Organizations today are no longer getting fined under GDPR because of missing privacy policies alone. They’re getting penalized for weak cybersecurity controls, insecure AI systems, poor breach response processes, unlawful data transfers, and failure to protect personal data at scale.
And regulators are escalating enforcement fast.
As of early 2026, cumulative GDPR fines have crossed €7.1 billion, while breach notifications across Europe continue to rise year over year. At the same time, the EU AI Act is introducing another layer of scrutiny for organizations using AI in hiring, analytics, fraud detection, monitoring, and automated decision-making systems, with penalties reaching up to €35 million or 7% of global annual turnover for serious violations.
This is why GDPR can no longer be treated as just a legal or privacy framework.
Modern organizations now need to prove they can:
- Detect breaches quickly,
- Secure personal data across cloud environments,
- Govern AI systems responsibly,
- Manage third-party risk,
and continuously validate security controls under a risk-based compliance model.
That overlap between cybersecurity, privacy, and AI governance is exactly where many organizations struggle today.
In this guide, we have discussed what GDPR actually requires from a cybersecurity perspective, the technical controls regulators expect to see, how GDPR overlaps with frameworks like ISO 27001 and NIST CSF, and what organizations should do now to prepare for increasing AI-related compliance obligations under both GDPR and the EU AI Act.
Struggling to align cybersecurity, privacy, and AI governance under one compliance strategy? Our compliance experts help organizations simplify GDPR, ISO 27001, SOC 2, and EU AI Act readiness with practical implementation support.
Let’s start by understanding the fundamentals of GDPR in cybersecurity and how various regulations map to the IT infrastructure within your organization.
Why Does GDPR Matter for Cybersecurity?
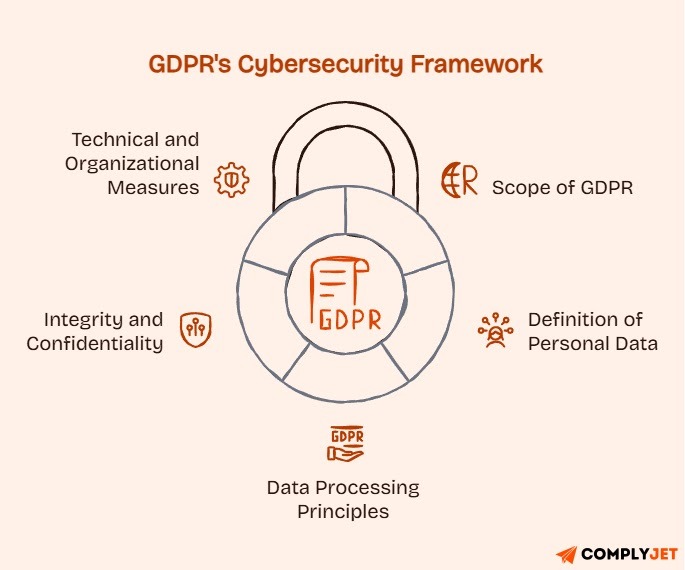
The General Data Protection Regulation (GDPR) came into force on May 25, 2018, reshaping how organizations worldwide approach personal data protection. It applies to any organization that processes the personal data of individuals in the European Union (EU) or European Economic Area (EEA), regardless of where the business operates.
That means GDPR can apply equally to companies in:
- New York
- Oslo
- Sydney
- or anywhere else handling EU resident data
Under GDPR, personal data includes any information that can directly or indirectly identify an individual, including:
- Names
- Email addresses
- IP addresses
- Location data
- Cookie identifiers
- Biometric information
Because of this broad definition, most customer-facing systems, SaaS platforms, marketing tools, and IT environments process GDPR-regulated data in some form.
At the center of GDPR are six data processing principles defined in Article 5. For cybersecurity teams, the most important principle is the principle of integrity and confidentiality under Article 5(1)(f), which requires organizations to protect personal data against:
- Unauthorized access
- Unlawful processing
- Accidental loss
- Destruction
- Damage
The regulation specifically requires organizations to implement “appropriate technical and organizational measures” to secure data. This is what transforms GDPR from a privacy regulation into a cybersecurity compliance obligation.
What Is GDPR in Cybersecurity?
GDPR in cybersecurity refers to the regulation’s mandatory security requirements for protecting personal data throughout its lifecycle. Unlike industry-specific frameworks, GDPR cybersecurity obligations apply across sectors and organization sizes whenever EU personal data is involved.
In practice, GDPR requires organizations to implement controls such as:
- encryption
- access management
- breach detection
- incident response procedures
- data protection governance
These are not optional best practices. They are enforceable compliance requirements backed by penalties of up to €20 million or 4% of global annual turnover.
Who Must Comply? The Global Reach of GDPR

GDPR has a broad extraterritorial reach. If your organization processes the personal data of individuals in the European Union (EU), the regulation can apply, regardless of where your business is located.
That means GDPR may apply to:
- A SaaS company in India
- A fintech startup in Canada
- An e-commerce brand in the United States
- or any organization serving or tracking EU residents
In practical terms, geography does not exempt organizations from GDPR obligations.
Controllers vs. Processors
GDPR separates organizations into two primary roles:
For example:
- A company storing customer data decides the purpose of processing and acts as the controller
- A cloud hosting provider, such as AWS, operates as the processor
Both parties have GDPR cybersecurity responsibilities, although controllers retain primary accountability for compliance and lawful processing.
Why Many Organizations Apply GDPR Standards Globally
Many businesses no longer maintain separate privacy standards for EU and non-EU operations. Instead, they apply GDPR-level controls organization-wide to simplify governance, reduce operational complexity, and prepare for evolving global privacy laws.
This approach has become increasingly common as countries such as:
- Brazil (LGPD)
- India (DPDA Act)
- the United Kingdom (UK GDPR)
- and several U.S. states (CCPA, VCDPA, CPA, CTDPA, and others)
introduce privacy frameworks influenced by GDPR principles.
For multinational organizations, adopting a unified GDPR cybersecurity framework often proves more scalable than managing fragmented regional controls.
Which Countries Does GDPR Apply To?
GDPR protects the personal data of users across:
- All 27 EU member states
- 3 members under the European Economic Area (Iceland, Liechtenstein, Norway)
The United Kingdom also maintains a separate but closely aligned UK GDPR framework post-Brexit.
The extraterritorial scope of GDPR extends well beyond what most organizations interpret. And it has been the single biggest reason for heavy penalties for organizations across the globe. Therefore, it is advised to understand deeply the GDPR countries, adequacy regions, and international applicability rules, which we have discussed in detail in our GDPR countries list guide.
What GDPR Requires from Your Cybersecurity Program: Action Steps for Businesses
The GDPR contains a total of around 99 articles. But security teams don't need to master the entire regulation. The following are the five articles that cybersecurity teams need to know to calculate the direct obligation of GDPR:
- Article 5(1)(f): Integrity and Confidentiality Principle
- Article 25: Privacy by Design and by Default
- Article 32: Security of Processing
- Article 33: Breach Notification to Supervisory Authority
- Article 35: Data Protection Impact Assessments (DPIAs)
Understanding the articles is necessary but insufficient. Security teams need to translate regulatory text into operational requirements.
Below, we have discussed the practical implications of the articles that were discussed in the previous section and what exactly GDPR mandates to regulate against these foundational articles.
Data Protection by Design and by Default (Article 25)

Article 25 introduced the concept of data protection by design and by default, requiring organizations to embed privacy and security controls into systems from the beginning — not after deployment or during compliance audits.
In practice, this means security and privacy considerations must be integrated throughout the development lifecycle:
- during requirements gathering
- in system architecture decisions
- throughout development and testing
- and in the default user configurations
For example:
- Collect only the data necessary for a specific purpose
- Cisable unnecessary third-party sharing by default
- Require opt-in for marketing communications
- Configure social or profile settings as private by default
- Evaluate pseudonymization and data masking during design stages
This shifts responsibility away from users manually protecting their privacy and places accountability on organizations to build secure defaults into products and systems.
How does this apply? A widely cited enforcement example to consider is that of Instagram. It was fined €405 million by Ireland’s Data Protection Commission in 2022 after children's accounts were set to public by default, which is a direct Article 25 violation.
Security of Processing (Article 32)
Article 32 forms the technical core of GDPR cybersecurity requirements. It requires organizations to implement “appropriate technical and organizational measures” based on the sensitivity of data, processing activities, and overall risk exposure.
Rather than prescribing identical controls for every organization, GDPR follows a risk-based approach. A startup handling business contact data faces different expectations than a healthcare platform processing medical records at scale.
Key GDPR Security Requirements Under Article 32
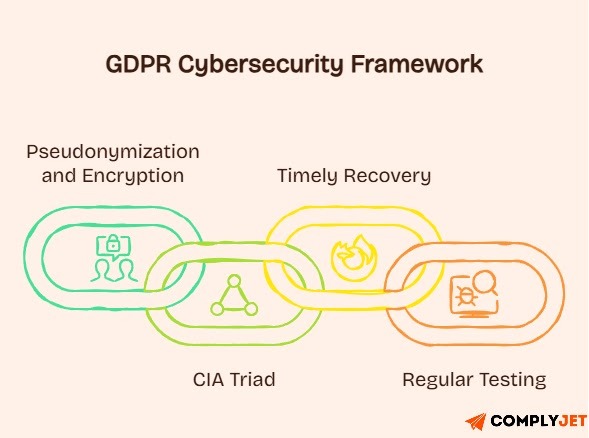
1. Pseudonymization and Encryption
GDPR strongly emphasizes:
- data encryption
- pseudonymization
- secure key management
Pseudonymization replaces identifiable information with artificial identifiers, while encryption makes data unreadable without decryption keys.
These controls significantly reduce breach impact and may influence regulatory penalties or notification obligations if exposed data remains unintelligible to attackers.
2. Confidentiality, Integrity, Availability, and Resilience
Article 32 aligns closely with the CIA triad familiar to cybersecurity teams:
- Confidentiality through access controls and authentication
- Integrity through logging, monitoring, and change management
- Availability through backups and redundancy
- Resilience through disaster recovery and business continuity planning
This is where GDPR and cybersecurity frameworks heavily overlap operationally.
3. Timely Recovery After Incidents
Organizations must restore data availability and access quickly following technical or physical incidents.
This requires:
- Tested backups
- Documented recovery procedures
- Recovery time objectives (RTOs)
- Incident recovery workflows
Unverified backup strategies are not sufficient from a GDPR compliance perspective.
4. Regular Testing and Evaluation
Security controls must be continuously assessed through:
- penetration testing
- vulnerability assessments
- security audits
- control effectiveness reviews
Businesses shall note that GDPR does not recognize static “point-in-time” compliance. Organizations must demonstrate ongoing validation as threats evolve.
The Risk-Based Compliance Model
GDPR does not require every organization to implement enterprise-grade controls uniformly. Instead, organizations must demonstrate that security investments are proportionate to:
- Processing risks
- Data sensitivity
- Attack exposure
- Potential impact on individuals
However, regulators expect documented risk assessments supporting those decisions.
Having security controls is not enough if you cannot prove them during audits or investigations. Complyjet help organizations map technical safeguards to GDPR Article 32, ISO 27001, and SOC 2 requirements.
Data Breach Notification (Articles 33 & 34)

GDPR’s breach notification rules (Articles 33 & 34) are among its most operationally demanding cybersecurity obligations.
When a personal data breach occurs, organizations must notify the relevant supervisory authority within 72 hours of becoming aware of the incident.
Under GDPR, a personal data breach includes:
- Unauthorized access
- Unlawful disclosure
- Accidental loss
- Destruction
- Alteration
- Exposure of personal data
Importantly, “awareness” does not mean completing a full forensic investigation. It means having sufficient evidence to reasonably conclude that personal data has been compromised.
What Breach Notifications Must Include
Organizations must provide:
- The nature of the breach
- Affected data categories
- Approximate number of impacted individuals
- Likely consequences
- Mitigation measures taken
- DPO or contact information
If all details are unavailable within 72 hours, organizations can submit phased updates as investigations continue.
When Individuals Must Be Notified
Article 34 requires organizations to notify affected individuals when the breach is likely to create a high risk to their rights and freedoms, particularly involving:
- financial information
- government identifiers
- authentication credentials
- health data
- or sensitive personal information
Notification may not be required if:
- The data was strongly encrypted
- The risk was fully mitigated afterward
- Or direct communication would require disproportionate effort
Why Detection Capabilities Matter
The 72-hour requirement effectively turns incident detection into a GDPR cybersecurity compliance issue.
Organizations cannot comply if breaches remain undetected for weeks. As a result, technologies such as:
- SIEM platforms
- Endpoint detection and response (EDR)
- Data loss prevention (DLP)
- Centralized logging
- And incident response tooling
become operational compliance requirements rather than optional security investments.
Data Protection Impact Assessments (DPIAs): Article 35

A Data Protection Impact Assessment (DPIA) is a structured risk assessment required when processing activities are likely to create high risk for individuals’ rights and freedoms.
GDPR specifically requires DPIAs for activities such as:
- large-scale processing of sensitive data
- extensive profiling or automated decision-making
- systematic public monitoring
- processing involving vulnerable individuals or high-risk technologies
What a DPIA Includes
A GDPR DPIA typically covers:
- The processing activity and its purpose
- Necessity and proportionality assessment
- Risks to individuals
- Mitigation measures and compliance controls
Why DPIAs Matter for Cybersecurity Teams
For cybersecurity and compliance teams, DPIAs closely align with:
- Threat modeling
- Privacy risk assessments
- Security architecture reviews
- Vendor risk analysis
Organizations that integrate DPIAs into their secure development lifecycle (SDLC) reduce duplicated compliance efforts while ensuring security controls directly support GDPR compliance objectives.
How Security Teams Implement GDPR Cybersecurity Protocols in Real Environments
Translating GDPR requirements into technical implementation means understanding which security controls actually reduce compliance risk.
Let’s break down the core security measures that actually support GDPR cybersecurity compliance in practice.
Encryption
GDPR strongly incentivizes encryption, even though it doesn’t universally mandate it. If breached data is encrypted and unintelligible to unauthorized parties, organizations may avoid notification obligations, and regulators often consider encryption when determining penalties.
Encryption at rest should protect databases, cloud storage, and systems containing personal data, especially sensitive categories like health records, financial data, or credentials. Modern platforms make this easier, but secure key management remains critical.
Encryption in transit protects data moving between applications, APIs, and users. TLS 1.2 or higher should secure all personal data transmissions, while outdated protocols like SSL 3.0 or TLS 1.0 should be eliminated.
The goal is not perfect encryption, but risk-appropriate encryption. Standards like AES-256 and RSA-2048 remain reasonable choices for most environments.
Pseudonymization and Data Masking
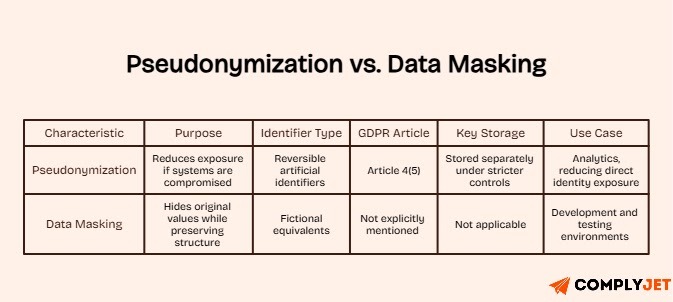
Pseudonymization replaces direct identifiers with reversible artificial identifiers, reducing exposure if systems are compromised. For example, customer names can be replaced with random IDs while the mapping key is stored separately under stricter controls.
Under GDPR Article 4(5), pseudonymization only works if the additional identifying information is stored separately and protected with technical and organizational safeguards. Keeping the mapping key alongside the dataset defeats the purpose.
Data masking hides original values while preserving structure and usability. Organizations commonly mask production databases before using them in development or testing environments by replacing names, emails, and account numbers with fictional equivalents.
These controls are especially valuable for analytics, where teams can analyze trends and behavior patterns without directly exposing identities.
Access Controls and Identity Management
The principle of least privilege aligns directly with GDPR’s data minimization and security requirements. Employees should access only the personal data necessary for their roles.
Role-based access control (RBAC) helps enforce this systematically by assigning permissions based on job function instead of individual users. This simplifies onboarding, role changes, and permission revocation.
Multi-factor authentication (MFA) is essential for privileged accounts, remote access, and systems processing sensitive personal data. Passwords alone are no longer sufficient against phishing and credential-stuffing attacks.
Regular access reviews are equally important. Quarterly audits help identify excessive permissions, inactive accounts, and users who retained access after role changes or departures.
Endpoint Protection and DLP
Endpoint security protects personal data on employee devices, where exposure risk is often highest. Modern endpoint detection and response (EDR) platforms support GDPR requirements through behavioral monitoring, threat detection, and automated response capabilities.
Data Loss Prevention (DLP) tools monitor and restrict unauthorized movement of personal data. Properly configured DLP controls can block customer lists from being emailed externally, copied to USB devices, or exfiltrated through suspicious activity.
DLP also supports breach detection obligations under Article 33 by helping organizations identify abnormal access or transfer patterns that may indicate compromise.
However, effectiveness depends heavily on configuration.
Hence, accurate data classification, balanced policies, and continuous tuning are necessary to reduce false positives without weakening detection.
Email Security
Email remains one of the most common sources of personal data exposure. Phishing attacks compromise credentials, employees send data to incorrect recipients, and archived mailboxes often contain years of sensitive information.
Encrypting outbound emails containing personal data reduces risk during transmission and storage. TLS secures server-to-server communication, while S/MIME or PGP provides message-level encryption for sensitive communications.
Email security gateways add additional protection through spam filtering, phishing detection, malware scanning, and DLP enforcement for outbound messages.
Email archives also require attention. Long-term archives often become high-value targets because they store large volumes of historical personal data. Organizations should restrict archive access, encrypt stored messages, and apply retention policies that delete emails once legal and business requirements expire.
Mapping GDPR to Other Cybersecurity Frameworks
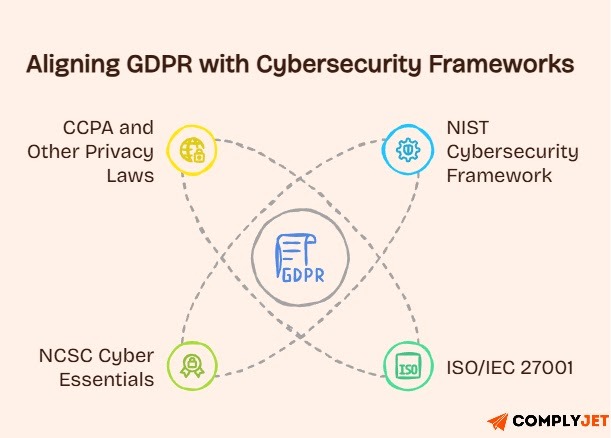
Organizations already using established security frameworks often have much of the groundwork needed for GDPR compliance. Instead of treating GDPR separately, the better approach is to map its requirements to existing controls. So, here’s how GDPR maps to other respective frameworks, with several points common for each framework.
NIST Cybersecurity Framework
The NIST CSF’s core functions: Identify, Protect, Detect, Respond, and Recover, align closely with GDPR requirements.
- Identify supports data discovery, classification, Article 30 records, and DPIAs.
- Protect covers encryption, access controls, pseudonymization, and staff security training under Article 32.
- Detect helps organizations identify breaches quickly enough to meet the 72-hour notification requirement.
- Respond aligns with breach response and notification obligations under Articles 33 and 34.
- Recover supports GDPR’s requirement to restore data availability after incidents.
Organizations operating at mature NIST CSF levels usually already have many required technical controls in place. The remaining gaps are often documentation, governance, and privacy procedures.
ISO/IEC 27001
ISO 27001 is widely viewed as strong evidence of “appropriate technical and organisational measures” under GDPR. Its risk-based approach closely matches GDPR’s security expectations.
Annex A controls map directly to GDPR areas like access control, encryption, incident management, and business continuity. ISO 27002 further provides implementation guidance for these controls.
Organizations pursuing ISO 27001 should explicitly include GDPR requirements within their ISMS scope so policies, audits, and controls support both frameworks.
NCSC Cyber Essentials
For UK organizations, the NCSC’s Cyber Essentials framework provides a practical security baseline through controls like secure configuration, access control, malware protection, patching, and firewalls.
While Cyber Essentials alone does not guarantee GDPR compliance, it supports Article 32 by establishing minimum security hygiene. The NCSC’s broader “10 Steps to Cyber Security” guidance adds more advanced practices around risk management, monitoring, and incident response.
CCPA and Other Privacy Laws
CCPA takes a different approach from GDPR, relying more on consumer opt-out rights than GDPR’s consent-first model. However, organizations meeting GDPR standards will usually satisfy much of CCPA’s technical and governance requirements as well.
The same applies to newer privacy laws like Brazil’s LGPD, India’s DPDP Act, and several U.S. state privacy laws. Building security and privacy programs around GDPR creates a strong foundation for broader multi-jurisdictional compliance.
GDPR, AI, and the Future of Cybersecurity Compliance
Artificial intelligence adds new GDPR challenges that security teams now need to manage proactively.

What Changes When AI Starts Processing Personal Data?
Using personal data to train AI models falls fully under GDPR. Organizations must establish a legal basis, minimize collected data, secure training datasets, and conduct DPIAs when processing creates high risk.
Training data creates additional exposure because AI models can unintentionally memorize and reproduce personal information. To reduce this risk, organizations should use anonymization or pseudonymization where possible, apply privacy-preserving techniques like differential privacy, and maintain clear data lineage showing which datasets were used in each model.
Why Does GDPR Article 22 Matter for AI Systems?
GDPR Article 22 gives individuals rights when automated systems make decisions with significant effects, such as hiring, credit approvals, or insurance pricing.
Organizations using AI for these decisions must explain the logic involved, describe the impact of processing, and provide safeguards like human review options. This creates strong requirements around explainability, audit trails, logging, and oversight.
As a result, purely black-box AI systems can create compliance challenges, especially in high-impact use cases.
How Does the EU AI Act Connect With GDPR?
The EU AI Act adds another compliance layer for organizations deploying AI systems in the EU. While GDPR focuses on personal data protection, the AI Act regulates broader AI risks through a risk-based model.
High-risk systems used in areas like employment, credit scoring, law enforcement, or critical infrastructure face strict obligations, including risk assessments, governance controls, technical documentation, and conformity reviews.
These requirements overlap heavily with GDPR. For example, high-risk AI systems processing personal data may require both a GDPR DPIA and an AI Act Fundamental Rights Impact Assessment.
The AI Act also introduces massive penalties, reaching up to €35 million or 7% of global turnover for severe violations.
For security teams, this means AI governance is no longer just a technical issue. AI-powered monitoring, fraud detection, behavioral analytics, and hiring systems can all trigger GDPR and AI Act obligations simultaneously.
However, organizations that already follow GDPR principles like privacy by design, data governance, and risk-based security are generally better positioned for AI Act compliance.
AI systems can trigger both GDPR and EU AI Act obligations simultaneously. If your organization uses AI for analytics, monitoring, hiring, or fraud detection, we can help assess compliance risks before regulators do.
What Happens If You Don’t Comply? Here are Real-World GDPR Penalties

GDPR uses a two-tier penalty structure designed to be effective and financially significant.
- Tier 1 violations can reach €10 million or 2% of global annual turnover.
- Tier 2 violations, covering core privacy principles and unlawful processing, can reach €20 million or 4% of global turnover.
Regulators consider factors like the severity of the violation, duration, negligence, mitigation efforts, prior violations, cooperation, and the sensitivity of affected data.
What Do Real GDPR Enforcement Actions Usually Look Like?
- Meta received a €1.2 billion fine for unlawful EU-US data transfers.
- LinkedIn was fined €310 million over behavioral advertising without a proper legal basis.
- Uber faced a €290 million penalty tied to improper international data transfers.
- TikTok received a €345 million fine related to children’s privacy protections and default settings.
Most major penalties stem from weak security controls, unlawful data transfers, or processing without valid legal grounds, not minor paperwork failures. To avoid these significant penalties, organizations should implement robust GDPR compliance software and monitoring systems.
Why Are GDPR Penalties More Than Just Financial Risk?
Beyond fines, organizations also face reputational damage, customer trust loss, increased regulatory scrutiny, and, in some cases, restrictions on processing activities that directly disrupt operations.
GDPR Cybersecurity Compliance Checklist
Now that you know the articles that build the GDPR cybersecurity framework, and how organizations apply these regulations within their IT infrastructure.
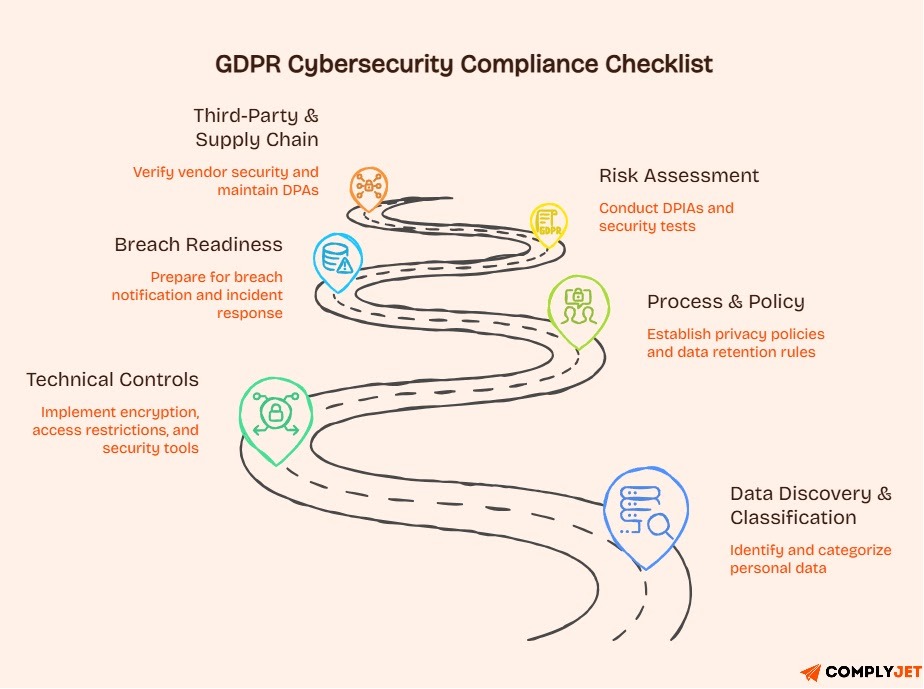
Here’s a detailed checklist that you can use to check the current status of your cybersecurity readiness.
This checklist provides a practical framework for verifying compliance.
Data Discovery & Classification
- Do you know where all personal data exists? Conduct a data inventory identifying what personal data your organization collects, processes, stores, and shares
- Can you clearly trace how personal data moves? Understand how personal data moves between systems, third parties, and jurisdictions
- Have you categorized data based on sensitivity? Categorize personal data by risk level (standard, sensitive, special category)
- Is every processing activity tied to a clear purpose? Document the specific business purpose for each category of personal data
- Are your processing activities properly documented? Implement Article 30 registers documenting processing operations
Technical Controls
- Is personal data encrypted while stored? Deploy encryption for databases, file stores, and backups containing personal data
- Is personal data encrypted during transmission? Enforce TLS 1.2+ for all connections transmitting personal information
- Can you reduce exposure through pseudonymization? Evaluate opportunities to pseudonymize datasets while preserving
- Are access permissions restricted by role? Implement role-based access and the principle of least privilege
- Is MFA enabled for sensitive systems and admin access? Require MFA for administrative access and systems processing sensitive personal information
- Are DLP and endpoint security controls in place? Deploy data loss prevention tools and endpoint security
- Can you detect suspicious activity quickly? Establish SIEM or equivalent capabilities to detect security incidents
Process & Policy
- Is privacy built into your development process? Establish procedures integrating privacy and security into the development lifecycle
- Have you assigned ownership for data protection? Appoint DPO if required; designate privacy owner if not
- Are your privacy policies fully documented and current? Document how personal data is collected, used, stored, and protected
- Do you have clear data retention rules? Define how long different categories of personal data are kept and when they're deleted
- Are your Article 30 records regularly maintained? Keep current Article 30 documentation
Breach Readiness
- Could you notify regulators within 72 hours? Document procedures enabling supervisory authority notification within the deadline
- Do you know how to assess whether a breach is reportable? Define how to evaluate whether breaches trigger notification requirements
- Are breach notification templates already prepared? Prepare breach notification drafts, accelerating response
- Have you tested your incident response process recently? Test breach response procedures regularly, ideally quarterly
- Does everyone know their role during a breach? Assign clear roles and responsibilities for breach management
Risk Assessment
- Are DPIAs conducted for high-risk processing activities? Conduct Data Protection Impact Assessments for processing likely to result in high risk
- Are security controls tested regularly? Test security controls quarterly or after significant changes
- Have systems handling personal data been penetration tested? Conduct annual penetration tests of systems processing personal data
- Are risk assessments reviewed as threats evolve? Reevaluate risks as business operations and threat landscape evolve
Third-Party & Supply Chain
- Have you verified vendor security practices? Verify that vendors processing personal data on your behalf implement adequate security
- Are Data Processing Agreements signed and maintained? Maintain Article 28 contracts with all processors
- Do you know which subprocessors handle your data? Understand which subprocessors handle your data and under what safeguards
- Have processor security controls been reviewed? Obtain SOC 2 reports, ISO 27001 certificates, or conduct security assessments
- Is vendor risk management an ongoing process? Regularly reassess third-party security posture
The 10-Point GDPR Compliance Action Plan
GDPR compliance now requires continuous security validation, governance, and breach readiness. Talk to our compliance experts to identify gaps across your cybersecurity and privacy program.
Frequently Asked Questions
What is GDPR in cybersecurity?
GDPR is the EU regulation that makes protecting personal data a legal cybersecurity requirement, not just a privacy best practice. It requires organizations to implement security controls like encryption, access management, breach detection, and incident response to protect personal data from unauthorized access, loss, or disclosure. Violations can result in fines of up to €20 million or 4% of global annual turnover.
What does GDPR stand for in cybersecurity?
GDPR stands for General Data Protection Regulation. In cybersecurity, it refers to the EU framework that requires organizations to secure personal data through risk-based technical and organizational controls such as encryption, pseudonymization, monitoring, and access restrictions.
What are the main GDPR IT security requirements?
GDPR mainly requires organizations to implement risk-based security controls under Article 32. This includes encryption, access controls, system resilience, security testing, breach detection, backup and recovery capabilities, and the ability to notify regulators within 72 hours of a reportable breach. It also requires Privacy by Design under Article 25.
How do I comply with GDPR as a cybersecurity professional?
Start by identifying where personal data exists and how it flows across systems. Then implement core controls like encryption, least-privilege access, MFA, logging, monitoring, and incident response procedures. GDPR compliance also requires documenting security measures, conducting risk assessments, and ensuring breach response processes can meet the 72-hour reporting requirement.
What does GDPR have to do with cybersecurity?
GDPR directly ties cybersecurity to legal compliance. Articles 5 and 32 require organizations to protect personal data using appropriate technical and organizational security measures, while Article 33 mandates breach notification within 72 hours. In practice, that means weak cybersecurity controls can become regulatory violations with significant financial and operational consequences.
Does GDPR require encryption?
GDPR does not universally mandate encryption, but Article 32 specifically lists encryption as a recommended security measure. In practice, regulators strongly expect encryption for sensitive personal data because encrypted data may reduce breach notification obligations and lower regulatory penalties if a breach occurs.
Final Remarks
GDPR, at this point, has become a broader security and governance framework that expects organizations to apply risk-based technical and organizational controls across the entire data lifecycle.
In practical terms, that means you need clear visibility into where personal data exists, who can access it, how it moves between systems, and what controls are protecting it.
This includes implementing encryption, enforcing least-privilege access, monitoring for unauthorized activity, maintaining breach response capabilities, securing third-party data flows, and documenting major processing decisions through DPIAs, RoPAs, and governance procedures.
And as AI systems become more embedded into business operations, those responsibilities are expanding beyond traditional privacy compliance into areas like model governance, automated decision-making oversight, and cross-border data risk management.
The organizations that choose compliance as non-negotiable are not treating GDPR cybersecurity as a standalone compliance checklist. Instead, they are aligning GDPR with frameworks like NIST CSF, ISO 27001, SOC 2, and emerging AI governance requirements to build a unified security and compliance posture that can scale across teams, systems, and jurisdictions.
If your organization is trying to manage GDPR alongside frameworks like ISO 27001, SOC 2, HIPAA, or the EU AI Act, we help simplify that overlap through practical cross-framework compliance implementation. Get in touch with our compliance experts!







