You start preparing for ISO 27001, assuming it’s a structured process focused on security policies, risk management, and certification. But somewhere along the way, ISO 27002 comes into the picture, and suddenly things are less clear.
Now you’re wondering whether you need both standards, whether ISO 27002 is another certification, and whether skipping it could create problems later. This confusion is common, especially for teams going through compliance for the first time.
At its core, the issue comes down to two things: the difference between a certification and a guideline, and the difference between a framework and the controls that support it. Without understanding this early, teams often spend time on the wrong areas or overcomplicate their approach.
This guide is not a theoretical breakdown of ISO standards. It is designed to help you understand what actually matters, how ISO 27001 and ISO 27002 work together, and what you should focus on to move forward efficiently.
If you're already exploring ISO compliance and want a more structured approach, book a quick demo with ComplyJet to see how teams are getting ISO 27001-ready without unnecessary complexity.
What is ISO 27001?

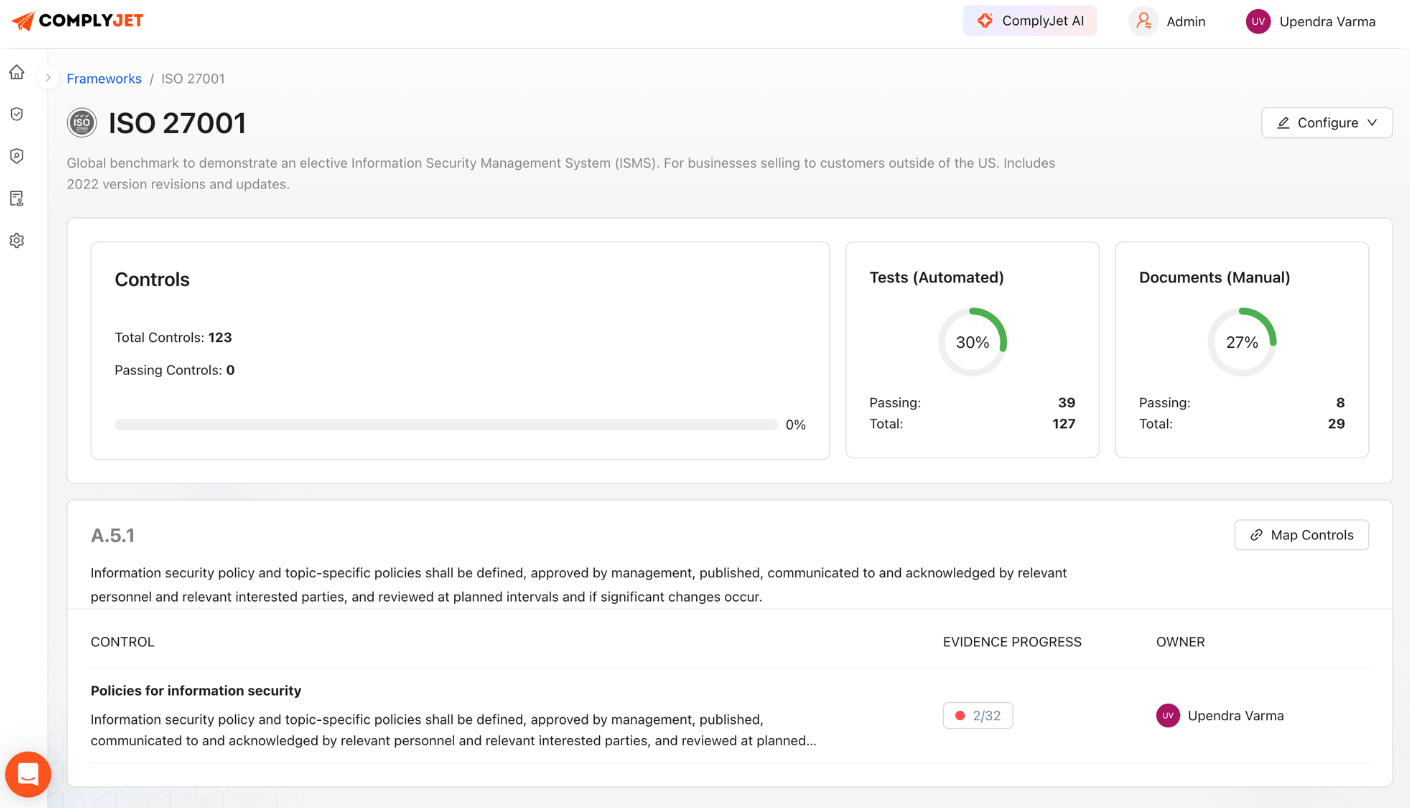
ISO 27001 is a certifiable information security standard that helps organizations manage risk in a structured way. It is not just about writing policies or passing an audit. It is about building a system that ensures your data, systems, and processes are consistently protected.
This system is called an Information Security Management System (ISMS). In simple terms, an ISMS helps you identify risks, apply the right controls, and continuously monitor and improve your security posture over time. Instead of reacting to problems, you are actively managing them.
At a practical level, ISO 27001 includes a few key parts. You start with risk assessment, where you identify what could go wrong and what impact it could have. Then you apply security controls, which are listed in Annex A and cover areas like access control, incident response, and data protection.
Finally, you go through audits and certification, where an external auditor verifies that your system meets the required standards.
By the numbers: According to the ISO Survey 2024, the number of valid ISO 27001 certificates nearly doubled in a single year, jumping from 48,671 in 2023 to 96,709 in 2024 across more than 179,877 certified sites globally. That represents one of the largest single-year surges in the standard's history.
For SaaS companies, ISO 27001 is often less about best practice and more about necessity. Enterprise clients expect it, security questionnaires demand it, and without it, trust becomes a barrier to closing deals. Approximately 75% of enterprise procurement departments now mandate ISO 27001 as a prerequisite, often disqualifying vendors before technical discussions even begin.
If ISO 27001 feels like too many moving parts, that’s because it is. Tools like ComplyJet simplify this into a structured, trackable workflow so you can focus on progress instead of confusion.
What is ISO 27002? (And Why It Confuses Everyone)

ISO 27002 is a guideline for information security controls. It is not a certification standard, which means you cannot get audited or certified against it.
Its role is to provide practical guidance on how security controls can be designed, implemented, and managed within an organization.
This is where most of the confusion comes from. Since ISO 27002 talks about controls like access management, incident handling, and data protection, it often feels like something you are required to implement fully. In reality, it is meant to be used as a reference, not a strict checklist.
ISO 27002 focuses on how controls should work in practice.
For example, in access control, it explains how to define user roles, assign permissions, and review access regularly. In incident management, it provides guidance on how to report, handle, and resolve security incidents in a structured way.
The value of ISO 27002 lies in its level of detail. It helps teams move from broad ideas to clear implementation by reducing guesswork and providing direction on what good security practices look like.
At the same time, it is flexible. Organizations are expected to adapt its guidance based on their size, industry, and risk level, rather than follow it exactly as written.
What is the Difference Between ISO 27001 Vs 27002
Understanding the difference between ISO 27001 and ISO 27002 becomes easier when you look at how they are used in practice. While both are part of the same family of standards and focus on information security, they serve very different roles.
One is designed to help organizations build and prove a structured system, while the other focuses on how security controls are applied at an operational level.
Here is a detailed comparison to make that distinction clear:
Strategic vs Operational Difference
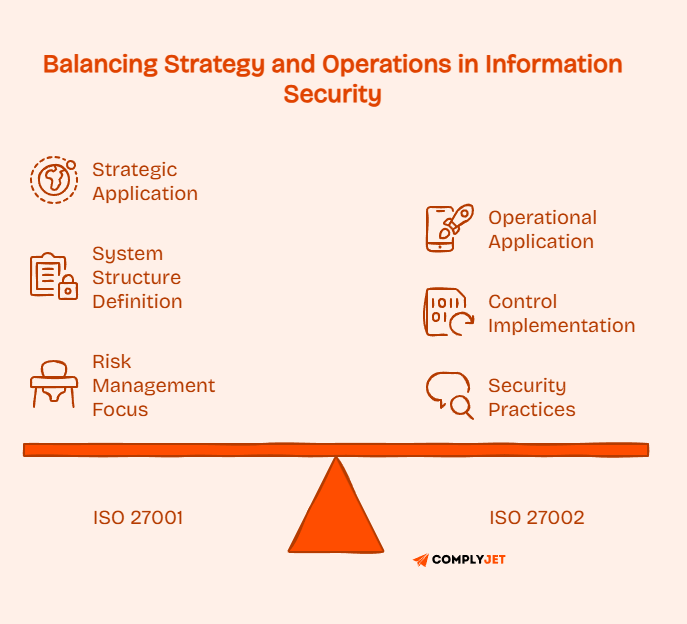
The core difference between ISO 27001 and ISO 27002 lies in how they are applied.
ISO 27001 is strategic. It defines the structure of your information security system and ensures that it meets a recognized standard. It focuses on governance, risk management, and accountability.
ISO 27002 is operational. It focuses on how individual controls are implemented and managed in day-to-day operations. It provides direction on how to apply security practices in a consistent and effective way.
This distinction is important because organizations often confuse the need for structure with the need for detail. In reality, both are important but serve different purposes.
Why People Mix Them Up
The confusion usually happens for a few reasons.
First, both standards belong to the same ISO 27000 family and use similar terminology, especially around controls and security practices. This makes them appear interchangeable at a glance.
Second, they are often introduced together during the compliance journey. When teams start exploring information security standards, they come across both at the same time without clear guidance on how they differ.
Third, both deal with the same subject areas such as access control, incident management, and data protection. However, they approach these areas from different levels, which is not always obvious without deeper context.
Because of this, many teams assume that ISO 27002 is an additional requirement rather than a supporting resource.
You can also give a quick read to ISO 27001 vs SOC 2: The Definitive Guide (2026)
How ISO 27001 and ISO 27002 Actually Work Together
The easiest way to understand how ISO 27001 and ISO 27002 work together is by looking at the connection through Annex A.
Annex A is a section that lists a set of security controls covering areas like access management, incident handling, supplier relationships, and data protection. These controls define what needs to be in place for a structured approach to information security. However, they are written at a high level, which means they tell you what is required but leave room for interpretation.

This is where ISO 27002 becomes useful.
ISO 27002 takes those same control areas and provides detailed guidance on how they can be implemented in practice. Instead of just stating that a control should exist, it explains how organizations typically design, apply, and manage that control over time.
A simple way to think about this is through an analogy.
ISO 27001 acts like a blueprint. It outlines what the structure should look like and what elements must be included. ISO 27002 works like an instruction manual, helping you understand how to build each part properly so that the overall system functions as expected.
This relationship becomes especially important during implementation. When teams rely only on high-level requirements, they often face uncertainty. They spend time deciding how detailed a control should be, what auditors might expect, or whether their approach is sufficient. This slows down progress and can lead to inconsistencies.
Using ISO 27002 as a reference helps reduce that uncertainty. It provides practical direction, which makes it easier to move from planning to execution without constantly second-guessing decisions.
At the same time, it is important to use it with balance. You are not expected to apply every recommendation exactly as written. The goal is to use it where clarity is needed, not to turn it into an additional layer of work.
The key insight is simple.
You don’t need ISO 27002. But skipping it often makes ISO 27001 harder.
Teams that use it selectively tend to implement controls more confidently and with fewer revisions, which ultimately makes the entire process more efficient.
Global adoption surge: ISO 27001 is now the fastest-growing certification type in the ISO ecosystem, projected to expand at a CAGR of 14.2% through 2032. The global ISO 27001 certification market was valued at $18.59 billion in 2025 and is expected to reach $74.56 billion by 2035.
Do You Need ISO 27002 for ISO 27001 Certification?
The short answer is no. You do not need ISO 27002 to get ISO 27001 certified. It is not a requirement, and auditors do not check whether you have followed ISO 27002.
The practical answer is more nuanced.
For most teams, ISO 27002 is almost always helpful, especially during implementation. While it is not required, it often makes the process clearer and more structured.
The difference becomes more obvious when you look at different types of organizations.

Small teams or startups
If you are a small team or a startup, you are likely working with:
- limited security expertise
- limited time
- pressure to move quickly
In this situation, the challenge is not knowing what needs to be done. The challenge is figuring out how to do it correctly without slowing everything down.
This is where ISO 27002 helps. It reduces guesswork by providing guidance on how controls can be implemented in real scenarios. Instead of spending time deciding what approach to take, you can follow a more structured path and move faster.
For smaller teams, this often means fewer mistakes and less rework during audits.
Mature organizations
For larger or more mature organizations, the situation is different.
They usually have:
- dedicated security teams
- existing policies and processes
- prior experience with compliance frameworks
In these cases, ISO 27002 may not be used as heavily. Teams already have internal standards and practices, so they rely less on external guidance.
However, even mature organizations use it as a reference when they need clarity or want to align their controls with widely accepted practices.
What this means in practice
You are not required to follow ISO 27002, but ignoring it completely can make implementation harder, especially if your team is still building its security processes.
The most effective approach is to use it where needed, not treat it as an additional requirement. This helps you stay focused on certification while still implementing controls in a practical and consistent way.
You can also give a quick read to ISO 27001 Password Policy: Requirements, Audit Traps & Best Practices
ISO 27001 vs 27002 Controls (Deep Dive)
To really understand the difference between ISO 27001 and ISO 27002, you need to look at how they handle controls, because that is where most of the implementation effort actually sits.
At the core of ISO 27001 is Annex A, which contains a set of security controls that organizations can apply to manage risks. These controls cover key areas such as access management, incident handling, logging, and supplier relationships. They define what needs to be in place, but they are intentionally written at a high level.
ISO 27002 works on the same set of controls but goes deeper. It expands on each control by explaining its purpose, how it should be designed, and how it can be implemented effectively in real scenarios.
Control Structure: High-Level vs Detailed
The difference is not in the controls themselves, but in how they are described.
- ISO 27001 focuses on requirements
- ISO 27002 focuses on implementation guidance
This means ISO 27001 defines what must exist, while ISO 27002 helps you understand how to make it work properly.

Annex A: The Common Foundation
Annex A is where both standards connect.
It contains a structured list of controls that organizations use as part of their security framework. These controls form the foundation of how risks are managed and security is maintained.
However, Annex A alone does not tell you:
- how detailed a control should be
- how to implement it in your environment
- what good implementation looks like
This is where ISO 27002 adds value. It builds on Annex A by providing clarity and practical direction, helping teams move from requirement to execution without guesswork.
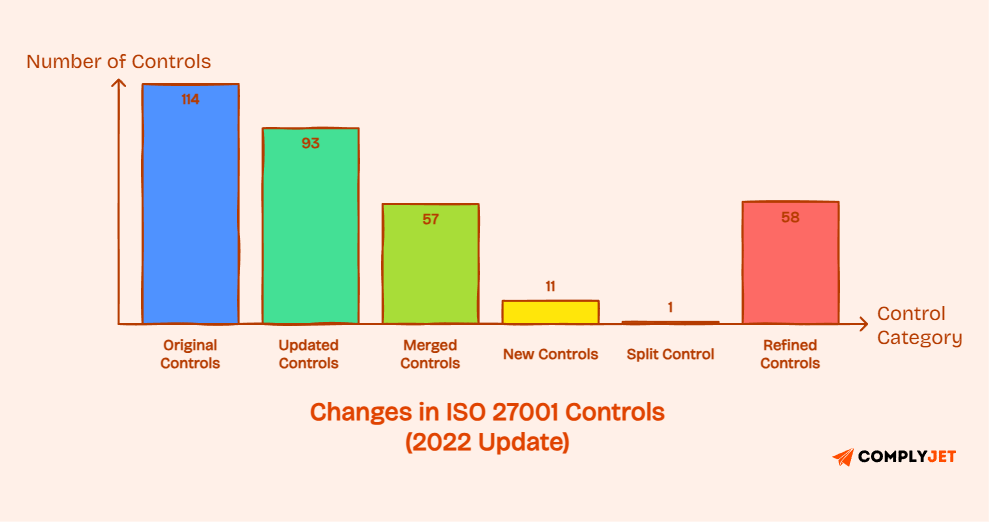
2022 Update: Simpler, More Practical
The 2022 revision made the control structure more streamlined.
- Controls reduced from 114 to 93
- Grouped into four categories:
- Organizational
- People
- Physical
- Technological
This new structure is easier to navigate and reflects modern security practices, especially in areas like cloud environments and remote access.
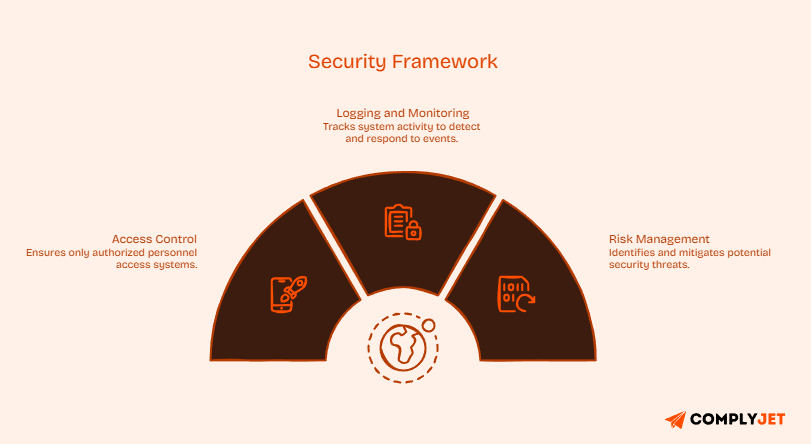
Example 1: Access Control
Access control is one of the most critical areas in any security setup.
At a requirement level, the goal is simple. Only the right people should have access to the right systems.
In practice, this involves:
- defining roles and responsibilities
- assigning permissions
- managing onboarding and offboarding
- reviewing access regularly
Without detailed guidance, teams often struggle to decide how strict or detailed these controls should be. This leads to either weak controls or unnecessary complexity.
Why it matters: According to the IBM Cost of a Data Breach Report 2024, stolen or compromised credentials were the most common initial attack vector, responsible for 16% of all breaches and these incidents took the longest to resolve, averaging nearly 10 months to identify and contain. Robust access control is not just a compliance checkbox. It directly reduces breach risk and recovery costs.
Example 2: Logging and Monitoring
Logging is another area where implementation matters more than theory.
Organizations are expected to track system activity so they can detect and respond to security events.
In practice, this includes:
- deciding what events to log
- storing logs securely
- reviewing logs regularly
- setting up alerts for unusual behavior
The challenge is finding the right balance. Too little logging creates risk. Too much logging creates noise and makes monitoring ineffective.
Example 3: Risk Management
Risk management is the foundation of all controls.
Organizations need to:
- identify risks
- assess their impact
- apply appropriate controls
- monitor and update over time
Without structure, this process becomes inconsistent. Different teams may assess risks differently, which leads to gaps in security.
Clear guidance helps standardize how risks are evaluated and treated, making decisions easier to justify during audits.
The cost of poor risk management: Organizations that extensively use AI and automation in their security operations save an average of $2.2 million per breach compared to those that don't, according to IBM's 2024 report. Two out of three organizations studied had deployed some form of AI and automation in their security operations center, a figure up 10% from 2023. Structured risk management, the kind ISO 27001 mandates, creates the operational foundation for those savings.
When Should You Use ISO 27001 vs ISO 27002?
Most teams ask this as a choice, but it’s not really a “one vs the other” decision. The better way to think about it is when to rely on each one during your compliance journey. They serve different purposes, and using them correctly depends on what stage you are in and what you are trying to achieve.
Use ISO 27001 when your goal is certification
If your primary goal is to become compliant and get certified, ISO 27001 is where your focus should be.
This usually happens when:
- you are working with enterprise clients who require proof of security
- security questionnaires are slowing down deals
- you need a recognized standard to build trust
In these scenarios, ISO 27001 gives you a clear path. It helps you build a structured system, define processes, and prepare for audits. Without it, there is no certification, and without certification, many opportunities remain out of reach.
For most SaaS companies, this is not optional. It becomes a business requirement.
Use ISO 27002 when you need clarity during implementation
Once you start working on ISO 27001, the next challenge is not understanding what needs to be done. The challenge is figuring out how to implement it properly.
This is where ISO 27002 becomes useful.
You use it when:
- you are unsure how detailed a control should be
- you need examples of how to apply a control
- your team is interpreting requirements differently
Instead of guessing or overthinking, ISO 27002 gives you direction. It helps you move forward without spending too much time deciding what approach is correct.

Scenario 1: Early-stage startup
If you are a small team starting from scratch, your priority should be speed and clarity.
In this case:
- ISO 27001 gives you the structure
- ISO 27002 helps you avoid mistakes
Without guidance, small teams often either under-implement controls or overcomplicate them. Using ISO 27002 selectively helps strike the right balance.
Scenario 2: Growing SaaS company
At this stage, you are likely dealing with:
- customer security reviews
- increasing data sensitivity
- pressure to scale quickly
Here, ISO 27001 becomes essential for credibility. At the same time, ISO 27002 helps ensure that controls are implemented in a consistent and scalable way.
The focus is not just certification, but doing it right without slowing down operations.
Industry adoption: By 2024, approximately 65% of IT service providers had obtained ISO 27001 certification to mitigate cyber risks.
For SaaS companies selling into enterprise markets, certification has shifted from a differentiator to a baseline requirement. Around 59% of IT and fintech firms now consider ISO 27001 essential for compliance and risk control.
Scenario 3: Mature organization
Larger organizations often already have:
- established security teams
- internal policies
- prior compliance experience
In these cases, ISO 27001 is still required for certification, but ISO 27002 may be used more selectively. Teams rely on their internal standards and refer to ISO 27002 when they need alignment or additional clarity.
What this means in practice
You do not need to treat ISO 27001 and ISO 27002 as separate tracks.
A more effective approach is:
- Focus on ISO 27001 as your main objective
- Use ISO 27002 as a support tool when needed
This keeps your process structured without adding unnecessary complexity.
The goal is not to use both equally. The goal is to use each one at the right time so you can move forward without confusion or delays.
For Startups & SaaS: What Actually Makes Sense
For startups and SaaS companies, compliance is rarely the top priority. It sits alongside product development, hiring, and growth, which means it has to be done without slowing everything else down. That creates a very specific challenge.
You are working with:
- limited time
- limited resources
- and often no dedicated security team
In this setup, the problem is not that compliance is too difficult. The real problem is that it feels unclear. Teams spend time trying to interpret requirements, second-guess decisions, and figure out what “good enough” looks like.
Most startups don’t fail compliance because it’s hard. They fail because it’s unclear.

What Usually Goes Wrong
Startups often fall into one of two extremes.
Some under-implement controls because they move too fast and skip important details. Others overcomplicate everything by trying to follow every recommendation perfectly, which slows them down.
Both approaches create problems. One increases risk, the other delays certification.
What Actually Works
A more practical approach is to separate priorities.
Your primary focus should be ISO 27001, because that is what leads to certification and unlocks business opportunities. Without it, you cannot demonstrate compliance to clients or move forward in enterprise deals.
At the same time, ISO 27002 should be treated as a support layer, not a requirement. You use it when you need clarity on how to implement a control, not as something you must follow in full detail.
This approach keeps your process simple. You stay focused on certification while still implementing controls in a way that is practical and consistent.
If you're a startup trying to get ISO 27001 done without slowing down your roadmap, ComplyJet helps you cut months off your compliance timeline by turning a complex process into a structured, trackable system.
Cost, Time & Resource Breakdown
When teams evaluate ISO 27001 and ISO 27002, cost and time are usually the biggest concerns. Not just the direct cost, but the effort required to get everything done properly without delays.

ISO 27001: Time and Cost Reality
For most organizations, ISO 27001 implementation takes anywhere between 3 to 12 months. The timeline depends on how prepared your organization is and how structured your approach is from the beginning.
The cost is not fixed. It varies based on several factors:
- Company size and complexity
Larger organizations with more systems and teams require more effort. - Existing security maturity
If you already have policies and controls in place, the process is faster and cheaper. - Internal vs external resources
Using consultants increases cost but can reduce time. Handling everything internally saves money, but often slows progress. - Tools and automation
Manual processes take longer and require more effort. Structured tools can reduce both time and operational overhead. - Audit and certification fees
These are mandatory costs paid to certification bodies.
What most teams underestimate is not the audit cost, but the internal effort required. Managing documentation, tracking controls, and preparing for audits takes consistent time across multiple teams.
ISO 27002: No Direct Cost, But Not “Free”
ISO 27002 does not have a certification cost because it is not a certifiable standard.
However, that does not mean it has no impact on cost.
The cost of ISO 27002 is indirect. It shows up in the form of:
- time spent understanding guidance
- effort required to interpret controls
- additional work if over-implemented
If used correctly, it can reduce mistakes and prevent rework, which saves time in the long run.
If overused, it can slow down implementation by adding unnecessary complexity.
What Changed with ISO 27001:2022 and ISO 27002:2022?
The 2022 update to the ISO 27000 series focused on making the standards easier to use, more aligned with modern security practices, and better suited for environments like cloud, DevOps, and distributed systems.
Instead of adding complexity, the update aimed to simplify how controls are structured and applied.
Fewer Controls, More Structured Approach
One of the biggest changes was the reduction in the number of controls.
- Controls were reduced from 114 to 93
- This was not a removal of requirements, but a restructuring:
- 57 controls were merged into 24
- 11 new controls were introduced
- 1 control was split into two
- 58 controls were refined for clarity
This makes the framework easier to navigate while still covering the same security areas.
New Controls Reflect Modern Security Needs
The update introduced 11 new controls to address current security challenges:
- Threat intelligence
- Information security for cloud services
- ICT readiness for business continuity
- Physical security monitoring
- Configuration management
- Information deletion
- Data masking
- Data leakage prevention
- Monitoring activities
- Web filtering
- Secure coding
These additions reflect how security has evolved, especially with increased reliance on cloud infrastructure and application-level security.
Simplified Control Structure
Previously, controls were grouped into 14 domains, which often felt fragmented.
The 2022 version reorganized them into four broader categories:
- Organizational controls (37 controls)
- People controls (8 controls)
- Physical controls (14 controls)
- Technological controls (34 controls)
This new structure makes it easier to understand how controls relate to each other and where they fit within an organization.
Introduction of Control Attributes
Another important update came with ISO 27002:2022, which introduced control attributes.
These attributes help classify controls in multiple ways, making them easier to manage and map to different frameworks.
Key attributes include:
- Control type (preventive, detective, corrective)
- Security property (confidentiality, integrity, availability)
- Cybersecurity function (identify, protect, detect, respond, recover)
- Operational capability
- Security domain
This allows teams to organize controls based on how they function, not just where they sit.
For teams, this means less time interpreting controls and more time implementing them effectively, especially in environments that rely on cloud services and continuous development.
Common Mistakes Teams Make
Most teams don’t struggle because ISO 27001 is too complex. They struggle because they approach it the wrong way. A few common mistakes show up consistently, especially for teams going through compliance for the first time.
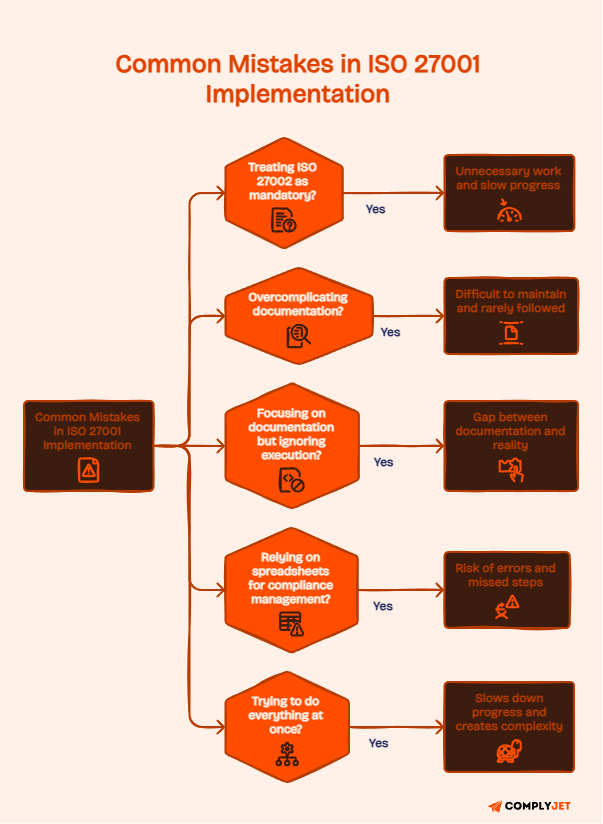
Key Mistakes to Avoid
- Treating ISO 27002 as mandatory: Many teams assume they need to fully implement ISO 27002 because it appears alongside ISO 27001. This leads to unnecessary work and slows down progress. In reality, it is a guideline meant to support implementation, not a requirement.
- Overcomplicating documentation: Teams often try to create overly detailed policies that cover every possible scenario. This results in documents that are difficult to maintain and rarely followed in practice. Auditors look for clarity and consistency, not excessive detail.
- Focusing on documentation but ignoring execution: Writing policies without actually implementing them creates a gap between what is documented and what is happening in reality. This becomes a major issue during audits and often leads to delays.
- Relying on spreadsheets for compliance management: Spreadsheets may seem simple at first, but they quickly become hard to manage as the process grows. Tracking controls, evidence, and progress across multiple files increases the risk of errors and missed steps.
- Trying to do everything at once: Some teams attempt to implement all controls in full detail from the beginning. This slows down progress and creates unnecessary complexity instead of focusing on what is needed for certification.
These mistakes may seem small at first, but they compound over time and make compliance slower, more stressful, and harder to manage.
If you’re manually managing compliance in spreadsheets, you’re not saving money you’re adding risk.
ComplyJet helps you avoid these mistakes from day one by giving you a structured system to manage controls, documentation, and audit readiness in one place.
Step-by-Step: Implement ISO 27001 Using ISO 27002
Getting ISO 27001 certified is not about doing everything at once. It is about following a clear sequence and making sure each step is handled properly before moving forward. Using ISO 27002 during implementation helps reduce confusion and gives you practical direction where requirements feel unclear.

1. Define the Scope
The first step is to clearly define the scope of your ISMS. This means deciding which parts of your business, systems, and data will be covered under certification. A well-defined scope keeps the process focused and manageable, especially for startups.
In practice, you should identify the products, services, or systems that handle sensitive data and set clear boundaries around them. Avoid making the scope too broad in the beginning, as this increases effort and slows down progress.
At the same time, do not exclude critical systems just to reduce workload, because that can create gaps during audits. The goal is to keep the scope realistic and aligned with your business priorities.
2. Conduct a Risk Assessment
Risk assessment is the foundation of the entire process. You need to understand what could go wrong, how likely it is, and what impact it would have on your organization.
To do this effectively, start by identifying key assets such as data, systems, and processes. Then evaluate potential threats and vulnerabilities associated with them. While doing this, focus on clarity rather than building complex scoring models.
Many teams make the mistake of overengineering risk frameworks, which slows things down without adding real value. At the same time, avoid treating risk assessment as a formality. It should reflect real risks your business faces, not just generic scenarios.
3. Map Controls
Once risks are identified, the next step is to map appropriate controls. This is where you decide how each risk will be managed.
In practice, this means reviewing relevant control areas and selecting only those that address your identified risks. It is important to document why a control is selected or not selected, as this becomes part of your audit evidence.
A common mistake here is treating controls like a checklist and selecting everything without justification. On the other hand, skipping documentation can create problems later when auditors expect clear reasoning behind your decisions. Control mapping should always be risk-driven and well-documented.
4. Use ISO 27002 for Execution
This is where most teams face challenges. You know what controls to implement, but not how to implement them correctly.
ISO 27002 helps by providing practical guidance. You can use it to understand how controls are typically applied and what a good implementation looks like. The key is to use it as a reference, not as a strict rulebook. Following every recommendation blindly can slow you down and add unnecessary complexity.
At the same time, ignoring it completely often leads to guesswork and inconsistent implementation. The right approach is to use ISO 27002, where you need clarity and adapt it to your organization’s size and needs.
5. Documentation
Documentation is required, but it should support your processes, not replace them.
You should create policies and procedures that reflect how your organization actually operates. Clear and concise documentation is easier to maintain and more useful during audits. Many teams make the mistake of over-documenting, creating long policies that are rarely followed in practice.
This creates a gap between what is written and what is done. On the other hand, poor or missing documentation makes it difficult to demonstrate compliance. The balance lies in keeping documentation practical, relevant, and aligned with real operations.
6. Internal Audit
Before moving to certification, you need to validate your system internally. This step helps identify gaps and fix issues early.
An effective internal audit involves reviewing controls, checking whether processes are being followed, and verifying that documentation matches actual practices. It should be treated as a genuine evaluation, not just a formality. Ignoring issues identified during this stage is a common mistake and often leads to problems during the external audit.
Addressing gaps early makes the final audit smoother and reduces the risk of delays.
7. Certification Audit
The final step is the external audit, where your ISMS is reviewed by a certification body.
Preparation here is critical. You need to ensure that all controls are implemented, documentation is complete, and evidence is readily available. Teams should also be aware of their roles and responsibilities during the audit process.
A common mistake is rushing into this stage without proper preparation, which leads to unnecessary findings and rework. Certification is not achieved through last-minute effort, but through consistent work across all previous steps.
For better understanding, refer to ISO 27001 Certification Process (2026): Step-by-Step Guide
Tools That Simplify ISO Compliance
For most teams, the challenge with ISO 27001 is not understanding the requirements but managing everything together. When done manually, compliance quickly becomes messy, slow, and inconsistent.
Teams often rely on spreadsheets and documents to track controls, policies, and evidence. This works in the beginning, but as complexity increases, it becomes difficult to keep everything updated and aligned. Important steps get missed, visibility drops, and audit preparation takes longer than expected.
Automation solves this by bringing everything into a structured system.
Instead of juggling multiple tools, you get a centralized workflow where controls, documentation, and progress are tracked in one place. This reduces manual effort and helps teams stay consistent throughout the process.
ComplyJet is built to simplify this.
It offers centralized compliance management, makes control mapping clearer, and ensures audit readiness without last-minute effort. This allows teams to focus on implementation instead of coordination.
Want to see how ISO 27001 can be implemented without spreadsheets, chaos, or delays?
Book a demo with ComplyJet and get a clear compliance roadmap.
FAQs
What is the main difference between ISO 27001 and ISO 27002?
The main difference comes down to purpose. ISO 27001 is a standard used to build and certify an information security management system. It defines what needs to be in place for an organization to manage security risks effectively. ISO 27002, on the other hand, is a guideline that provides detailed recommendations on how to implement security controls in practice.
In simple terms, ISO 27001 focuses on structure and compliance, while ISO 27002 focuses on execution and clarity.
Can you get certified in ISO 27002?
No, ISO 27002 is not a certifiable standard. Organizations cannot get audited or certified against it. Certification applies only to ISO 27001.
ISO 27002 is meant to support implementation, not to act as a separate compliance requirement.
How are controls different in ISO 27001 and ISO 27002?
Both refer to the same control areas, but the level of detail is different.
ISO 27001 defines controls at a high level, outlining what needs to be addressed. ISO 27002 expands on those controls by explaining how they can be implemented, managed, and maintained in real-world scenarios.
This difference is why ISO 27002 is often used during implementation, even though it is not required.
Do you need ISO 27002 for ISO 27001 certification?
No, it is not mandatory. However, many teams find it useful during implementation because it reduces guesswork and helps ensure controls are applied correctly.
Using it selectively can make the process smoother, especially for teams without deep security expertise.
When should you use ISO 27002?
ISO 27002 is most useful when you need clarity on how to implement a control. If your team is unsure about the level of detail required or how to structure a process, it acts as a helpful reference.
It is not something you need to follow fully, but something you use when needed.
Final Section — What Should You Do Next?
By now, the difference between ISO 27001 and ISO 27002 should be clear.
ISO 27001 is what enables certification. It provides the structure you need to build a system that can be audited and trusted. Without it, you cannot demonstrate compliance.

ISO 27002 is optional, but it plays an important role during implementation. It helps you apply controls more effectively and reduces uncertainty when decisions are not obvious.
The key is to use both in the right way.
Focus on ISO 27001 as your primary goal. Use ISO 27002 as a support layer when you need clarity. This approach keeps your process efficient without adding unnecessary complexity.
The biggest advantage comes from staying structured. When you reduce confusion and follow a clear path, compliance becomes faster and more manageable.
ISO 27001 helps you prove security.
ISO 27002 helps you build it right.
If you're serious about getting ISO 27001 certified without wasting months figuring things out,
ComplyJet gives you the fastest, most structured path to compliance.



