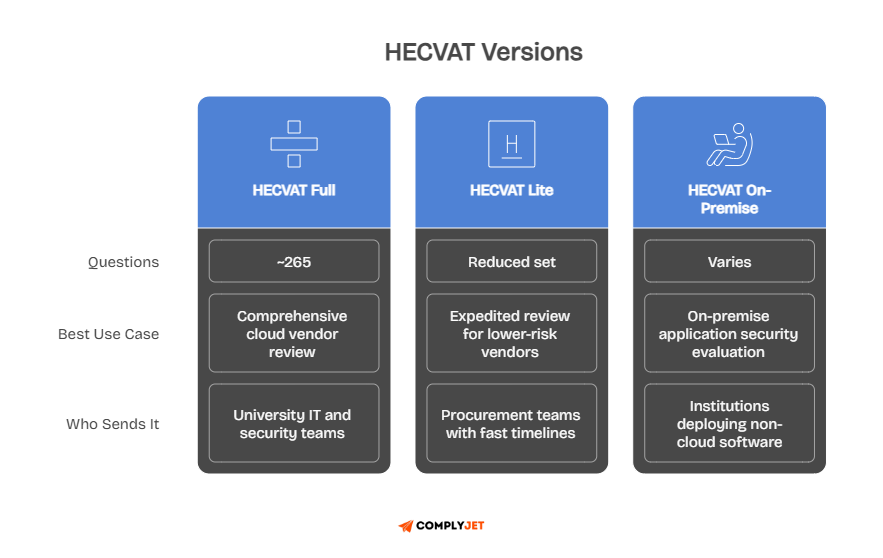
If you sell software to universities, having HECVAT responses ready will accelerate your sales cycle significantly.
NIST-Based Questionnaires
NIST SP 800-171 is a cybersecurity standard from the National Institute of Standards and Technology. It focuses on companies that handle Controlled Unclassified Information under US government contracts.
Complying with NIST SP 800-171 also satisfies much of NIST SP 800-53, which underlies both FISMA and FedRAMP compliance requirements. If you sell to federal agencies or operate in the defence supply chain, NIST-based questionnaires are a standard part of your third-party vendor assessment process.
Knowing which framework applies to your buyer helps you prepare the correct answers before a questionnaire even arrives. Now, let us look at what a security questionnaire template actually contains.
Security Questionnaire Template: Core Sections
Whether you receive a SIG questionnaire or a buyer-built compliance questionnaire, most security questionnaires share the same core structure. These sections are the building blocks of nearly every security questionnaire template used across industries today.
Knowing these sections before a questionnaire arrives gives you a real advantage. When a new one lands in your inbox, you recognise the categories immediately. Your team already knows where to find the policies and evidence each section requires.
The core sections in a standard security questionnaire template are:
- Company and Security Governance: CISO ownership, security program structure, accountability
- Data Security and Protection: Encryption standards including AES-256 and TLS 1.2 or higher, data classification, and data masking
- Access Controls: MFA, RBAC, identity access management, access review cadence
- Incident Response: Incident response policy, breach notification timelines, and incident response plans
- Vulnerability Management: Penetration testing, patch management, threat vulnerability management
- Change Management: Change management policy, pre-production testing, code validation process
- Business Continuity: Disaster recovery plans, backup procedures, operational resilience
- Cloud and Application Security: Cloud service provider controls, SDLC practices, web application firewalls, API security
- Compliance and Privacy: GDPR, HIPAA, SOC 2, ISO 27001, privacy compliance documentation
Right-sizing matters a lot here. A cloud provider with production environment access and custody of customer data deserves a thorough, multi-section assessment. A marketing vendor with no data access probably needs a much shorter one. Always match the depth of your compliance questionnaire to the actual risk the vendor relationship carries.
For SaaS companies, the cloud security and application security sections carry the most weight.
Enterprise buyers want to know how you secure the product they are buying, not just what policies exist in a shared drive. A strong SaaS security questionnaire template always prioritises those two sections.
Buyers are not just reading your answers. They are evaluating whether you have a real security program or just a document library. Evidence is the difference.
ComplyJet ships pre-built security questionnaire templates mapped to major frameworks, ready to deploy with no setup time.
Start your free trial and skip the configuration work entirely.
Security Questionnaire Examples and Sample Questions
Knowing the sections is one thing. Knowing what the actual questions look like is another. These security questionnaire examples give you a clear picture of what to expect when a new assessment lands in your inbox.
Questions range from simple yes-or-no to requests for detailed explanations, policy documents, and supporting evidence files. The best way to prepare is to read real examples in advance so nothing catches your team off guard during a live sales cycle.
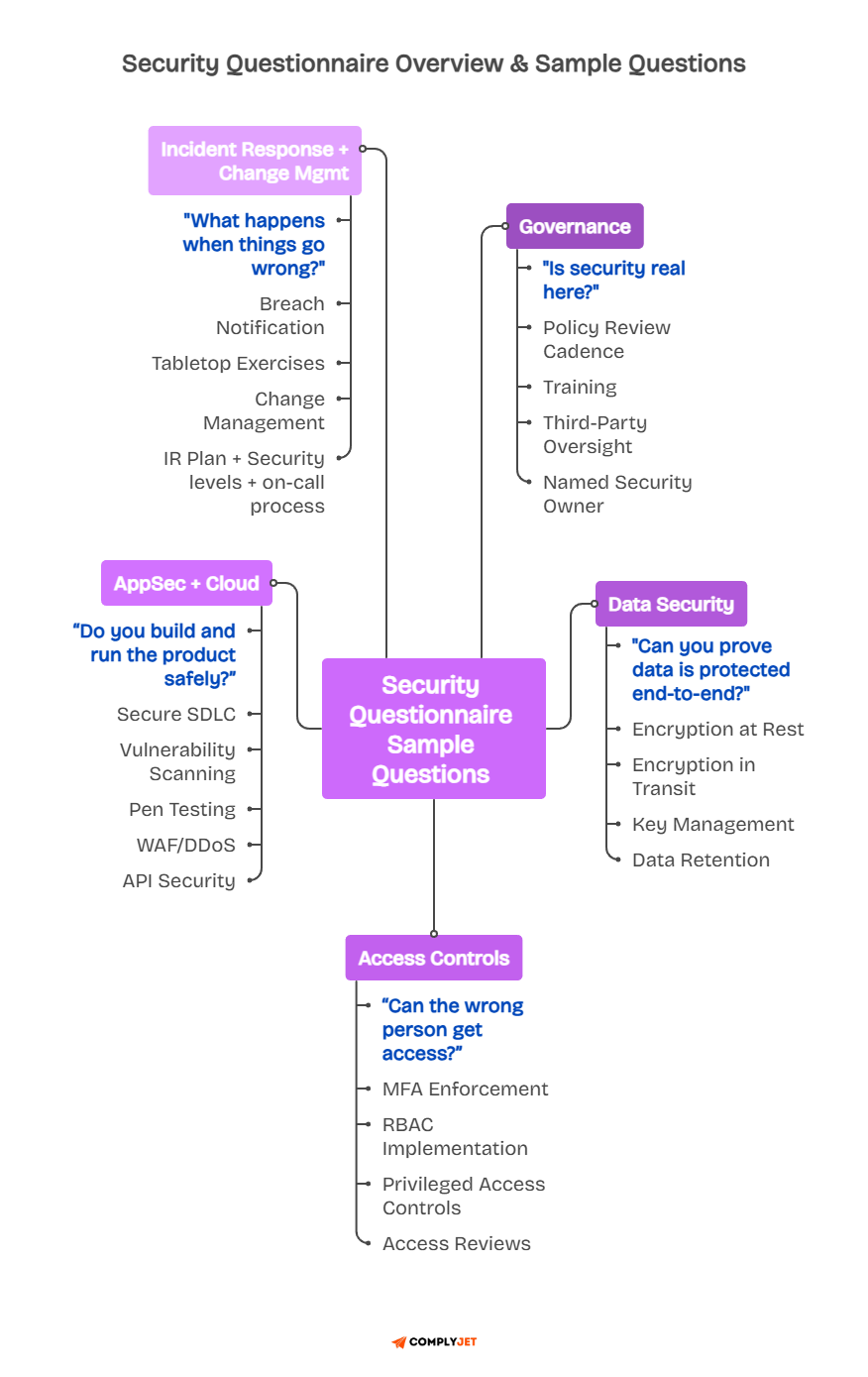
1. Basic and Governance Questions
These questions appear in almost every security questionnaire. They establish whether your organization has a real security program and who is accountable for running it day to day.
Common governance questions include: Does your organization have a cybersecurity policy? How often is it reviewed? Is there a designated CISO or data protection officer? Have you ever experienced a significant cybersecurity incident? Do you outsource any IT or security functions to third parties?
Founders' Tip: If you outsource IT or security functions to third parties, be ready to show that your own vendors have also been assessed. Enterprise buyers increasingly ask about your supply chain, not just your direct security controls. Your vendor's gaps become your gaps.
These questions reveal whether security is a real discipline inside your company or an afterthought. Buyers with mature procurement processes read governance answers carefully. Vague answers here will send them straight to your competitor.
2. Data Security and Encryption Questions
Data security questions go straight to how you protect customer data. Buyers want specifics, not reassurances. If you cannot name your encryption standard, that is a red flag in any software security questionnaire review.
A strong answer to an encryption question sounds like this. Data at rest is encrypted using AES-256. Data in transit is protected using TLS 1.2 or higher. Encryption keys are managed through a dedicated key management service with strict, documented access controls and regular rotation schedules.
Your data protection measures need to be specific and verifiable. Generic statements like "we take security seriously" mean nothing in this context. Buyers want to see the standard, the tool, and the policy that governs it.
3. Access Control and Identity Questions
Access control is one of the highest-risk areas in any vendor relationship. If the wrong person can access the bad system, your customer data is exposed. Buyers understand this. They ask about it directly, and they want evidence, not assurances.
Expect questions like these. Do you enforce multi-factor authentication across all systems? How is role-based access control implemented? How often do you conduct user access reviews? How do you manage privileged admin accounts?
Regular access reviews matter as much as the controls themselves. A vendor that enforces MFA but never audits who still has active access is still a real risk. Buyers who know what they are doing ask for both the access control policy and the most recent access review report to verify that it is being followed.
4. Application Security and Cloud Questions
Application security questions are common in any saas security questionnaire. Buyers want to know how you build and maintain your product, not just how you store data. These questions probe your development process itself and your cloud security posture.
Common questions include: Do you conduct penetration testing, and how often? Do you use a web application firewall? How do you secure external APIs? Who is responsible for security in your cloud environment?
According to the Verizon Data Breach Investigations Report, web application attacks are consistently among the top breach vectors year over year. Buyers asking about your WAF and API security are asking the right questions.
Cloud security, in particular, requires you to understand the shared responsibility model clearly. Your cloud service provider secures the infrastructure. You are responsible for ensuring your data, your identity management, and your application configuration. Make sure your answers accurately reflect that split.
5. Incident Response and Change Management Questions
Incident response questions test whether your response plan is real or just a document. Buyers want to know what happens when something goes wrong and how quickly you will tell them about it. They want a process, not a promise.
Expect questions like these: What is your incident response policy? What is your average time to detect and contain a breach? How do you notify customers in the event of a data breach? Is code tested in a pre-production environment before it reaches production?
Change management questions often appear alongside application security ones. A buyer wants to know that the new code goes through a controlled process before it touches their data in your production environment. Your change management policy should document that process clearly.
How to Answer a Security Questionnaire
Answering a security questionnaire well is not about saying the right things. It is about having the right systems in place before the questionnaire arrives.
Teams that scramble for answers tend to give inconsistent ones. Buyers notice inconsistency immediately.
The real goal is to reach a point where answering a questionnaire feels like retrieval rather than creation. The hard work happens before the questionnaire shows up. The response is just the output of preparation done earlier in a structured, ongoing process.
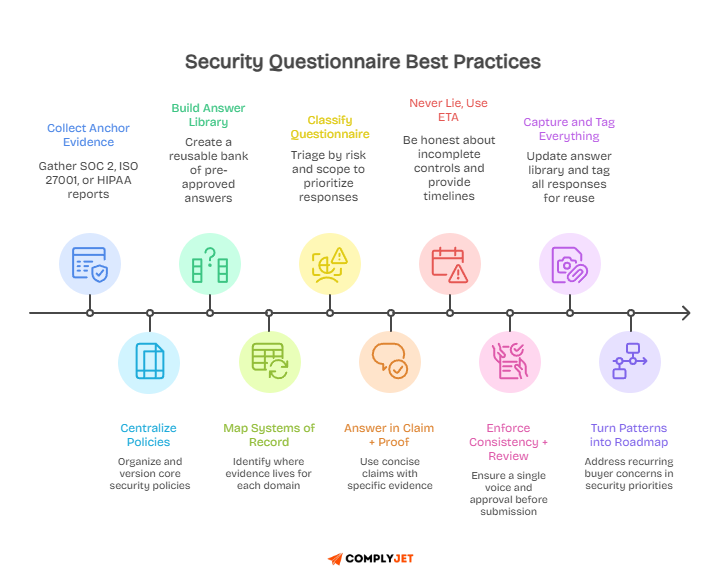
Before You Start: Build Your Foundation
Start by gathering your certifications. A SOC 2 report, ISO 27001 certification, or HIPAA attestation becomes your pre-built evidence base for dozens of questions at once.
These documents do much of the answering before you type a single word.
Document your core policies before any questionnaire arrives. Your information security policy, access control policy, incident response policy, and change management policy should all live in one accessible, centralized location.
When a question comes in, you should be able to find the right policy in seconds, not hours.
Build a centralized answer library. Every question you have ever been asked, and every approved answer your team has given, should live in one searchable place. This is the most valuable operational asset you can build for responding to security questionnaires at speed and scale.
While Answering: The Core Rules
Be direct. Use clear, active language. Do not pad answers with vague reassurances. Buyers read hundreds of questionnaire responses, and they spot filler immediately. Short, specific answers backed by evidence always beat long, uncertain ones.
Be honest about security gaps. If a control is still being implemented, say so clearly. Include a remediation plan with a realistic timeline. A transparent vendor who acknowledges a gap and shows a clear path to closing it is far more credible than one who checks every box without attaching a single piece of evidence.
Founders' Tip: Never answer yes to a security control that is not yet in place. Buyers conduct audits. They will find the gap. Being caught in an inconsistency destroys trust permanently. A gap with a remediation plan and a clear timeline is always the better option.
Be consistent. Use the exact phrasing and evidence across all related answers within a questionnaire.
One person answering access control questions differently from another person answering incident response questions is a red flag. Route all responses through a defined review and approval step before submission.
After Completion: Build for the Future
Once you submit a questionnaire, do not file it away and move on. Log every question and approved answer into your answer library. Tag each entry by domain and framework so retrieval is fast the next time a similar question arrives from a different buyer.
Use patterns in recurring questions to improve your actual security program.
If you are consistently asked about MFA and your answer is always "in progress," that is a clear signal to prioritize it. Security questionnaires are surprisingly helpful in identifying fundamental security gaps in an honest and actionable way.
Every completed questionnaire makes the next one faster. Every approved answer enriches your library.
Every gap you close improves both your security posture and your response quality. The process compounds over time when you treat it seriously.
ComplyJet's answer library centralizes your pre-approved responses so your team never starts from scratch again.
See our pricing and find out how accessible it actually is.
Security Questionnaire Automation: How It Works
Manually answering a security questionnaire is slow and inconsistent. One person writes one answer. Another person writes a different answer to the same question two months later on a different deal. The buyer notices.
Inconsistency is a trust problem with direct commercial consequences.
Security questionnaire automation solves this at the process level.
Instead of hunting through email threads and shared drives, your team gets suggested answers pulled from a vetted, centralized knowledge base. The process becomes faster, more consistent, and far more scalable as your deal volume grows.
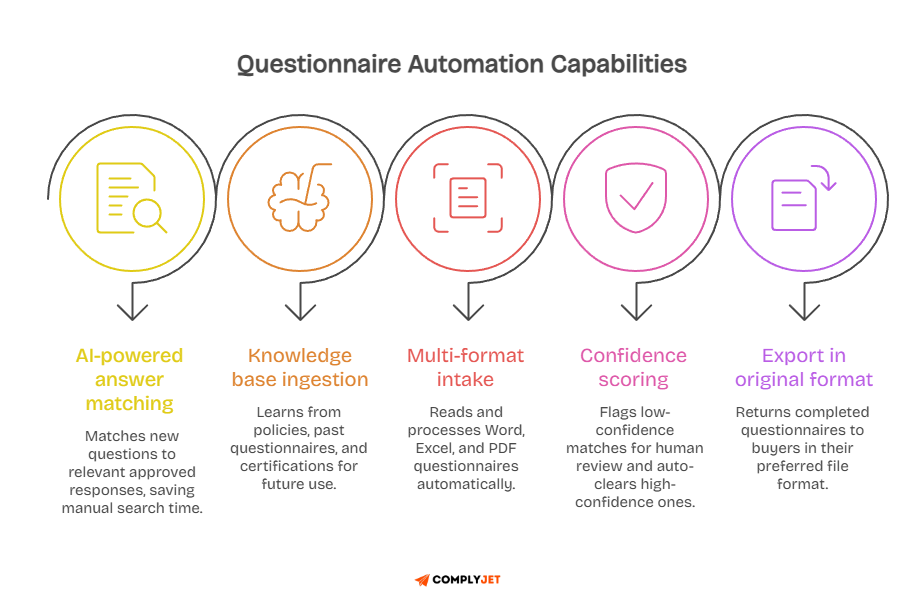
What Is Security Questionnaire Automation?
Security questionnaire automation uses AI to match incoming questions to pre-approved answers stored in your knowledge base. You feed the system your past questionnaires, internal policies, and certifications. It learns from that content and applies it when new questions arrive.
The core mechanism is retrieval, not generation. The system is not inventing answers.
It is finding the best match from the responses your security team has already reviewed and approved. Your team still reviews the output, but they spend minutes rather than days doing so.
According to IBM, organizations using security AI and automation extensively save an average of $2.22 million compared to those that do not. Questionnaire automation is a direct application of that same principle.
Automation also creates a complete audit trail. Every response is tracked by the approver, the evidence attached, and the date it was submitted. That level of documentation supports your security compliance posture during audits and enterprise security reviews.
How It Works: Step by Step
You start by building your knowledge base. Upload past security questionnaires, internal policies, SOC 2 reports, and certification documents. The system indexes all of it and makes it searchable by question type, domain, and keyword.
When a new questionnaire arrives, the tool ingests the file and scans each question. It suggests the best-matching answer from your library, along with a confidence score. High-confidence answers go straight to your reviewer. Lower-confidence ones are flagged for manual review by your security team.
Your team reviews the flagged items, edits where needed, and approves the final set of responses. The tool then exports the completed questionnaire in the buyer's original format. Every approved answer gets added back to the library to improve future suggestions.
The Business Case for Automation
The efficiency argument is real. Teams that automate questionnaire responses consistently report cutting turnaround times from multiple weeks down to hours. That time saving directly affects how quickly your sales team can advance a deal through procurement.
There is a compliance argument, too. Every automated response comes with a complete audit trail. Who approved it? What evidence was attached? When it was submitted. That level of documentation supports your security data compliance standards during formal audits and enterprise reviews.
Founders' Tip: Automation does not replace your security team. It removes low-value, repetitive work so your security team can focus on actual security improvements rather than answering the same access-control question for the fifteenth time this quarter.
Scaling manual questionnaire responses caps out quickly. As your deal volume grows, your security team becomes the bottleneck. Automation breaks that constraint. You can handle ten times the questionnaire volume without ten times the headcount.
What to Look for in Security Questionnaire Software
The best security questionnaire software does more than auto-fill answers. It connects your knowledge base to your existing workflow. When evaluating tools, look for AI-powered answer suggestions that clearly cite the source document. Not ones that guess without attribution.
You also need multi-format intake. The tool should automatically handle Word, Excel, and PDF questionnaires. And you need structured SME routing so the right person reviews the right question rather than it disappearing into a shared inbox for a week.
Key features to evaluate in security questionnaire software:
- AI-powered answer suggestions with citation-backed generation
- Centralized answer library with continuous learning from approved responses
- Multi-format intake covering Word, Excel, and PDF
- SME routing and collaboration workflows
- Slack and CRM integrations to keep questionnaires visible in your existing tools
- Trust the Center for buyer self-service before a formal questionnaire arrives
- Full audit trail on every response for compliance and accountability
Now, let's see what's best on the market.
Top Security Questionnaire Automation Software
The security questionnaire software market has matured quickly. A few years ago, most teams answered questionnaires in spreadsheets with no structure or process. Today, dedicated platforms handle the entire workflow from intake to delivery with AI at the center of the response process.
Each tool has a distinct focus. Some prioritize compliance breadth. Others prioritize pure response speed. Knowing the difference helps you pick the one that matches your actual bottleneck rather than buying a platform you will underuse.
The leading platforms in the space today include:
- Vanta: an all-in-one compliance platform with an integrated questionnaire automation module
- Drata: GRC-focused with live compliance posture mapped directly to questionnaire answers
- Responsive, formerly RFPIO: enterprise-grade with a Trust Center and multi-format intake at scale
- Conveyor: sales-team focused with a buyer portal and significant response time reduction
- Sprinto: fast-growth SaaS teams needing GRC and questionnaire automation in one unified platform
Questionnaire Automation with ComplyJet
ComplyJet is purpose-built for questionnaire automation and vendor security reviews.
It is designed for teams where the primary bottleneck is not broad compliance management. It is answering incoming security questionnaires quickly and consistently without first building a full GRC infrastructure.
If you are an early-stage SaaS company without a full compliance program in place, you need a tool that solves your immediate problem first. Buying a full compliance platform when your actual bottleneck is questionnaire turnaround time is expensive and slow to deploy.
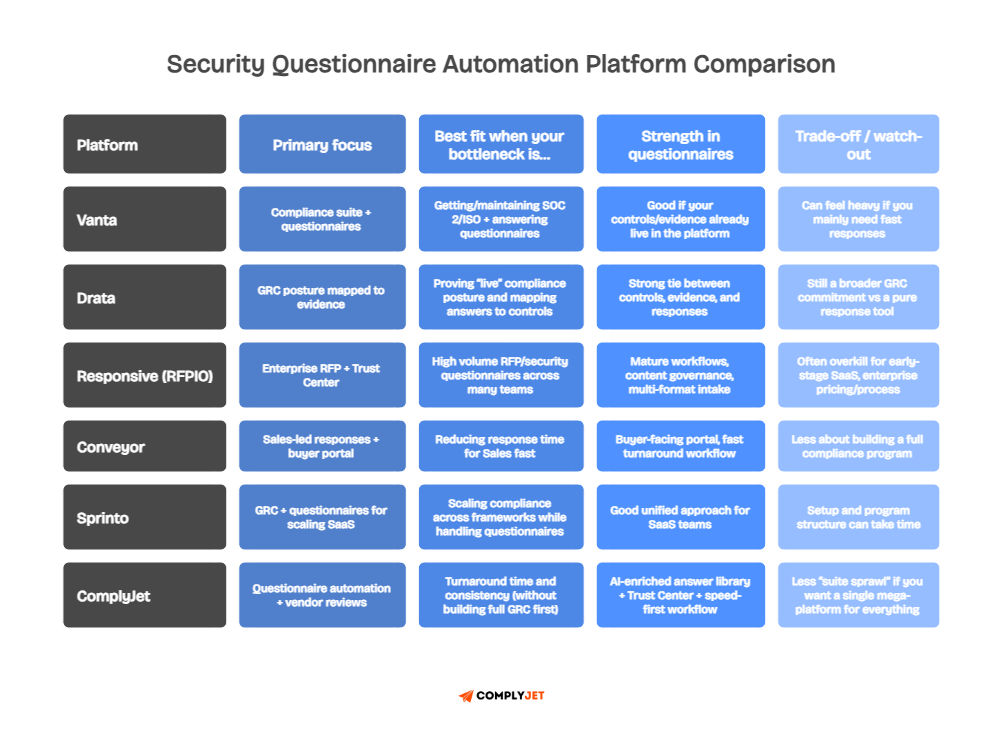
Where other platforms bundle questionnaire automation into a premium compliance suite, ComplyJet gives you the core capability you actually need right now at a price that works for growing teams.
The answer library is AI-enriched and continuously learns from your inputs. The Trust Center lets buyers self-serve before a formal questionnaire is ever sent. And the response process is built for speed from the ground up.
See how teams like yours are closing deals faster with ComplyJet. Read our customer stories and see the actual results for yourself.
Best Practices for Vendors and Buyers
A good security questionnaire process is not a one-time event. It is a discipline. Vendors who treat it that way win more deals and build more trust over time. Buyers who treat it that way take on more risk before incidents or regulatory problems occur.
These practices apply whether you are sending a questionnaire or receiving one. They separate teams that are always scrambling from those with a real, repeatable process that actually improves their security posture.
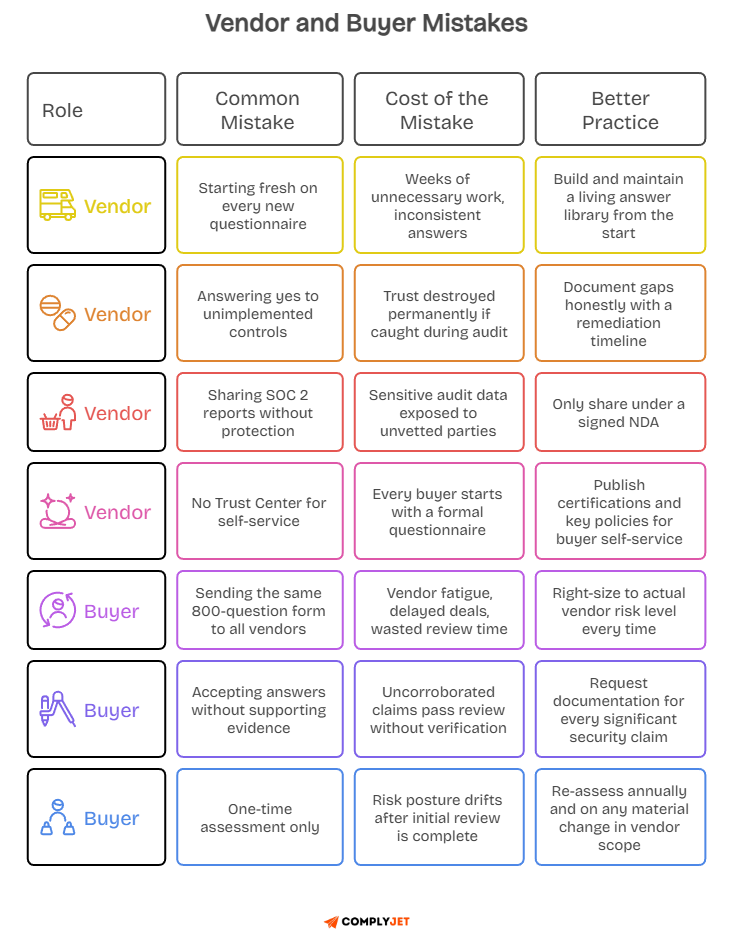
For vendors
The single most impactful step you can take is getting certified early. A SOC 2 report or ISO 27001 certification pre-answers dozens of common questions. It signals to buyers that your security program is real, audited, and independently verified. That signal alone can move a deal forward faster than any sales pitch.
Maintain a living answer library as your single source of truth. Every approved answer, tagged by domain and framework, lives in one searchable location.
Keep your Trust Center or security page updated so buyers can self-serve before a formal questionnaire is ever sent. Be transparent about gaps.
A remediation timeline builds more trust than a false positive checkbox. And automate to scale. Manual responses cap out quickly as your pipeline grows.
Founders' Tip: Your Trust Center is pre-sale leverage. When a buyer can answer their own security questions before reaching out, your sales cycle shortens. Publish your certifications, your security overview, and your key policies there. Update it every time you earn a new certification.
For buyers
The most common mistake is treating all vendors the same. A cloud provider with production environment access and custody of sensitive customer data deserves a rigorous, multi-section assessment based on a complete standardized framework.
A vendor with no data access and no system integration does not need that same depth of review.
Adopt standardized frameworks such as the SIG, CAIQ, or VSA rather than building questionnaires from scratch.
Treat assessments as ongoing relationships rather than one-time checkboxes. Re-assess annually and whenever vendor scope changes significantly.
Always request evidence alongside answers. Access to review reports, penetration test results, and SOC 2 reports matters far more than uncorroborated yes-or-no responses.
Frequently Asked Questions about Security Questionnaires
These are the questions that come up most often in conversations about security questionnaires, cybersecurity frameworks, and vendor risk management. The answers below are written for teams that want practical clarity, not textbook definitions.
What are the 7 types of cybersecurity?
The seven types of cybersecurity reflect the different layers where threats enter and cause damage.
Network security protects communication channels and infrastructure. Application security protects software from vulnerabilities. Information security maintains data confidentiality, integrity, and availability.
Operational security covers risk assessments, employee training, and response planning.
Disaster recovery and business continuity ensure critical systems can be restored after an attack.
End-user education addresses the human layer of risk. Mobile security covers device and wireless channel protection.
Security questionnaires are designed to evaluate vendor maturity across all seven domains. When a questionnaire feels long, it is because it is trying to cover the full landscape of risk exposure in a single, structured document.
What are the 5 C's of cybersecurity?
The five C's provide a practical lens for evaluating whether a security program covers what it needs to. Change means adapting continuously to evolving threats and business models.
Compliance means meeting regulations your organization is subject to, from GDPR and HIPAA to newer frameworks like NIS2 and DORA. Cost means making risk-based investment decisions so your security budget creates the most protection per dollar spent.
Continuity means planning for the worst with tested recovery plans, immutable backups, and operational resilience built into your infrastructure. Coverage means maintaining full visibility across your attack surface with consistent monitoring in place at all times.
A well-structured security questionnaire tests a vendor across all five dimensions simultaneously. That is one reason a thorough compliance questionnaire is hard to shortcut without the work showing clearly in the responses.
What are the four types of security?
The four foundational cybersecurity domains form the building blocks of any mature security program. Governance, Risk, and Compliance covers how policies, standards, and accountability are structured.
Network Security protects infrastructure from unauthorized access and external threats. Application Security secures software from vulnerabilities in code, APIs, and dependencies.
Incident Response and Recovery ensures the organization can identify, contain, and recover from a breach with a documented, tested process.
Security questionnaires are structured around these four domains. When you know which domain a question belongs to, you can find the right policy or evidence much faster.
What are the 5 steps of a security risk assessment?
A security risk assessment questionnaire formalizes a five-step evaluation process.
First, identify your assets and the data associated with them.
Second, identify the threats and vulnerabilities that could affect those assets.
Third, analyze and prioritize risks based on their likelihood and potential impact.
Fourth, implement the proper security controls to address the risks you have identified and documented.
Fifth, document your findings and establish continuous monitoring to prevent the assessment from going stale as threats evolve.
This process applies equally to internal security assessments and third-party vendor evaluations.
What is the Vendor Security Alliance Questionnaire?
The VSA Questionnaire is a free, standardised security assessment tool created by the Vendor Security Alliance. Its founding coalition includes Airbnb, Atlassian, Docker, Dropbox, and Uber. It was built to reduce the burden of every company creating its own vendor questionnaire from scratch.
It comes in two versions. VSA-Full covers vendor security comprehensively and is used globally by thousands of companies.
VSA-Core focuses on the most critical controls and adds a privacy section covering CCPA and GDPR compliance requirements. Both versions are free to download directly from the VSA website.
What is an application security questionnaire?
An application security questionnaire evaluates security at the software layer. It focuses on how a vendor builds, tests, and maintains their product rather than just how they store data.
This type of questionnaire is common during SaaS vendor onboarding because enterprise buyers want to know that the product itself is secure, not just the company behind it.
Questions typically cover secure SDLC practices, code review and testing processes, pre-production environment controls, web application firewall use, API security, and patch management cadence. It is often part of a broader software security questionnaire or cybersecurity assessment questionnaire review process. Having a documented secure development lifecycle is the most important thing you can show here.
How do you speed up responses to security questionnaires?
The fastest teams build an answer library before the questionnaire arrives. Every question they have ever been asked and every approved answer their security team has given lives in one central, searchable location.
When a new questionnaire comes in, the response process is retrieval, not rewriting from scratch.
On top of that foundation, they layer security questionnaire automation. AI automatically matches incoming questions to library answers. Their security team reviews flagged items rather than writing from scratch. The result is a process that takes hours instead of weeks and keeps sales cycles moving without security becoming the bottleneck on every deal.
What is an InfoSec questionnaire?
An InfoSec questionnaire is a short form of an information security questionnaire.
It covers how an organization manages data protection, access controls, encryption standards, and security governance across its systems and processes. You will see this term used for both internal self-assessments and third-party vendor evaluations.
It is also referred to as an IT security questionnaire or a cybersecurity assessment questionnaire, depending on who is sending it and its primary focus.
The terminology differs by industry and team. The purpose is consistent: evaluate whether the security program is real, documented, and actually functioning as described. If you are building a vendor risk management process, an infosec questionnaire is often the most practical and accessible starting point.
The Bottom Line
That sales rep from the beginning of this guide no longer has to be stuck.
They have a framework now. They know what type of questionnaire arrived, what sections it covers, how to answer it with objective evidence, and how to automate the process so the next one takes hours instead of weeks.
Security questionnaires are not going away.
If anything, they are getting longer and more detailed as data protection requirements grow globally.
The teams that treat them seriously, who build real answer libraries, automate where they can, and stay honest about security gaps, are the ones who close more deals and build lasting trust with enterprise buyers over time.
Your security posture is your competitive advantage. Make it visible, document it, and make it easy to share when a buyer asks.
ComplyJet is built for precisely this challenge. Helping security and sales teams respond faster, win more deals, and build buyer confidence from the very first questionnaire.
See what is possible first in your exclusive free trial and find out how your team gets there.